Escape Room Computer Science Cybersecurity MiTM Intercept the Attack

Escape Room | Computer Science | Cybersecurity | MiTM Intercept the Attack

Digital Escape Room | Computer Science |Cybersecurity |MiTM Intercept ...

Digital Escape Room | Computer Science | Cybersecurity | Bundle | 1 Week

Digital Escape Room | Computer Science | STEM | Cybersecurity ...

Digital Escape Room | Computer Science | Cybersecurity | Bundle | 1 Week

Premium Escape Room | Computer Science | Cybersecurity | Digital ...

Premium Escape Room | Computer Science | Cybersecurity | Digital ...

Escape Room | Computer Science | STEM | Cybersecurity | Compromised PC

Escape Room | Computer Science | STEM | Cybersecurity | Network Outage
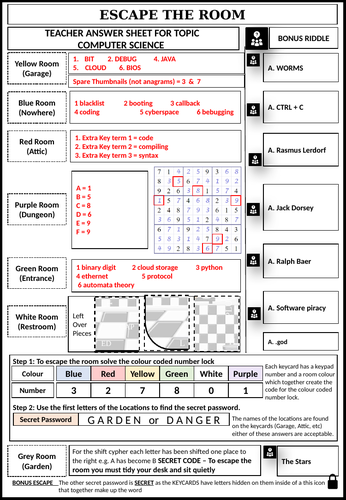
Computer Science Escape Room | Teaching Resources
