Hardware Hacking IoT Device Security For Computer Science Grades 6 9

Hardware Hacking & IoT Device Security For Computer Science | Grades 6-9

Hardware Hacking & IoT Device Security For Computer Science | Grades 6-9

Grade 9 Computer Science Unit 6 Computer Security & Ethics - YouTube

Top 12 Resources for IoT Security and Hardware Hacking | by Vulfosec ...

The Cybersecurity and Computer Science Master Collection for Grades 6-12

Best Practices For IoT Device Security

Exploring Hardware Hacking as an Approach to IoT Security - Redfox ...
Exploring Hardware Hacking as an Approach to IoT Security - Redfox ...

Exploring Hardware Hacking as an Approach to IoT Security - Redfox ...

Iot Security Best Practices For Beginners – peerdh.com
Advertisement Space (300x250)
Iot Security Best Practices For Beginners – peerdh.com

Beginner's Guide to IoT and Hardware Hacking - Expert Training

Hacking the Hackers: A Deep Dive into IoT Security Protocols

IoT Device Security Concepts and Best Practices - Stridefuture

PPT - IoT Device Security: Best Practices for Enhanced Protection ...

Get Started with Hardware Hacking & UART - TCM Security

Get Started with Hardware Hacking Tools - TCM Security

Hacking IoT Devices: CEH’s Approach to Security | by Gayuuinfocerts ...

Hacking the Hackers: A Deep Dive into IoT Security Protocols

Introduction To IOT Devices Security Issues | PDF | Security | Computer ...
Advertisement Space (336x280)

Bolster Your IoT Hardware Security with Expert Solutions – NIX United
Guide to Hacking the Internet of Things and Learning IoT Security ...

IoT Device Security: Best Practices for Enhanced Protection | PDF
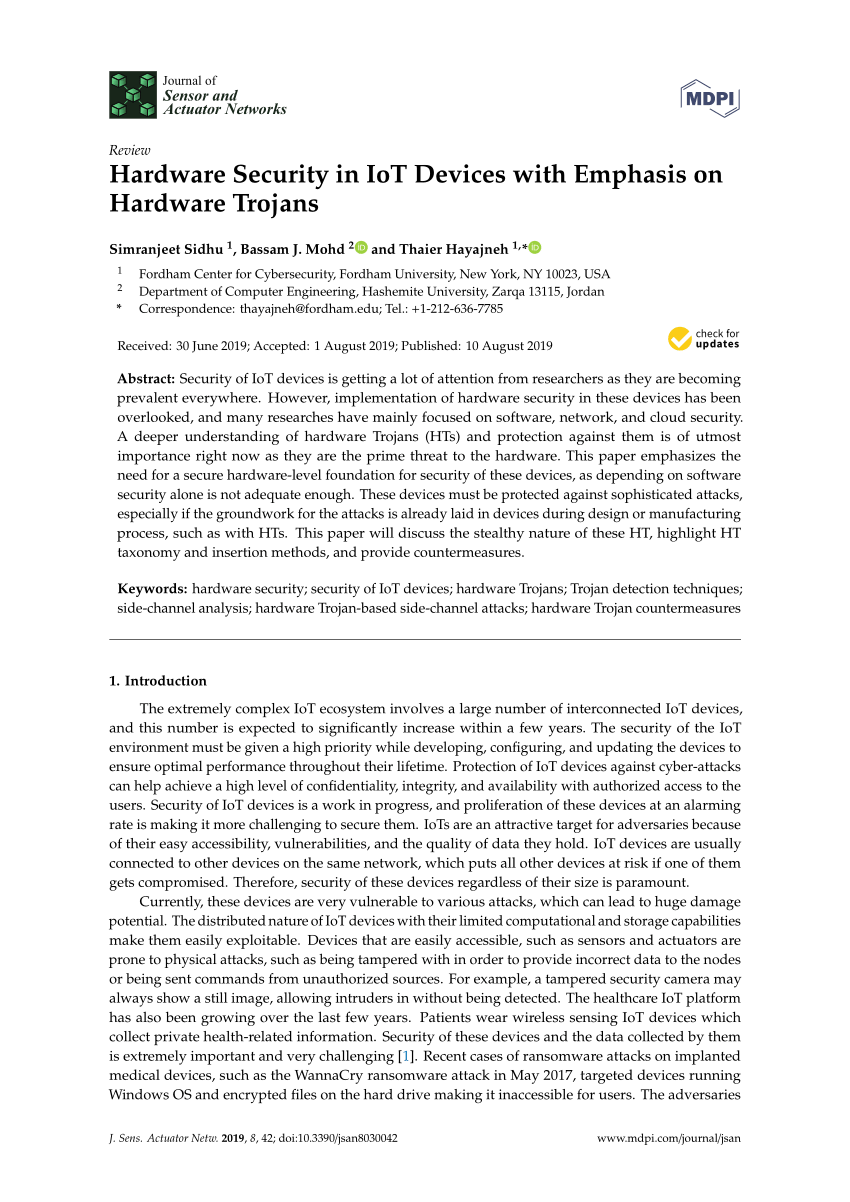
(PDF) Hardware Security in IoT Devices with Emphasis on Hardware Trojans

Beginner's Guide to IoT and Hardware Hacking - Expert Training

(PDF) Enhancing IoT Device Security through Network Attack Data ...

