Cybersecurity Vulnerabilities Advanced Security Analysis Curriculum L2APPD06

Cybersecurity Vulnerabilities: Advanced Security Analysis Curriculum L2 ...
Cybersecurity Vulnerabilities: Advanced Security Analysis Curriculum L2 ...

Cybersecurity Academy Curriculum | PDF | Computer Security | Security

How to perform a Cybersecurity Vulnerabilities Analysis to Keep Your
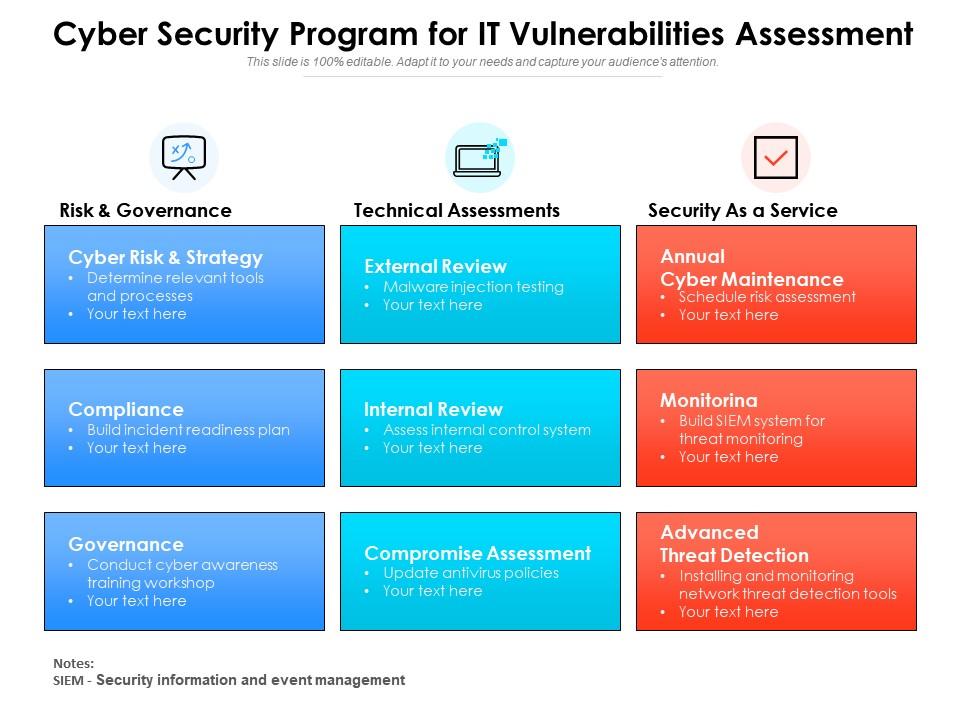
Cyber Security Program For It Vulnerabilities Assessment | Presentation ...
Cyber Security Vulnerability Analysis Checklist PPT Example
10 Most Common Cybersecurity Vulnerabilities | CyberGhost VPN

Cyber Security Vulnerabilities Explained | PDF | Security | Computer ...