Advertisement Space (300x250)

Cybersecurity Escape Room by Cre8tive Resources | TPT

An Educational Escape Room Game To Develop Cyberse | PDF | Computer ...

Cybersecurity Virtual Escape Room
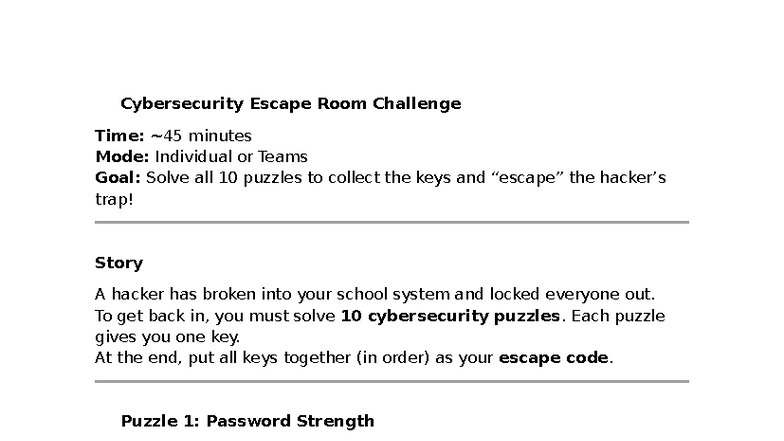
Cybersecurity Escape Room Challenge: Activity 2 Notes - Studocu
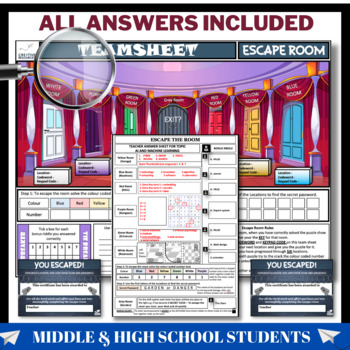
Cybersecurity Escape Room by Cre8tive Resources | TPT
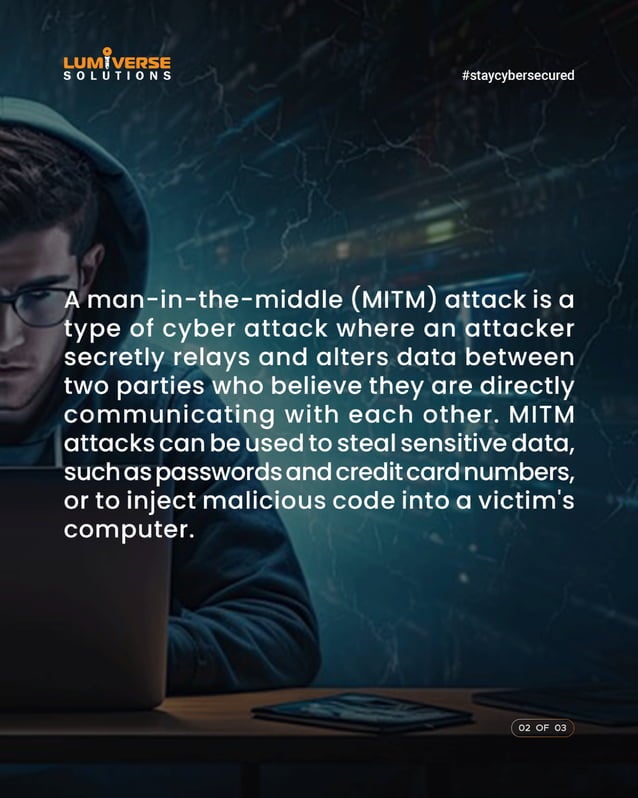
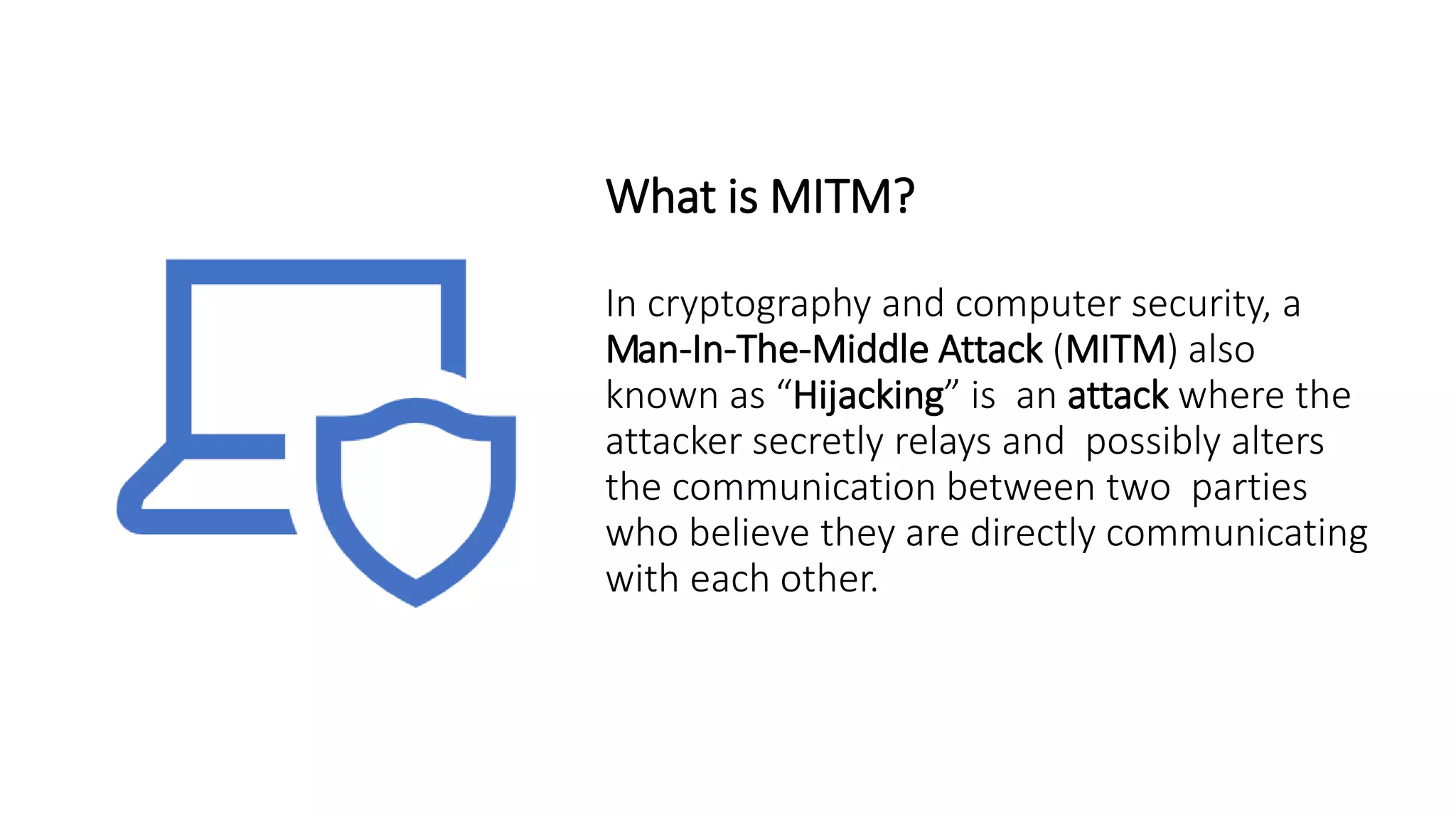
Man In The Middle Attack | MITM Attack | MITM | PDF
Cybersecurity startup to launch interactive escape room game
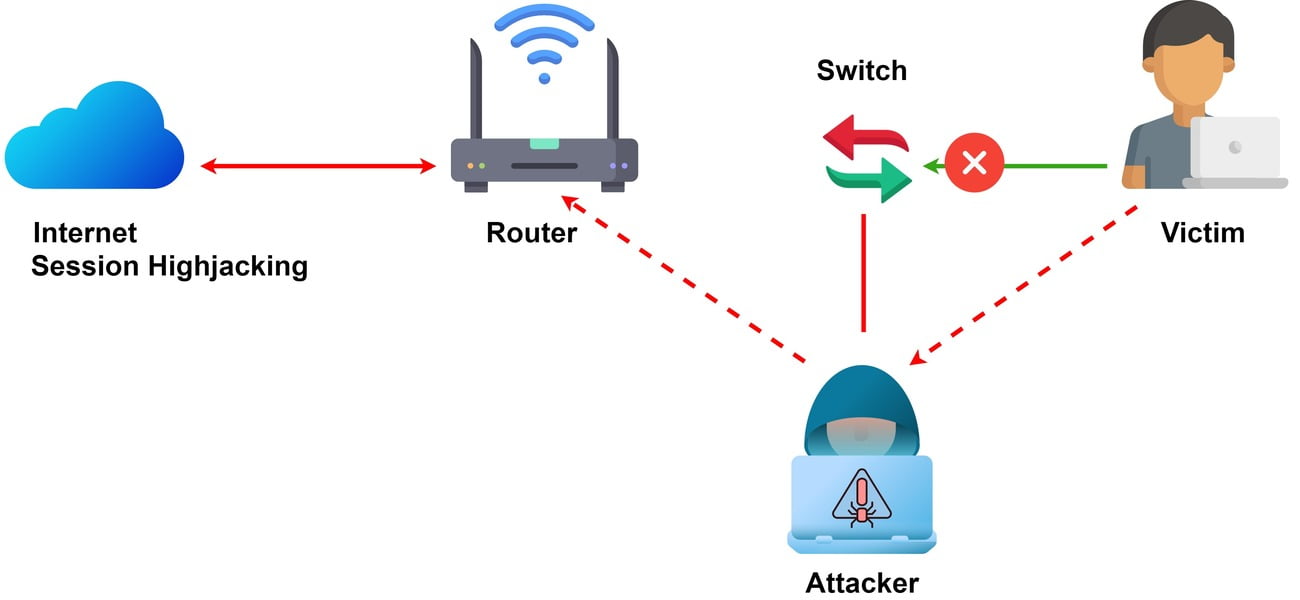
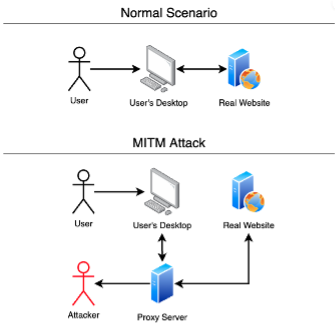
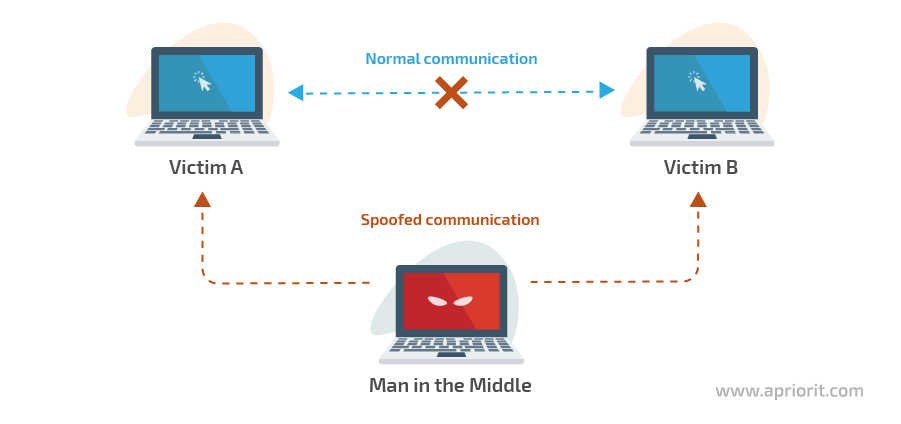
An example of the MITM attack Source: Authors based on the [3 ...