IoT Security Basics Every Device Owner Needs Now

Hacking the Hackers: A Deep Dive into IoT Security Protocols

Learn Computer Hacking and Security From Scratch - Expert Training
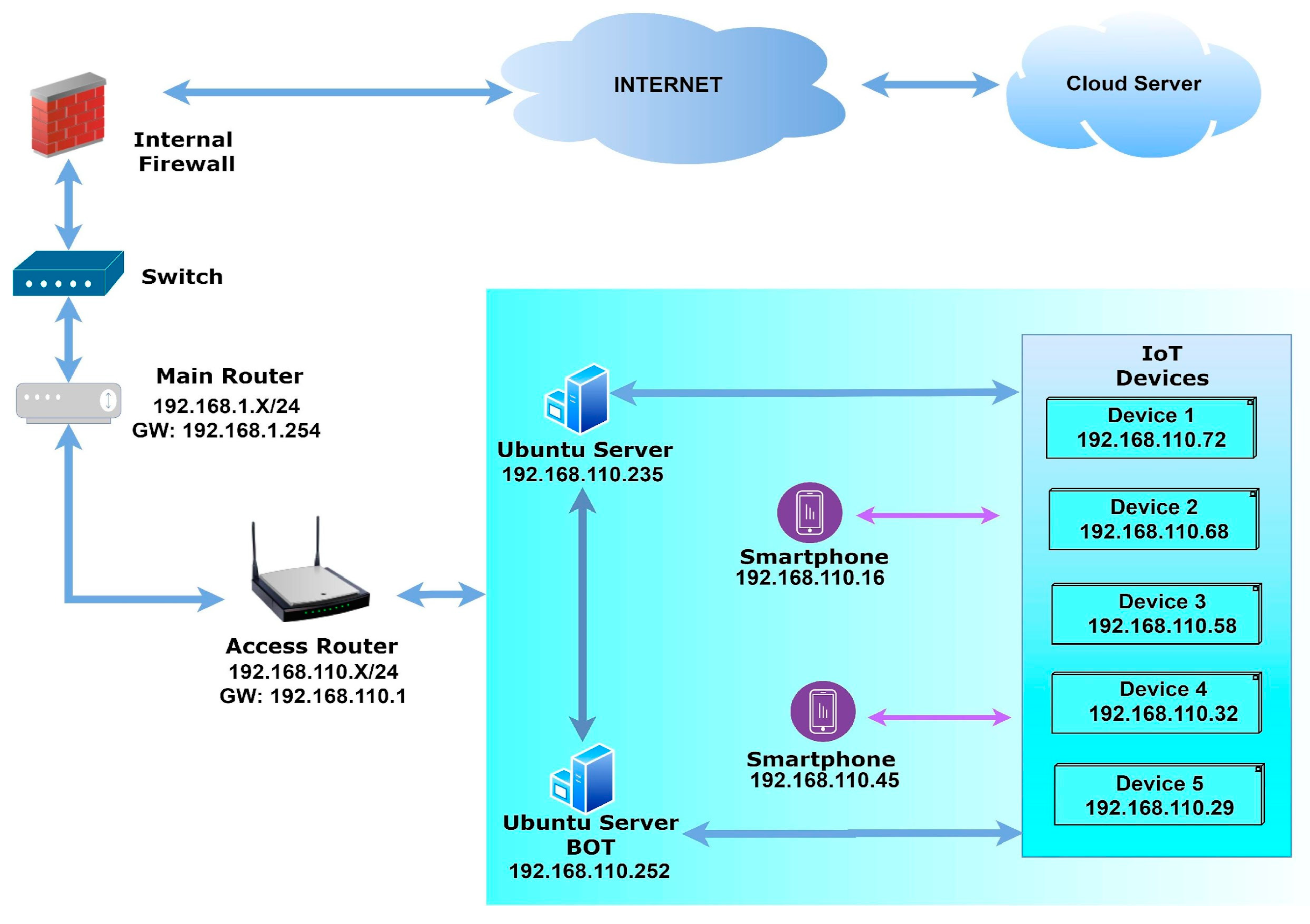
Enhancing IoT Device Security through Network Attack Data Analysis ...
Advertisement Space (336x280)