Cyber Security Risk Analysis And Control Matrix PPT Presentation

NEW LED Cyber Security Curriculum Compressed | PDF | Computer Security ...
Advertisement Space (300x250)
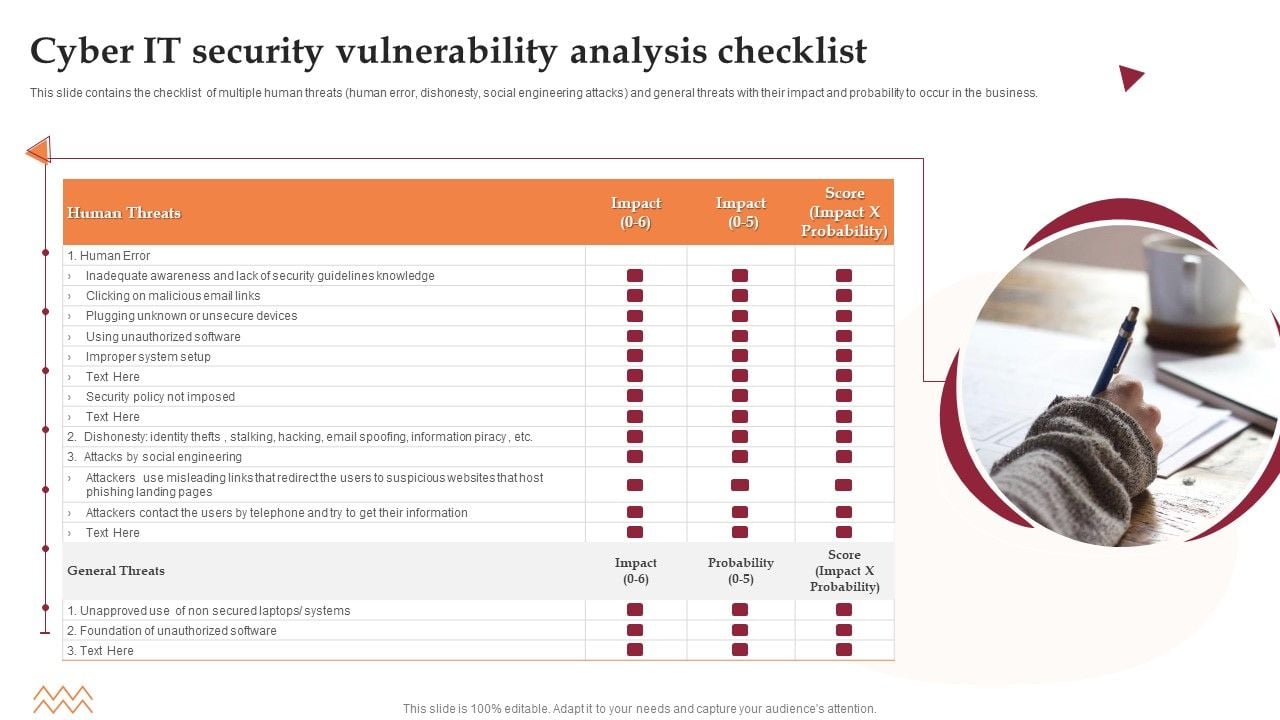
Cyber IT Security Vulnerability Analysis Checklist Microsoft PDF
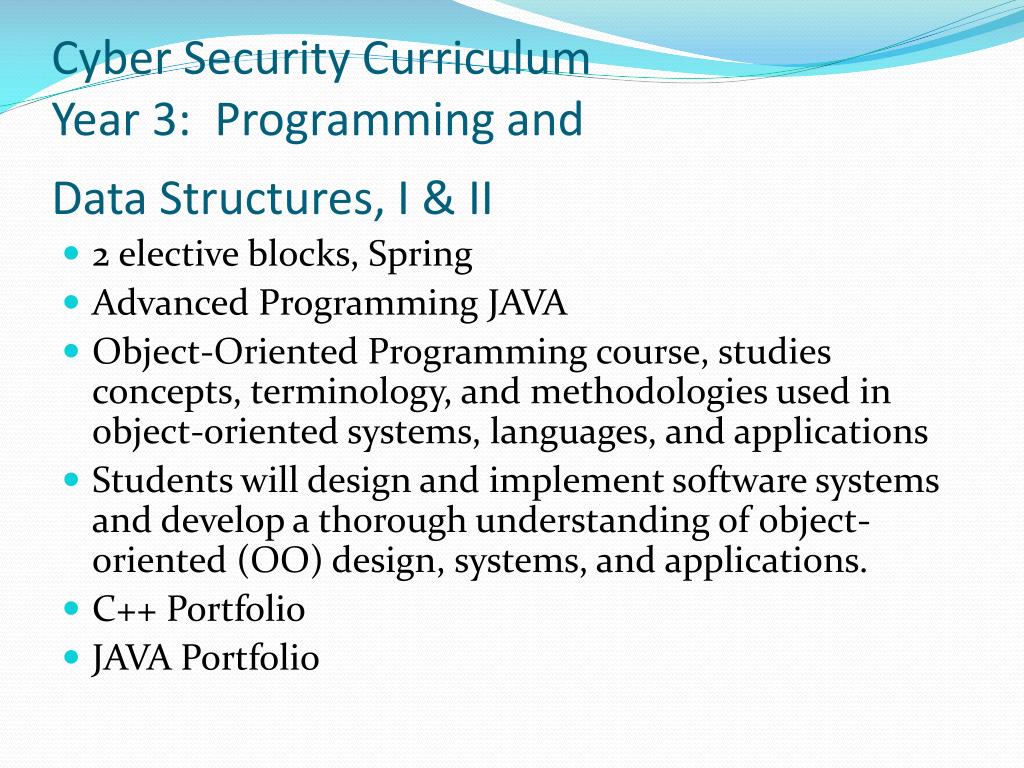
PPT - Cyber Security Curriculum PowerPoint Presentation, free download ...
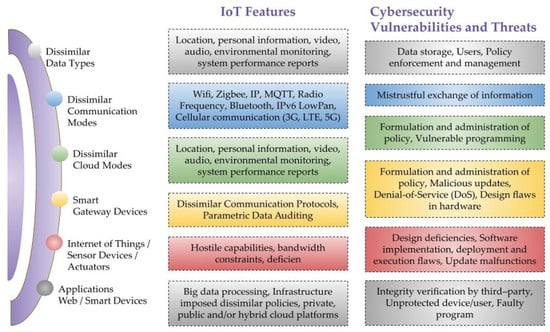
A Critical Cybersecurity Analysis and Future Research Directions for ...