Premium Vector | Mitm attack man in the middle cyberattack active ...

Canadian Cybersecurity Event Enhances Trade Show Training with Escape Room
Advertisement Space (336x280)
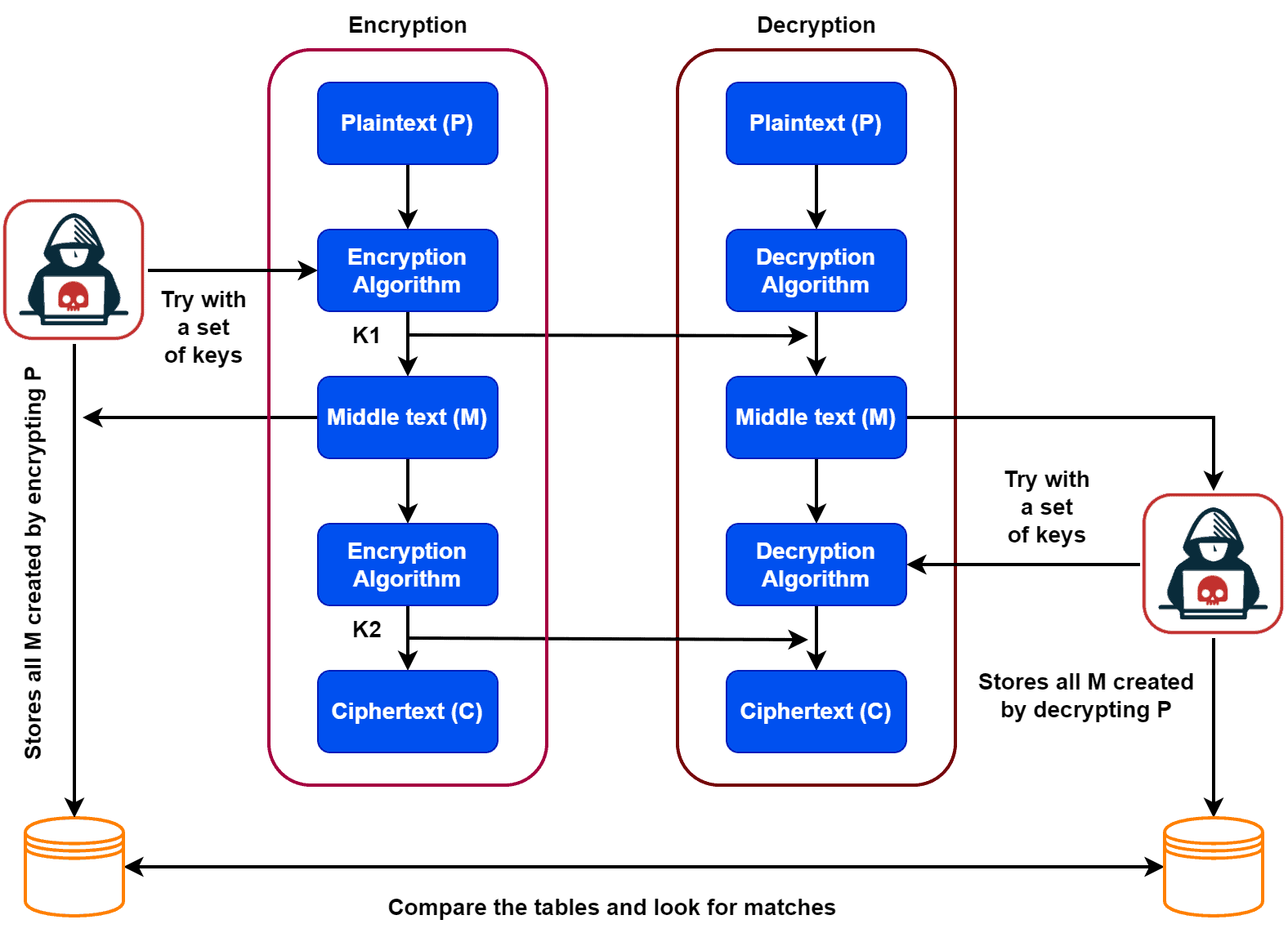
How Does Meet-in-the-Middle Attack Work? | Baeldung on Computer Science

Cybersecurity Games | Cybersecurity Escape Room | Doubleflow

Man In The Middle Attack | MITM Attack | MITM | PDF
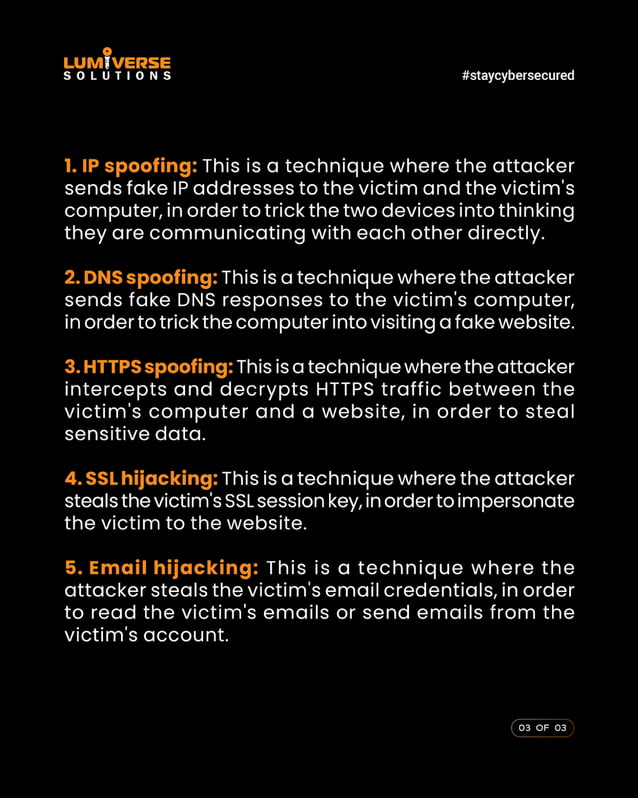
Man In The Middle Attack | MITM Attack | MITM | PDF