Unveiling the Ultimate Guide to IoT Device Security

Practical Hardware Hacking Course Overview | PDF | Security Hacker ...
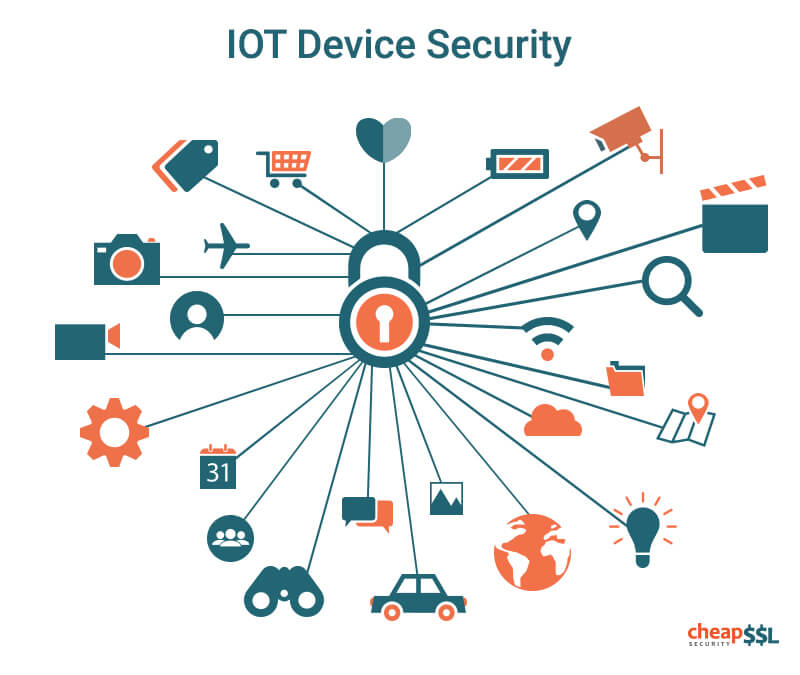
IoT Device Security Explained - Dataconomy

Ultimate Computer Science & Security Bundle: Lessons & Interactive ...

Computer Science - Grade 6 by Uolo - Issuu

A Guide to Hardware Networking and Computer Security | by Innovative ...

Grade 6 ICT (English Medium) - Computer Hardware Lesson Part 1 ...

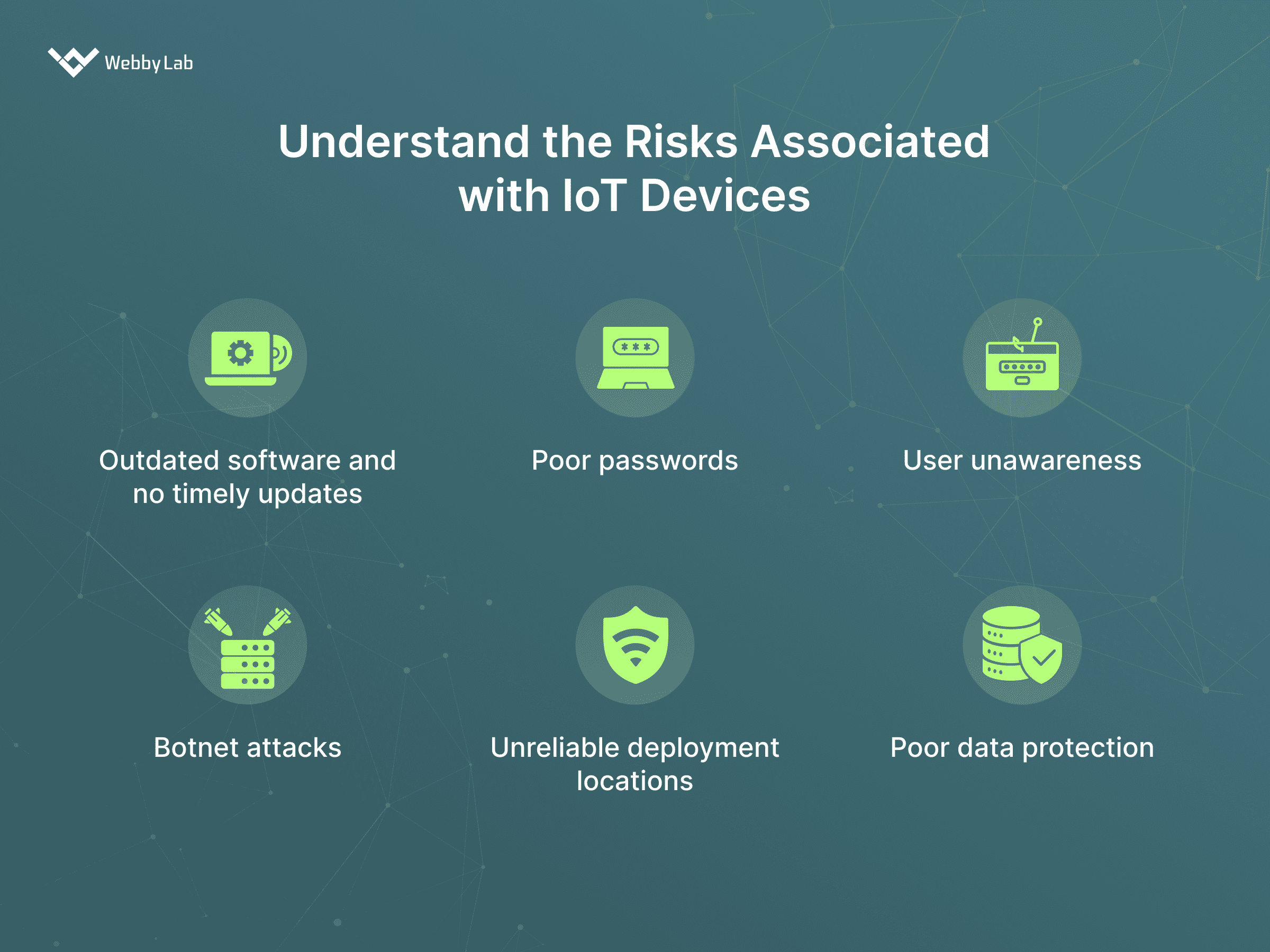
The Biggest Challenges in Ensuring IoT Device Security