The Top 10 Benefits of AI for Advanced Cyber security in Modern ...

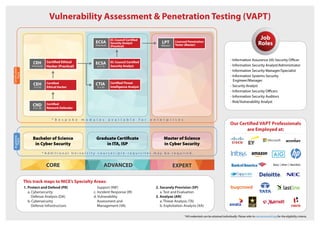
(PDF) Cybersecurity Curriculum Development: Introducing Specialties in ...
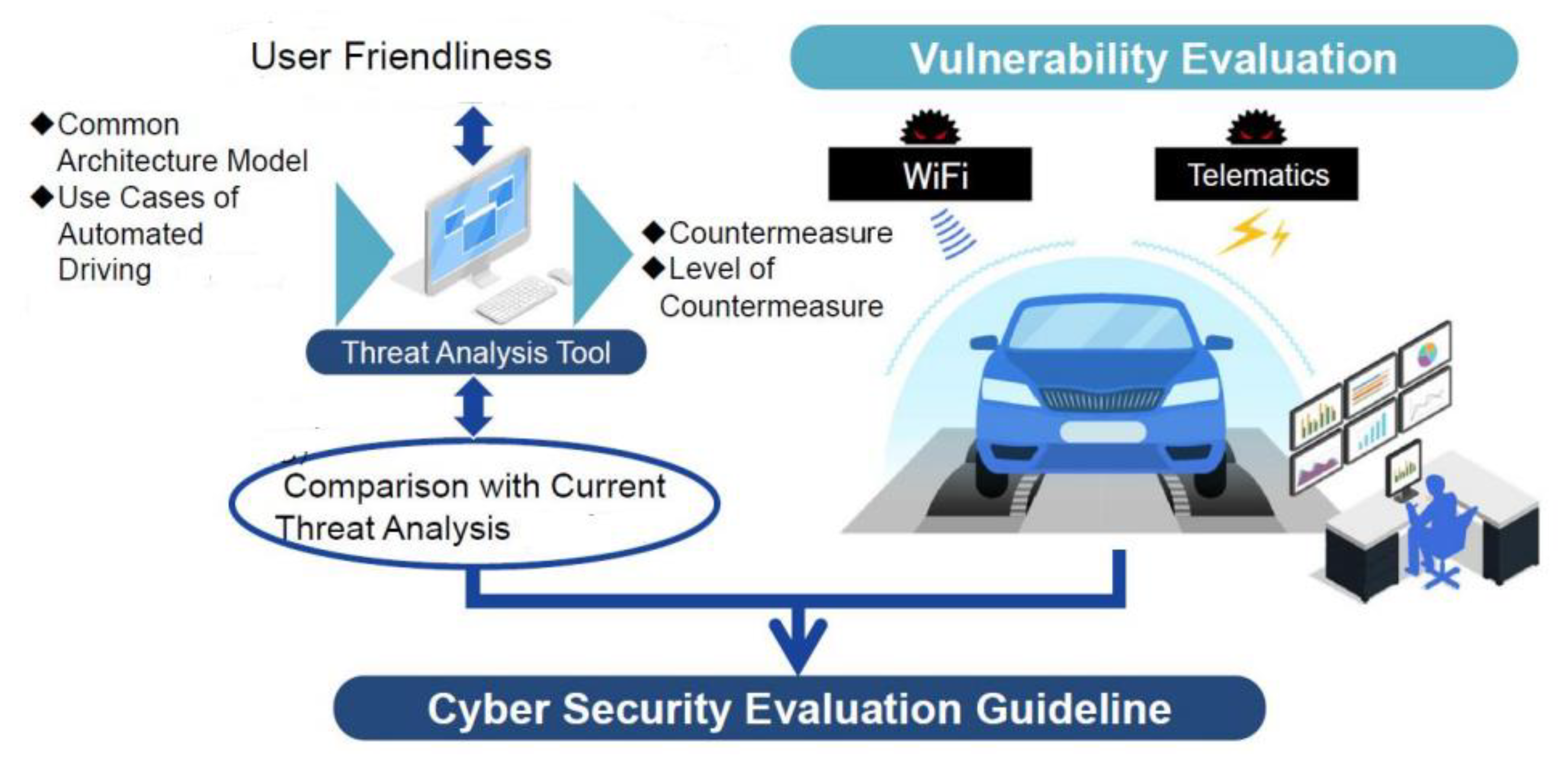
Autonomous Vehicles: The Cybersecurity Vulnerabilities and ...
Cyber Security Vulnerabilities | PDF