Cybersecurity Escape Room | QNP
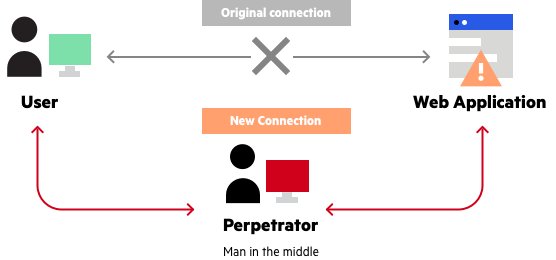
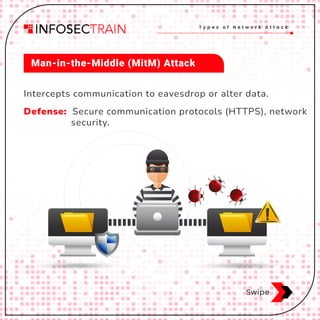
man in the middle mitm attack
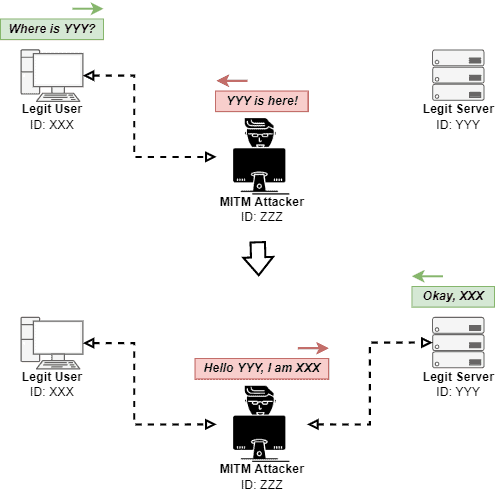
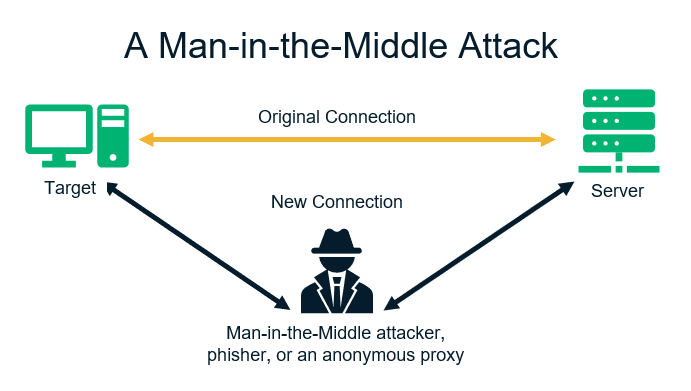
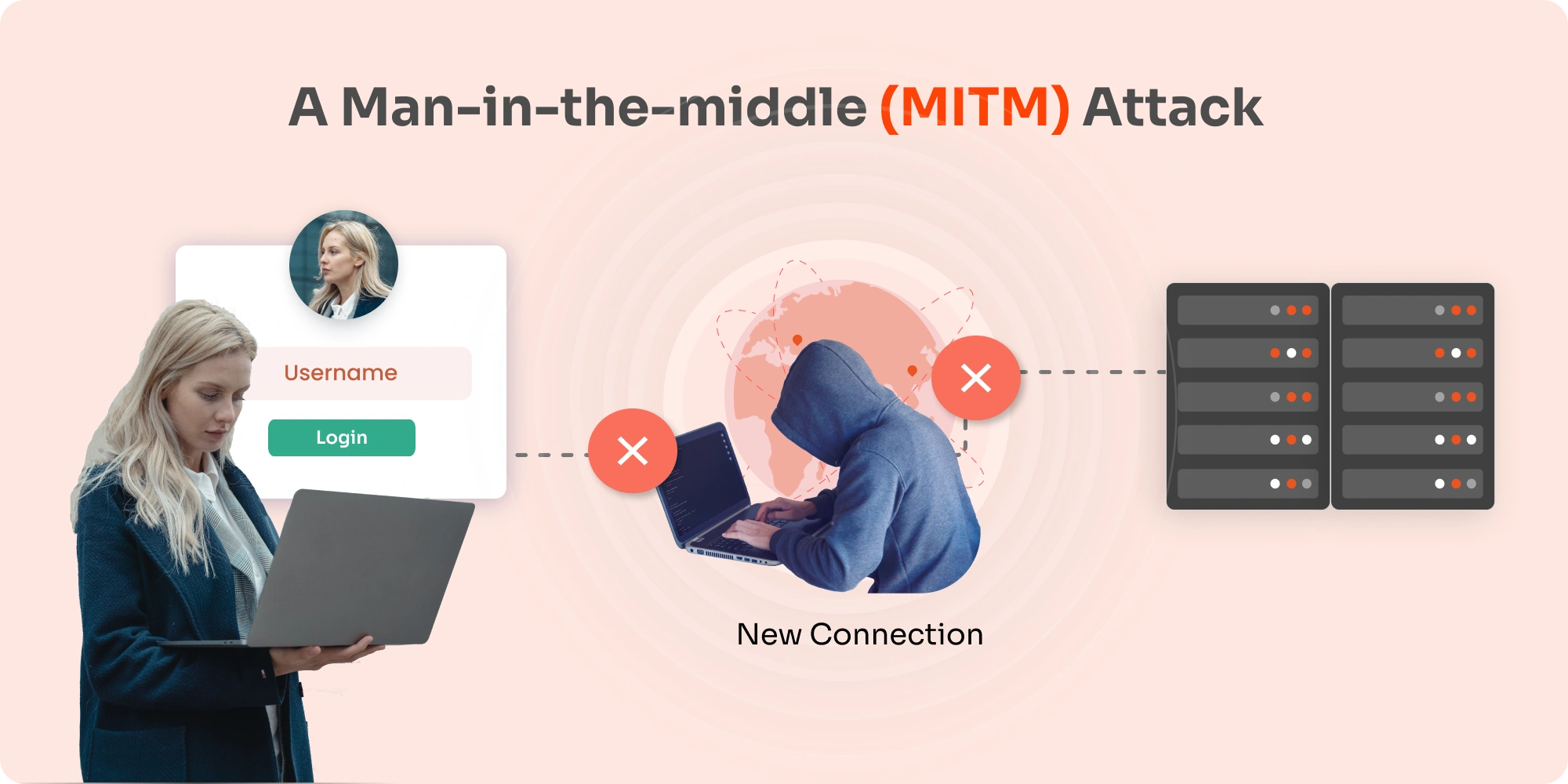
Man in the Middle (MITM) Attacks Explained | Baeldung on Computer Science
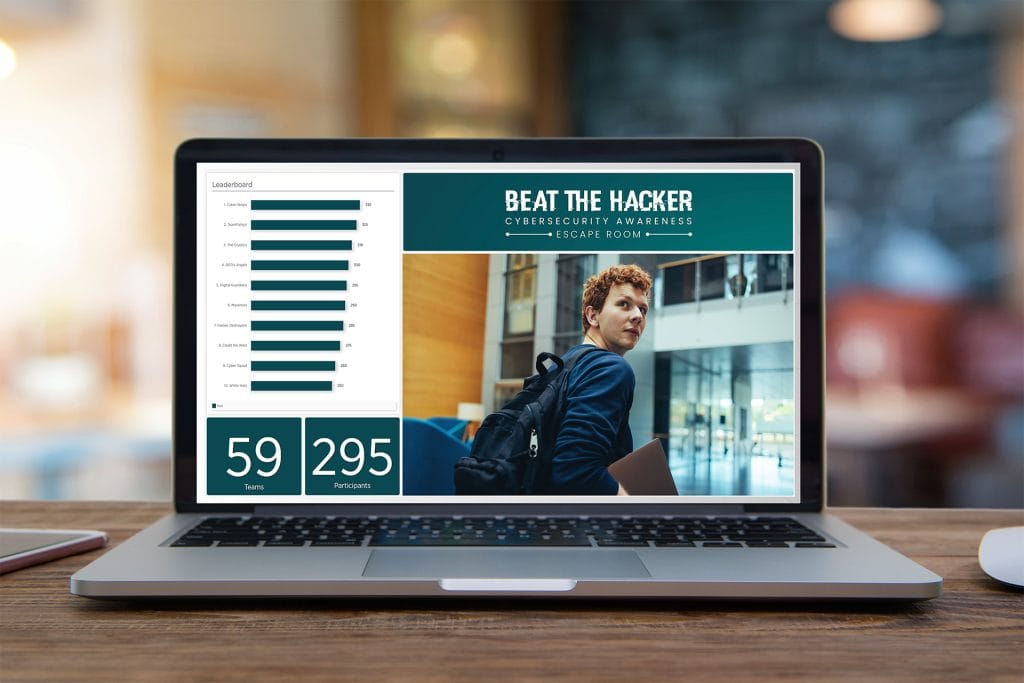
Cybersecurity Escape Room | Awareness Training | Doubleflow

"Decoding Cyber Threats: Unveiling the Innovative Cyber Escape Room ...
The Escape Room: Cybersecurity Training Virtual Experience
Advertisement Space (336x280)
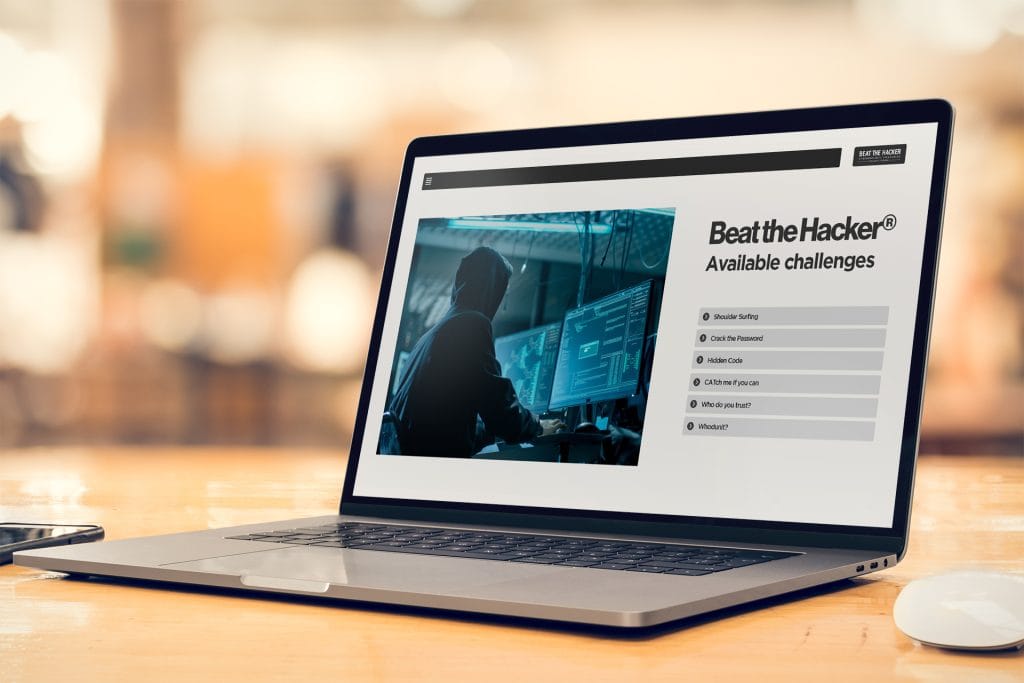
Cybersecurity Escape Room | Awareness Training | Doubleflow