Computer Science Classes Grades 4-6 Live Online | Create & Learn

Our newest course is here: Beginner's Guide to IoT and Hardware Hacking ...
Advertisement Space (336x280)

Innovative Solutions to IoT Device Security
Iot Devices Security By Design – New Security Testing Standard For

Computer Science - Grade 6 by Uolo - Issuu

IoT Hardware Security Measures - TelecomWorld101.com

Innovative Solutions to IoT Device Security - Leap Forward

COMPUTER SECURITY AND ETHICS | CH-6 |GRADE 9 | EXERCISE SOLVED ...

IoT Device Security from Ransomware Attacks:

Analyzing Firmware: Hardware Hacking Part 3 - TCM Security
IoT Device Security | Asimily

Hacking Devices for Professionals Archives - Hackzone Cyber Security Blog
Advertisement Space (336x280)
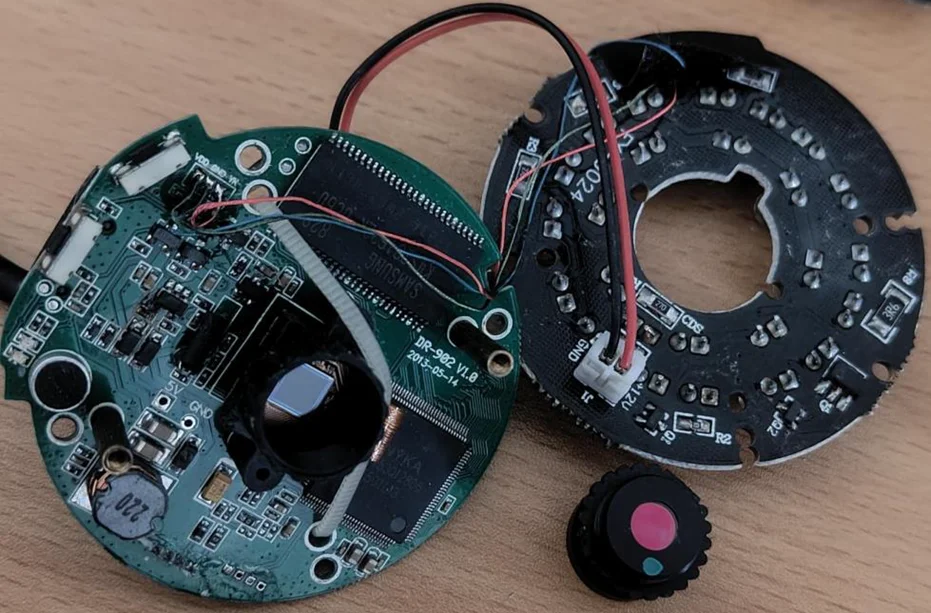
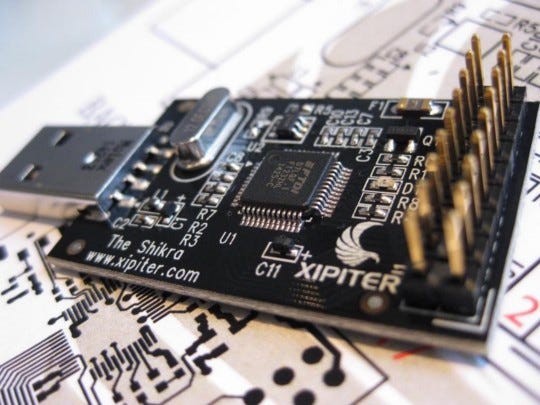
Leveraging Hardware Hacking Tools for Unveiling Vulnerabilities in ...

IoT Device Security Explained - Dataconomy
Remotely Hacking IoT Devices: Here’s How It’s Done - Pivot Point Security

Grade 6 Ch 9 Cyber Threats and Security Part 1 - YouTube

Iot Devices Security By Design – New Security Testing Standard For

Computer Science - Grade 6 by Uolo - Issuu

Hardware for Securing Wireless IoT Devices - TelecomWorld101.com
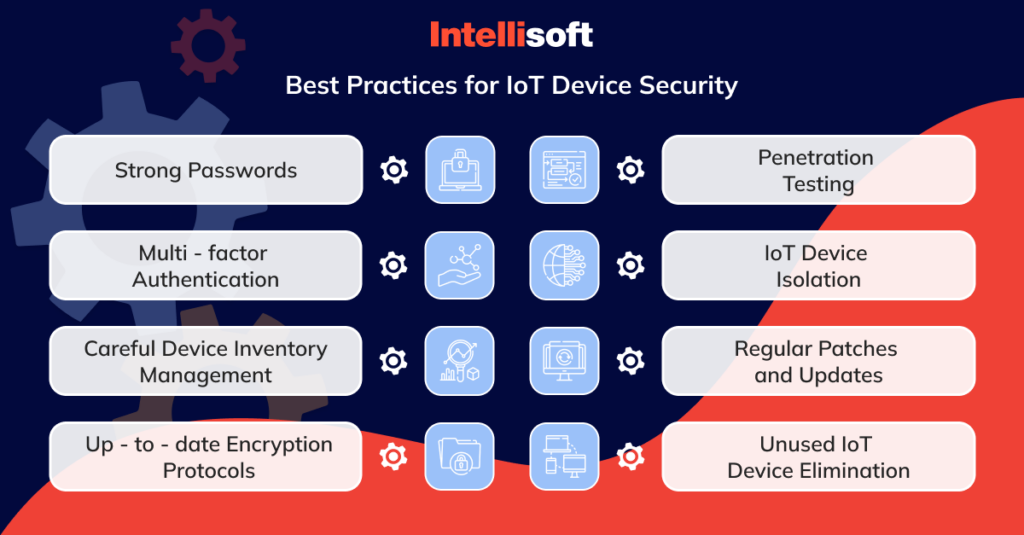
IoT Cybersecurity Essentials: IntelliSoft IoT Security Solutions