Cybersecurity Attack Vector Analysis For Effective Awareness Training ...

Top 10 Cyber Security Gap Analysis Templates with Examples and Samples

Cyber Security Curriculum Quantum Learnings 2020 | PDF | Denial Of ...
Advertisement Space (336x280)
Stanford Advanced Cyber Security Program: A Comprehensive Guide to ...

Cyber Security Analysis Powerpoint Ppt Template Bundles PPT Example

List of top 10 most common cybersecurity vulnerabilities
![Cybersecurity Vulnerabilities [Complete Guide] - Sprinto](https://sprinto.com/wp-content/uploads/2024/01/Healthcare-Compliance-Software-97.png)
Cybersecurity Vulnerabilities [Complete Guide] - Sprinto

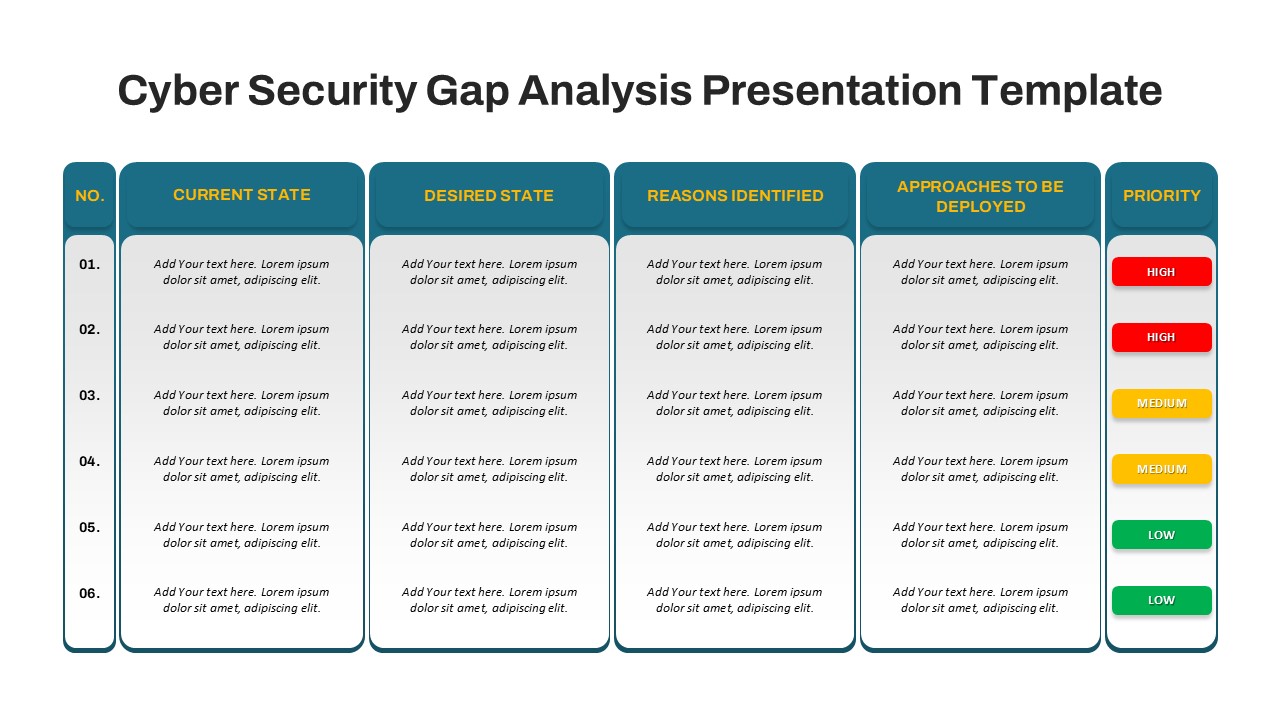
Top 10 Cyber Security Gap Analysis Templates with Examples and Samples