The Cyber Escape Room Co - Blog - The Cyber Escape Room Co.
Cybersecurity Games | Cybersecurity Escape Room | Doubleflow

Cyber Security Escape Room | Teaching Resources

Online Safety and Cyber Security Escape Room | Teaching Resources

Online Safety and Cyber Security Escape Room | Teaching Resources

Cyber Escape Room – CyberCrowd

Cyber Security Escape Room Online
Cyber Security Escape Room Online

Cybersecurity Escape Room-Free Interactive Cybersecurity Learning
Advertisement Space (336x280)

Online Safety and Cyber Security Escape Room | Teaching Resources
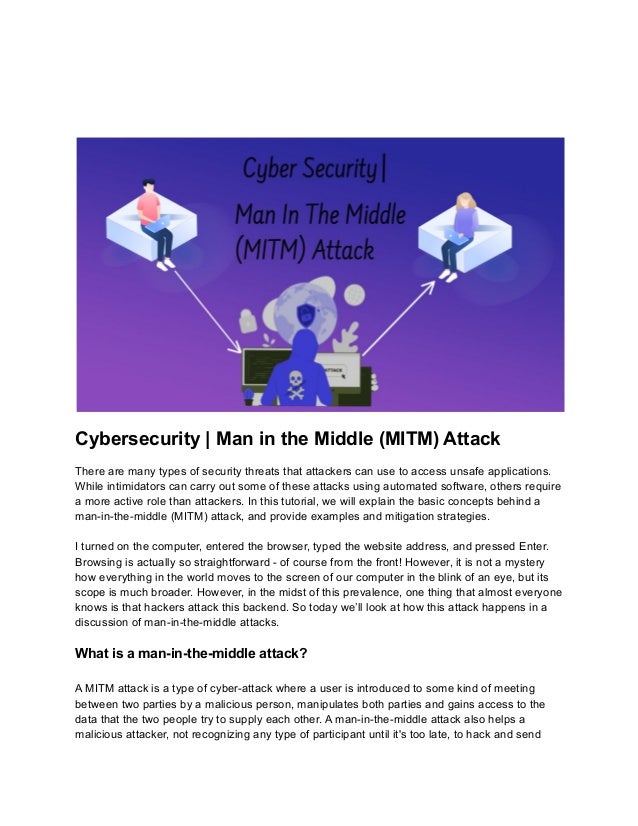
Cybersecurity _ Man in the Middle (MITM) Attack.pdf

Cyber Security Escape Room - Make it Clear

What is a Man in the Middle Attack? MitM Types & Prevention

CGI’s escape room for security training arrives in Edinburgh

Cyber Security Escape Room | Teaching Resources
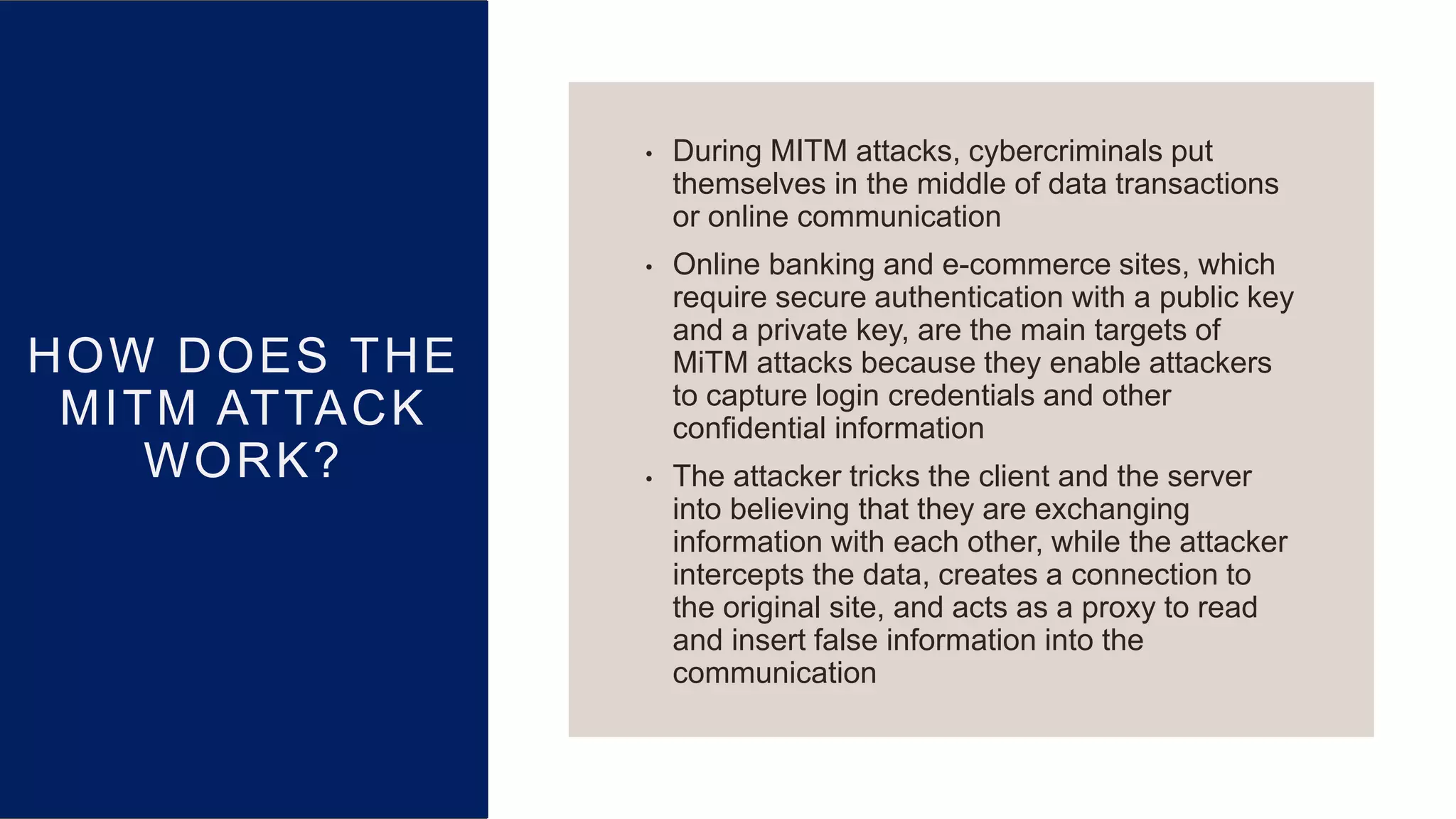
Cybersecurity _ Man in the Middle (MITM) Attack.pptx

What is MITM Attack? in 2025 | Learn computer science, Networking ...
Cyber Security - Escape Room by High School With Hannah | TPT

Computer science - technology Common Core RST.9-10.2 resources | TPT
Advertisement Space (336x280)
Man in the middle attack (mitm) | PPTX

MITM attack technique | Download Scientific Diagram

Northwest Chapter & TCS run Cyber Escape Room & Cyber Crisis Simulation ...
The Anatomy of a Cyber Attack
Security Awareness Information - Man in the Middle (MITM) Attack ...