The Importance of Security in IoT Hardware: Best Practices and Solutions
Iot Security Devices Examples at Robert Sandoval blog
Advertisement Space (336x280)
A Comprehensive Guide to IoT Security

Hardware Hacking – Hardware Hacking Courses

IoT Hackers Handbook: An Ultimate Guide to Hacking the Internet of ...

IoT Hacking: Vulnerabilities and Security Best Practices By ...

Major Security Threats in IoT Devices: What You Need to Know

IoT Security

Remotely Hacking IoT Devices: Here’s How
Hacking IoT Devices

Iot Security Topics at Kevin Blankenship blog

Cyber security | Grade 6 | Theme 2 - Lesson 4 | ICT - YouTube
IoT Security Threats and Solutions

Cyber security - Grade 6 - Theme 2 - Lesson 4 - ICT - YouTube

Establishing A “Security First” Approach for IoT Devices No Matter the ...

IoT Security using Machine Learning Topics

Things to know about the security of IoT-connected devices | IoT Now ...

IoT SECURITY LEARNING KIT | DIY Hand-on Tools | UART, ZigBee, Arduino ...

IoT Cybersecurity Essentials: IntelliSoft IoT Security Solutions

Grade 6 - ICT - Software & Hardware devices - YouTube

Computer Viruses & Cyber Safety – Interactive Pack Grades 6–9 | WORKBOOK

10 Steps to Improve Security of IoT Devices - Bannari Amman Institute ...
The Hardware Hacking Handbook | No Starch Press
An Introduction to Hardware Hacking
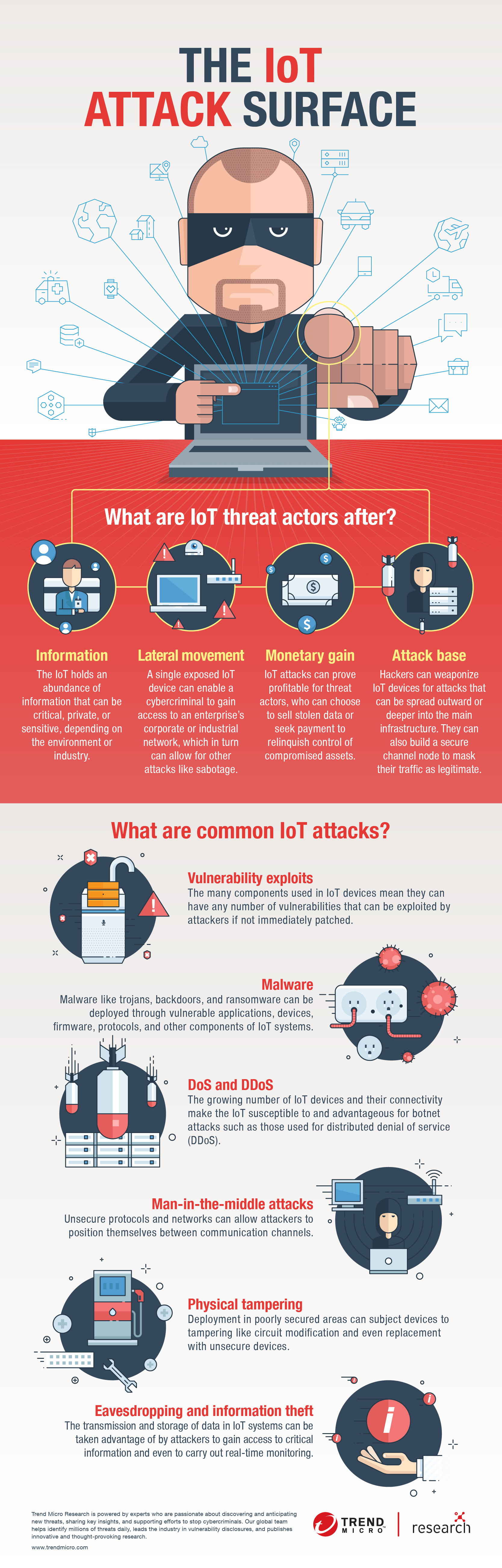
The IoT Attack Surface: Threats and Security Solutions - Security News
IoT Hacking - Course Cloud

3 IoT Security Vulnerabilities To Be Aware Of

Grade 6 ICT - ආරක්ෂිතව පරිගණක විද්යාගාරය භාවිතය - Use the Computer ...