Cyber Escape Room at GISEC: Test Your Skills

Cyber Escape Room Competition! - Leadership Southern Maryland

What is MITM Attack and How to Prevent from MITM Attack? | 'Monomousumi'

Cyber Escape Room 1

Cyber Escape Room – STEM – San Bernardino County ROP
Advertisement Space (336x280)
Cyber Security Escape Room | Teaching Resources

Cybersecurity _ Man in the Middle (MITM) Attack.pptx

HACKED! Cyber Security Escape Room for companies

Cyber Security Escape Room Training Experience - CyBiz

Escape Room | Cyber Security awareness escape room | København
Applying MITM Tools for Penetration Testing and Cybersecurity ...
Cyber Security Escape Room Creators Expand Team Due to Sweeping Success

What Is a Man in the Middle Attack? MITM Explained
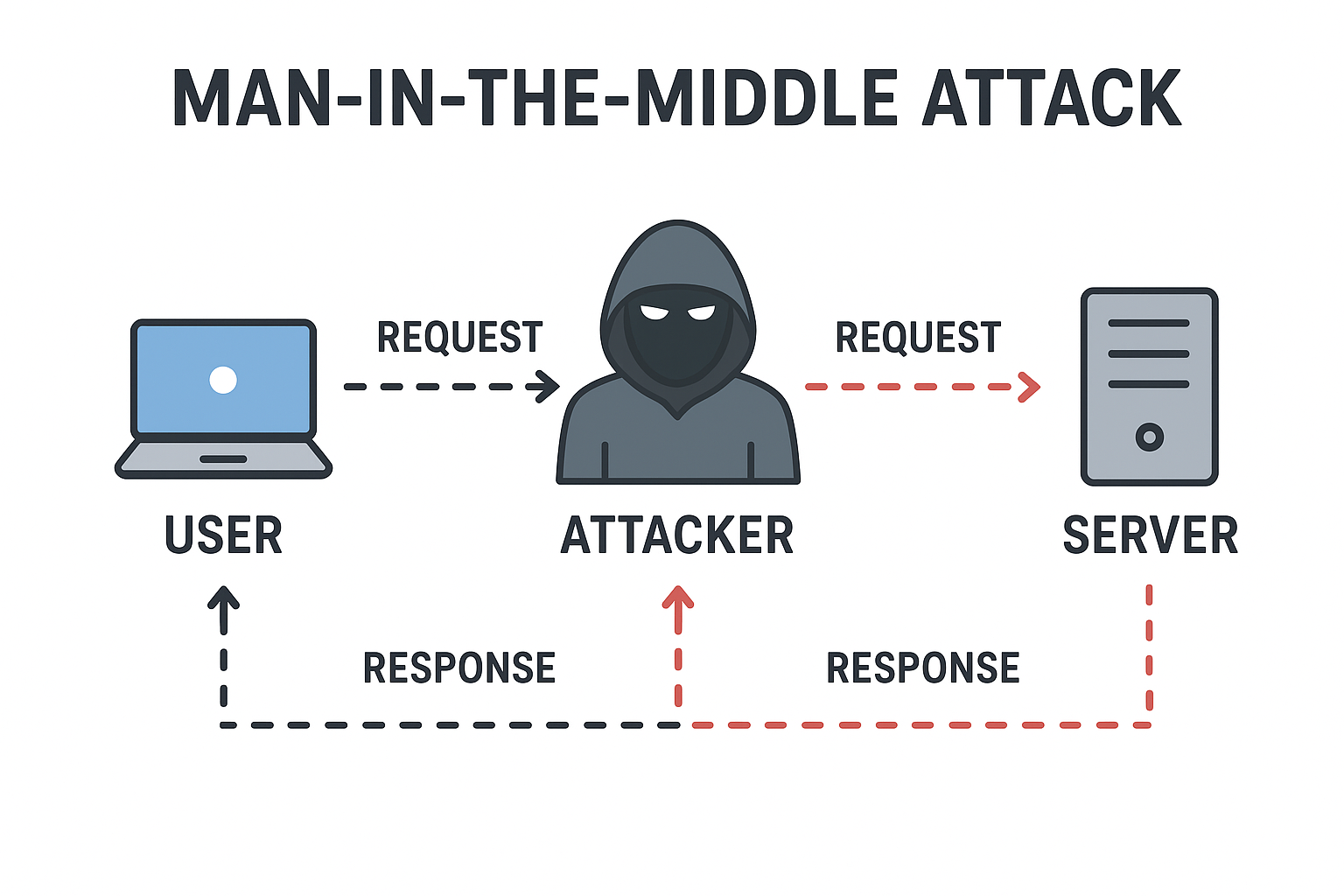
Man-in-the-Middle (MitM) Attack | TestingDocs

What is a cyber security escape room? - Darwin's Data
What is a Cyber Escape Room? A Complete Guide
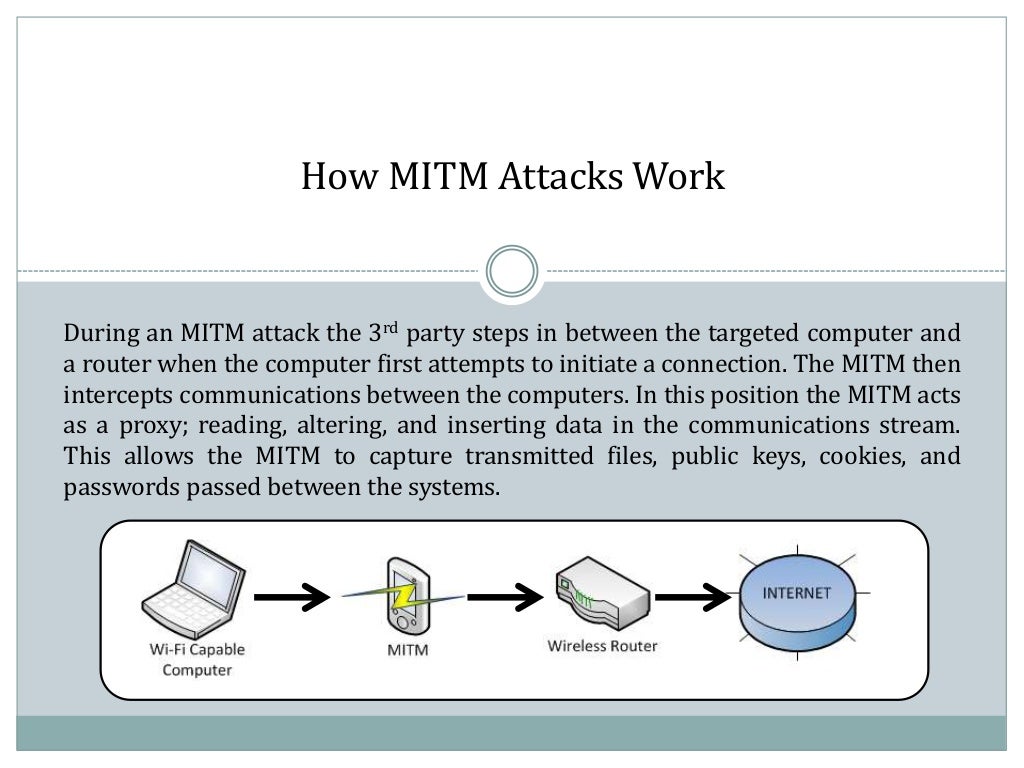
OPSEC - MITM Attacks.pptx

One Step Ahead of Hackers: Mitigating MitM Attacks | Blog

How to Detect and Stop a Man-in-the-Middle (MITM) Attack
%20attack.jpg)
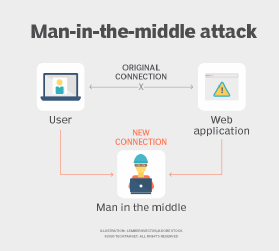
What is Man-in-the-Middle (MitM) Attack? Understanding MitM Attacks
Understanding MITM Attacks | Ascendant

A New Way of Detecting TLS (SSL) MITM Attacks | Enea
What Is a Man-in-the-Middle Attack (MitM)? - Definition from IoTAgenda

Cyber escape rooms: Inside INL’s pioneering training to protect ...