Hacking IoT — Lesson 1 — Discovering IoT Devices | i-PRO Products
Hacking Hardware Tools

CapinTech IoT Devices Security Checklist | Download Free PDF | Internet ...

Hacking and Cybersecurity: Grades 6-9 – Summer @ GDS

What Engineering Leaders Need To Know About IoT Security | Very

Computer Viruses & Cyber Safety – Interactive Pack Grades 6–9 | WORKBOOK

Mastering IoT Security: An In-Depth Guide to Securing the Internet of ...

What Is IoT Security? A Complete Overview | Splunk
Steps of Ensure Secure Communication in IoT Devices
TOTW №7: How to keep your IoT devices safe from hackers - Community ...

10 IoT vulnerabilities to be aware of + protection tips - Norton
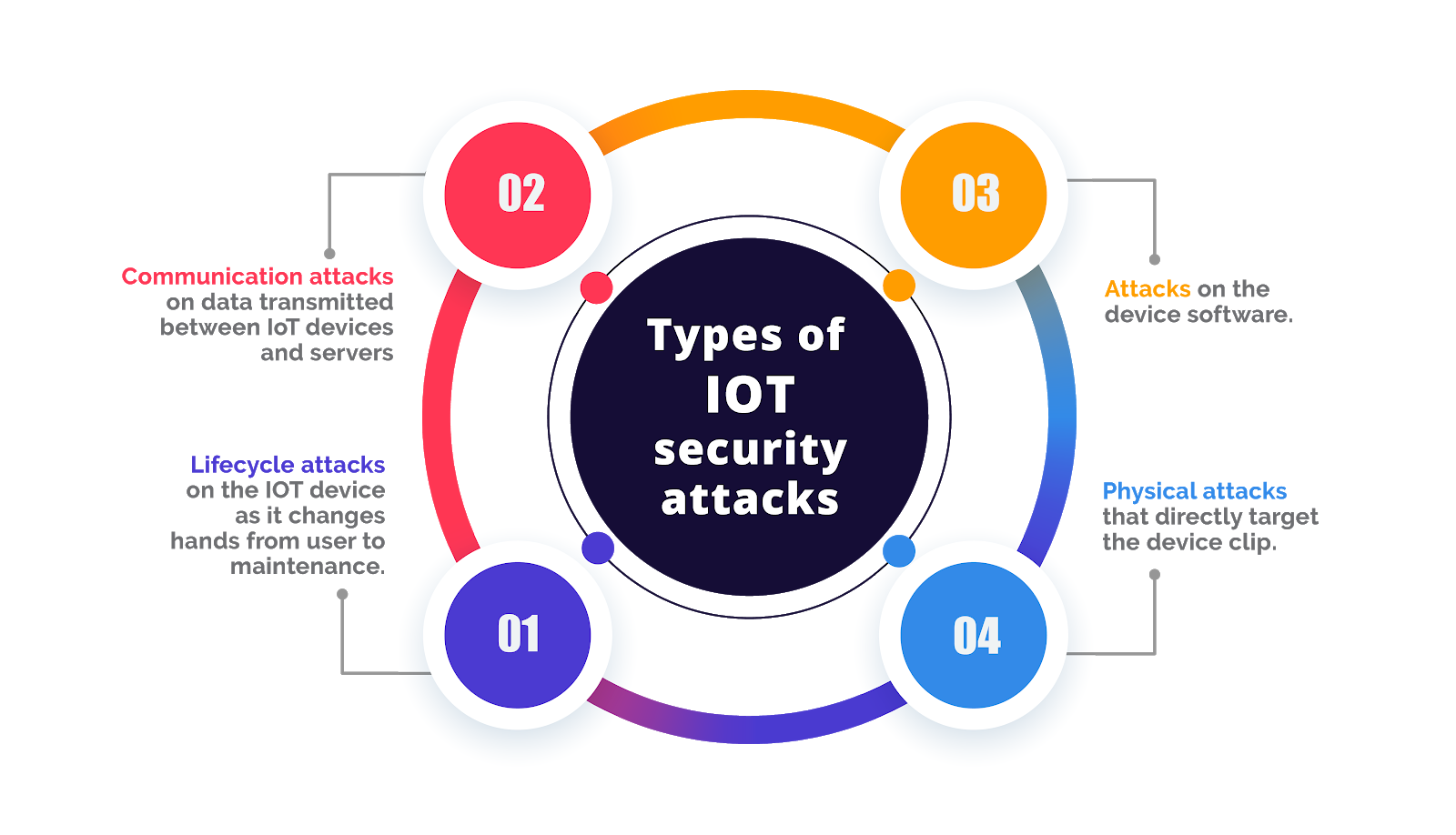
Understanding IoT Hacking: Types, Vulnerabilities, and Countermeasures ...

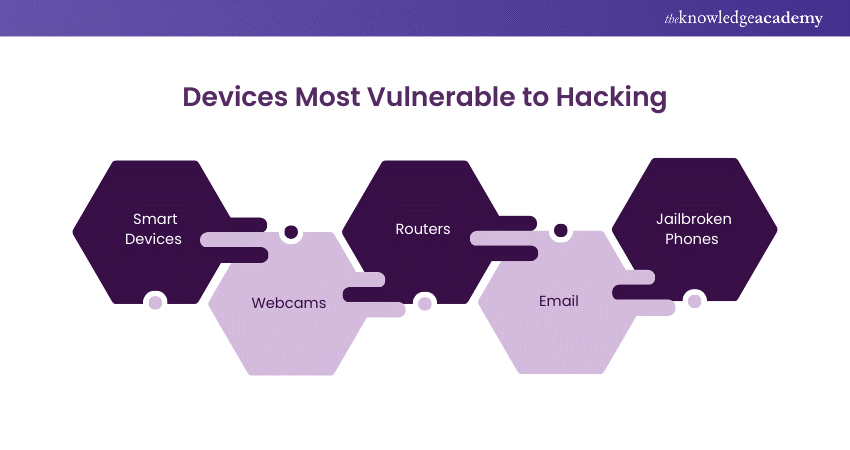
IoT Devices and Cybersecurity Threats - TechVidvan
What are IoT Attacks? Vectors Examples and Prevention.

The Top Vulnerabilities in IoT Devices: What Hackers Target and H

Threats to IoT Devices | TheCyberPatch

The 7 Layers of Cyber Security : Attacks on OSI model
IoT Security: How to Secure Your IoT Devices and Network - IoT Cloud ...

Securing IoT Devices: A Comprehensive Overview of the OWASP Top 10 ...
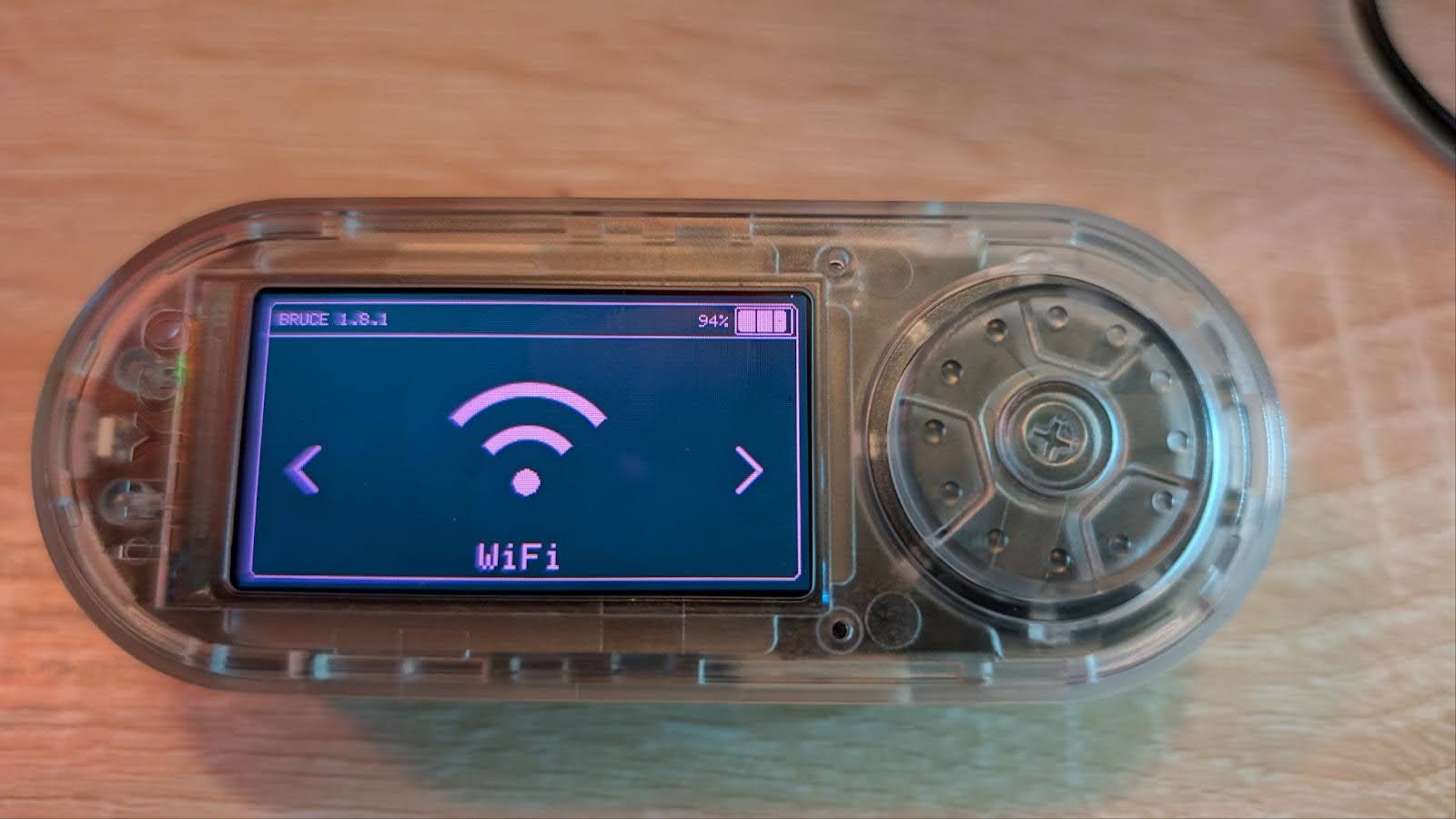
The Explosion of Hardware-Hacking Devices - Security Boulevard