Understanding Man-in-the-Middle (MITM) Attacks in Cybersecurity
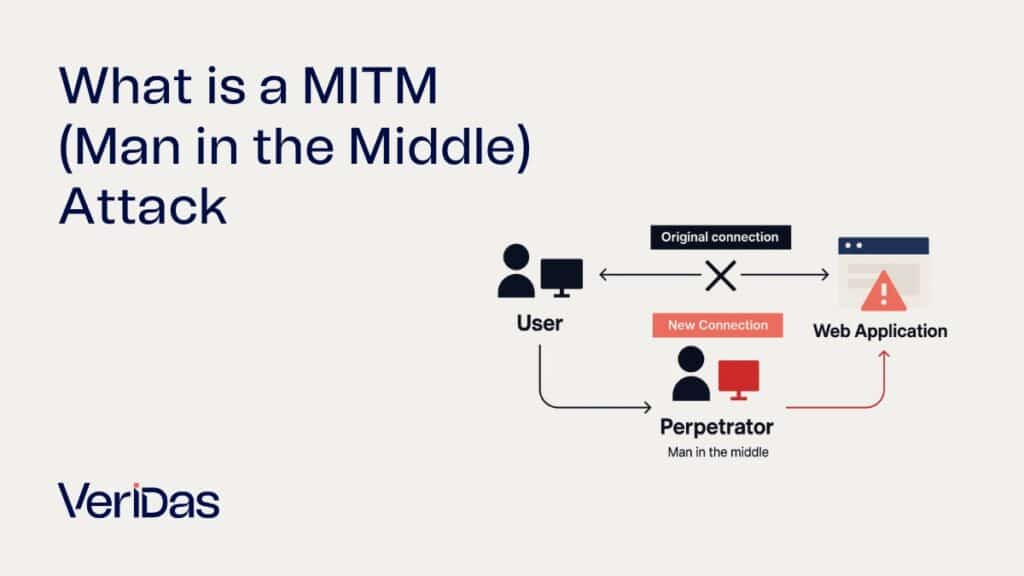
What is a Man-in-the-Middle (MITM) Attack and how to prevent it? • Veridas

Cyber Escape Room: GHOSTBYTE Malware Crisis (Google Forms | STEM for ...

Cyber security escape room, do you dare?

Workshop und Escaperoom Cyber-Sicherheit | Mittelstand-Digital Zentrum ...
10 Different Types of Cyber Attacks & How To Recognize Them - InfoSec ...

Cyber-Security-Escape-Room - Events - Staff Unit Information Security ...

What is a Man-in-the-Middle (MITM) Attack? - CyberGlobal
What is a Man-in-the-Middle (MITM) Attack? Understanding and Preventing ...

Man-in-the-Middle Attacks Explained: How Hackers Steal Your Data
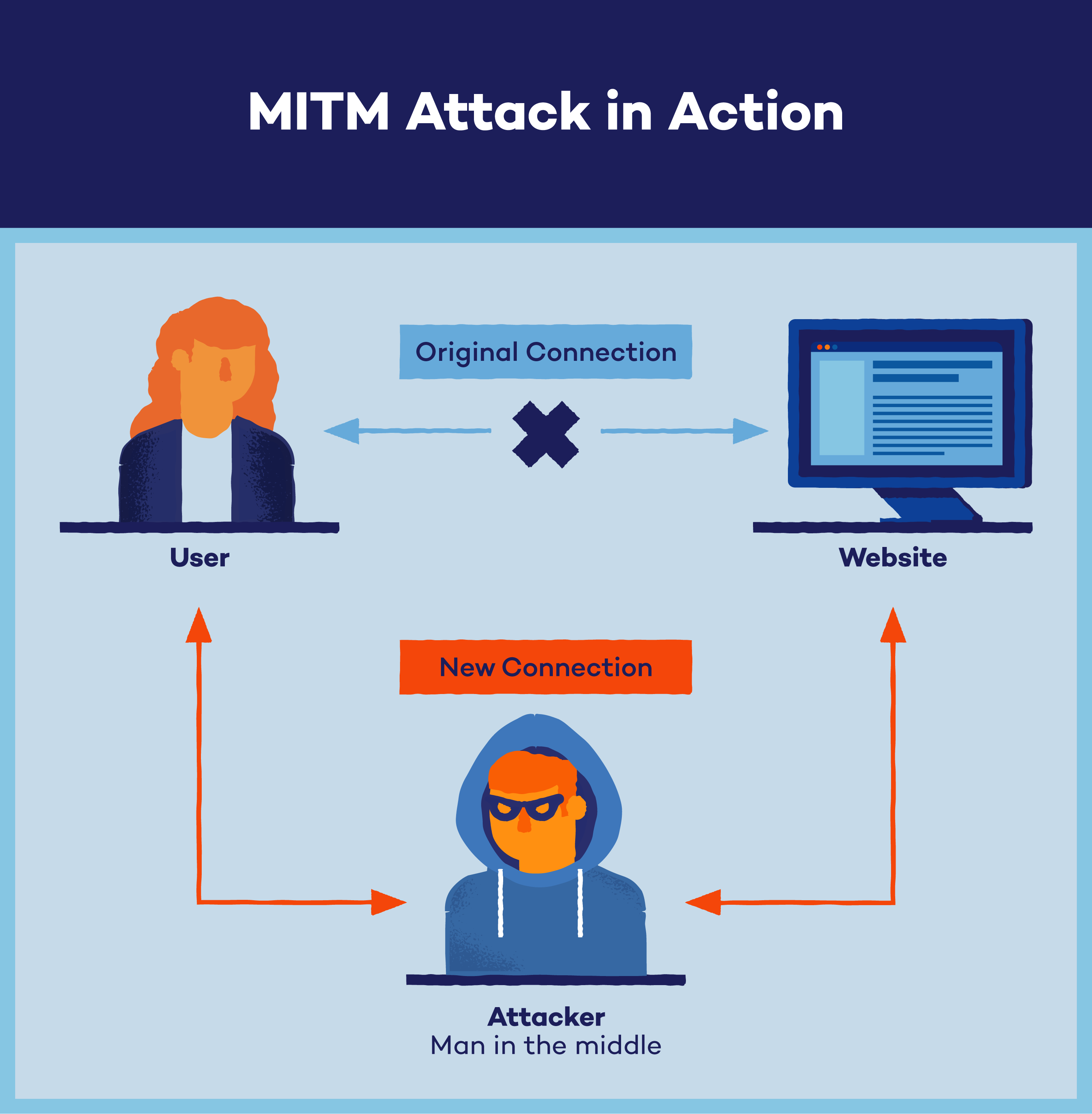
What Is a Man-in-the-Middle Attack? - Panda Security

Avoiding man-in-the-middle (MITM) attacks | Invicti
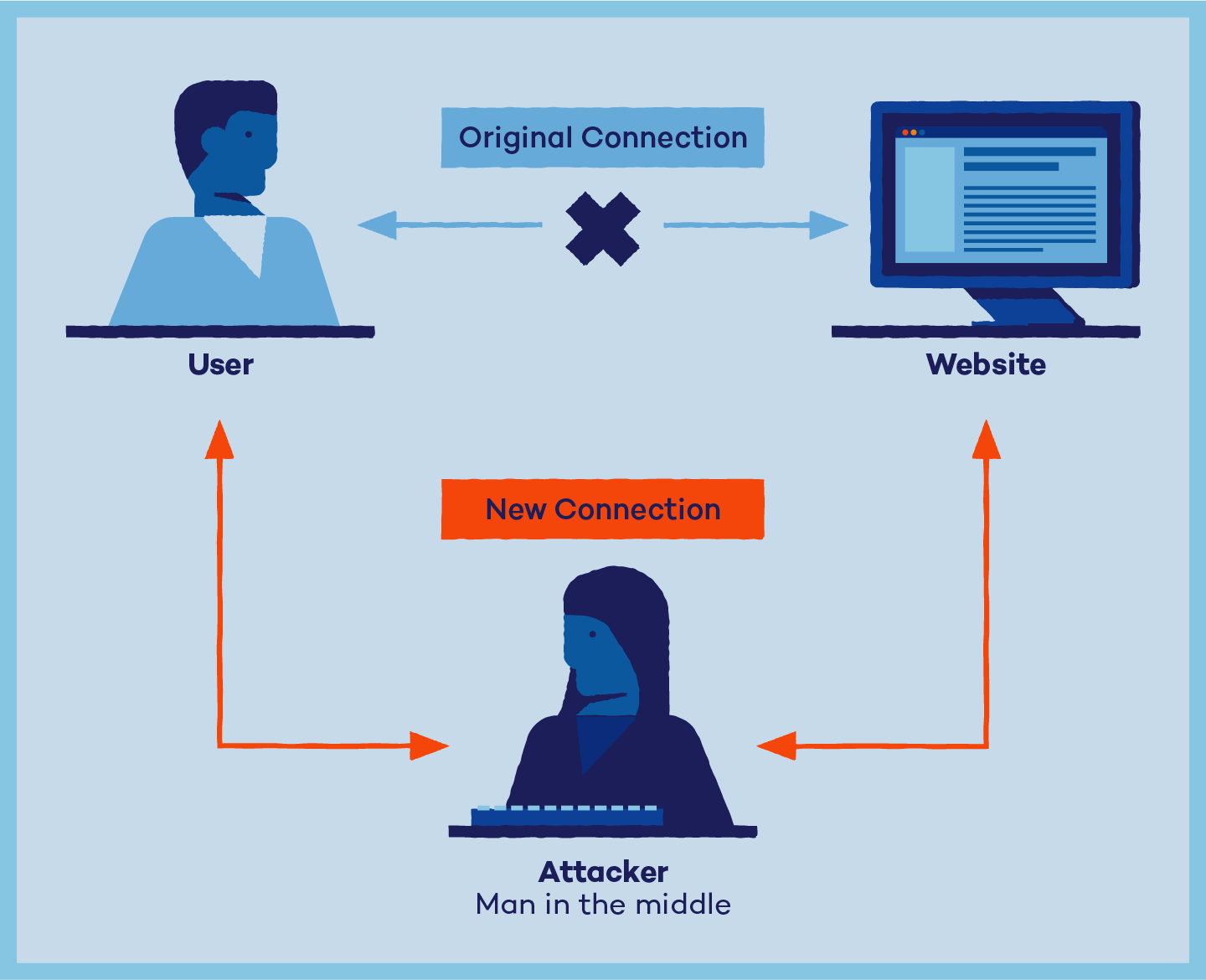
What Is a Man-in-the-Middle (MITM) Attack? Definition and Prevention ...

Understanding and Preventing Man-in-the-Middle (MitM) Cyberattacks ...

Spear‑Phishing, Whale Phishing, MITM: A Beginner’s Guide to Cyber ...
What is Access Provisioning in Identity Management?

Understanding and Mitigating Insider Threats in 2025: A Comprehensive ...
Types Of Network Attacks Safeguard your network against cyber threats | PDF

What Is a Man-in-the-Middle Attack? - Panda Security
cyber security.pptx
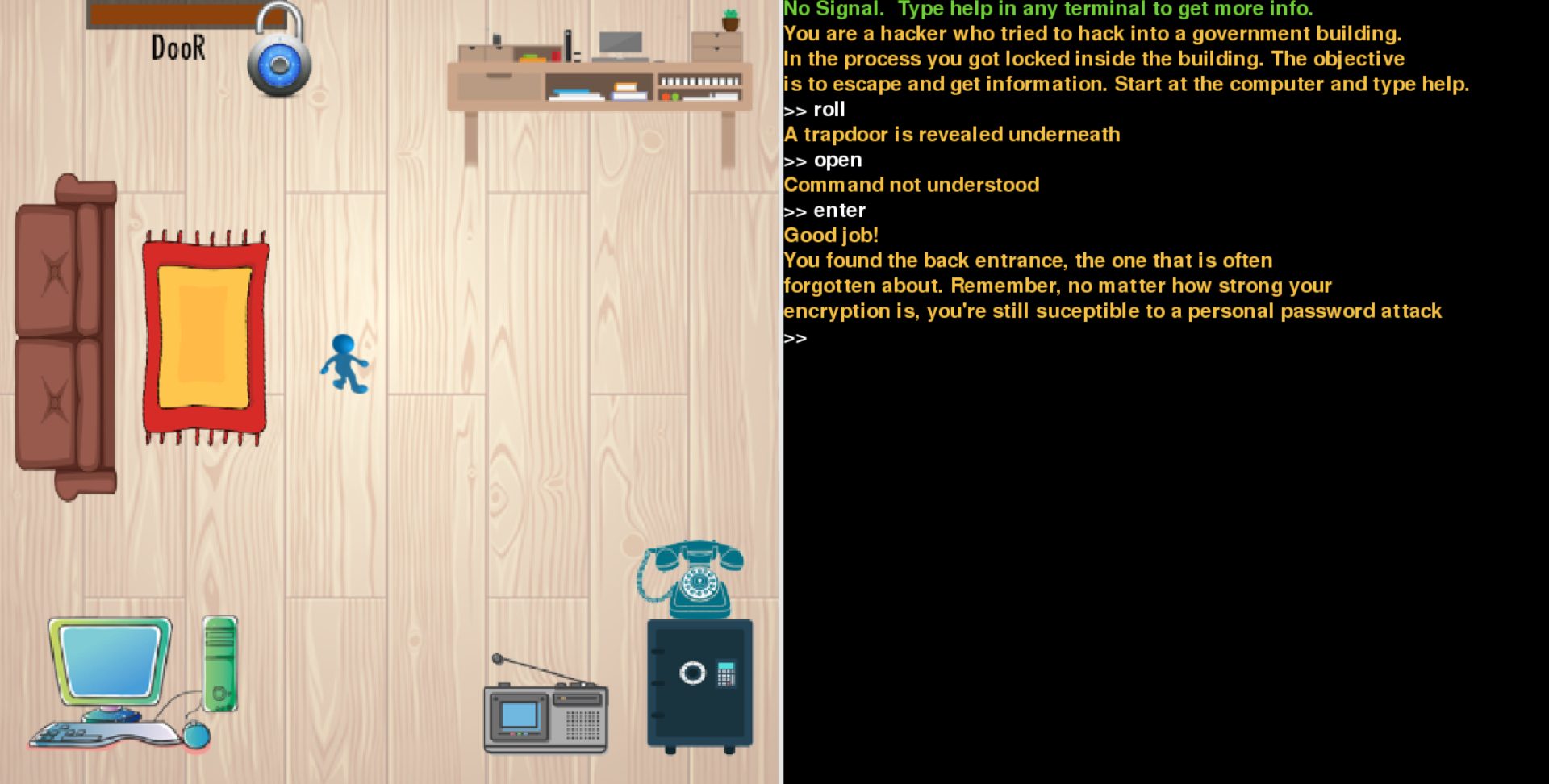
cyber-security-escape-room | Devpost

MOD are doing cyber-security awareness differently – Defence Digital