The Explosion of Hardware-Hacking Devices - Security Boulevard

IoT Security: How to Protect Your Smart Devices from Hackers - TechSouls

Cyber Security on the Edge: Efficient Enabling of Machine Learning on ...
Cyber Safety Class 9 | PPTX

What Is IoT Security? How to Keep IoT Devices Safe

Hardware | Hackaday

Staying Safe Online – Cybersecurity Skills Pack Grades 6–9 | WORKBOOK

Top 10 Hacking Devices Used in the Field of Ethical Hacking
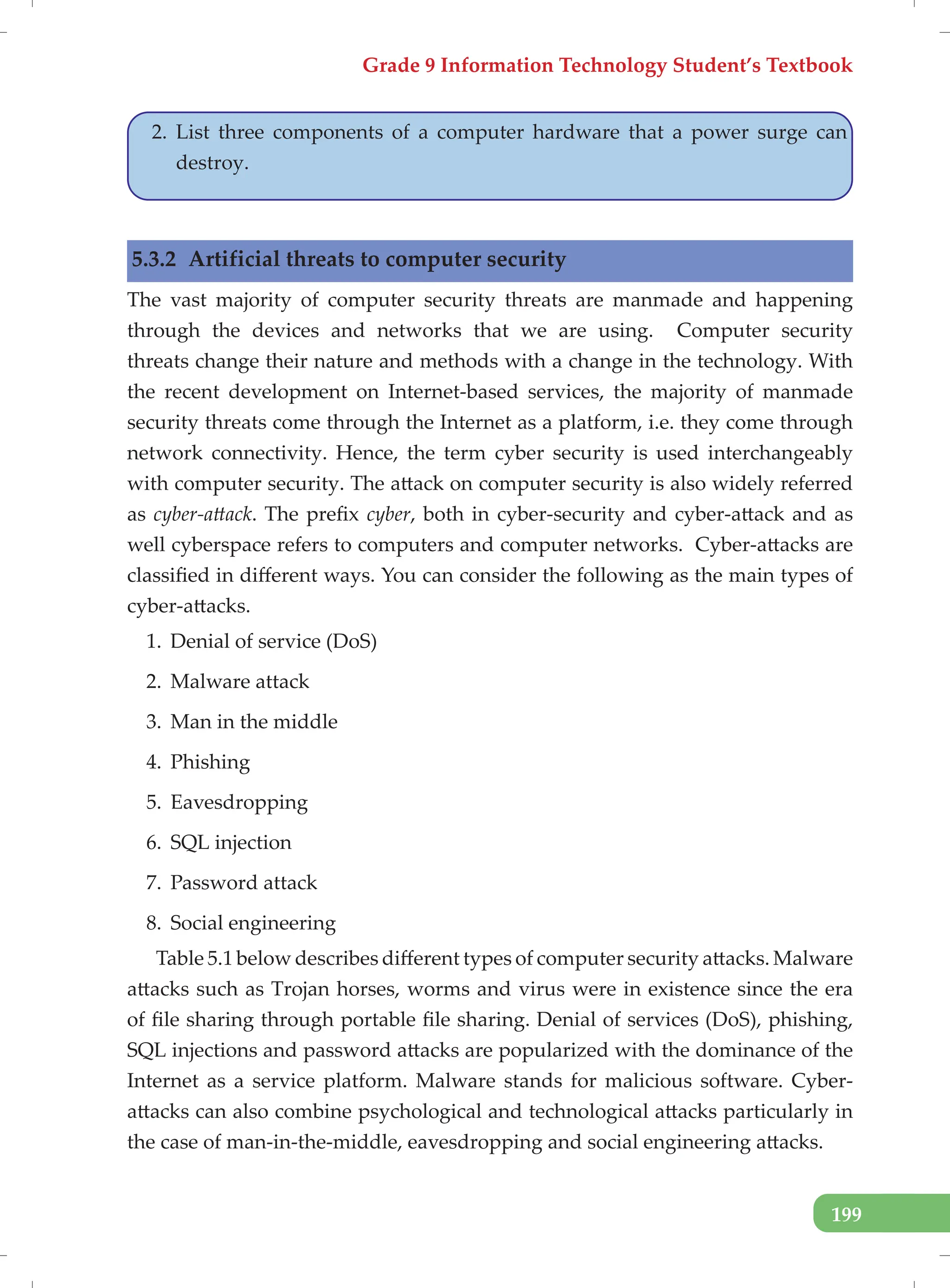
Grade 9-Textbook new IT-STB-2023-web.pdf

IoT-Device-Security-DRAFT-slide-presentation | PPTX

IGCSE_Computer_Science_Grade_9_Enhanced.pptx
What is Hacking? Protect Yourself from Cyber Threats
IoT-Device-Security-DRAFT-slide-presentation | PPTX
Grade 9-Textbook new IT-STB-2023-web.pdf