Online Master of Science in Cybersecurity Curriculum Overview | Course Hero

Organizing Security Awareness Conducting Cyber Security Gap Analysis Of Org

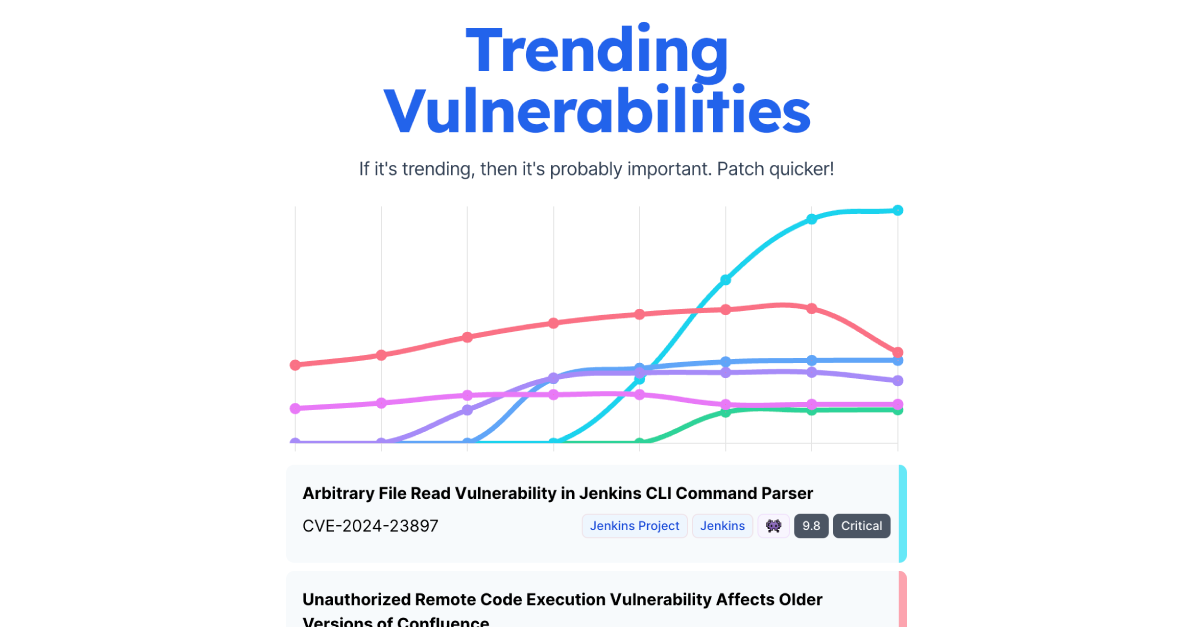
Uncovering Cybersecurity Vulnerabilities in 2024

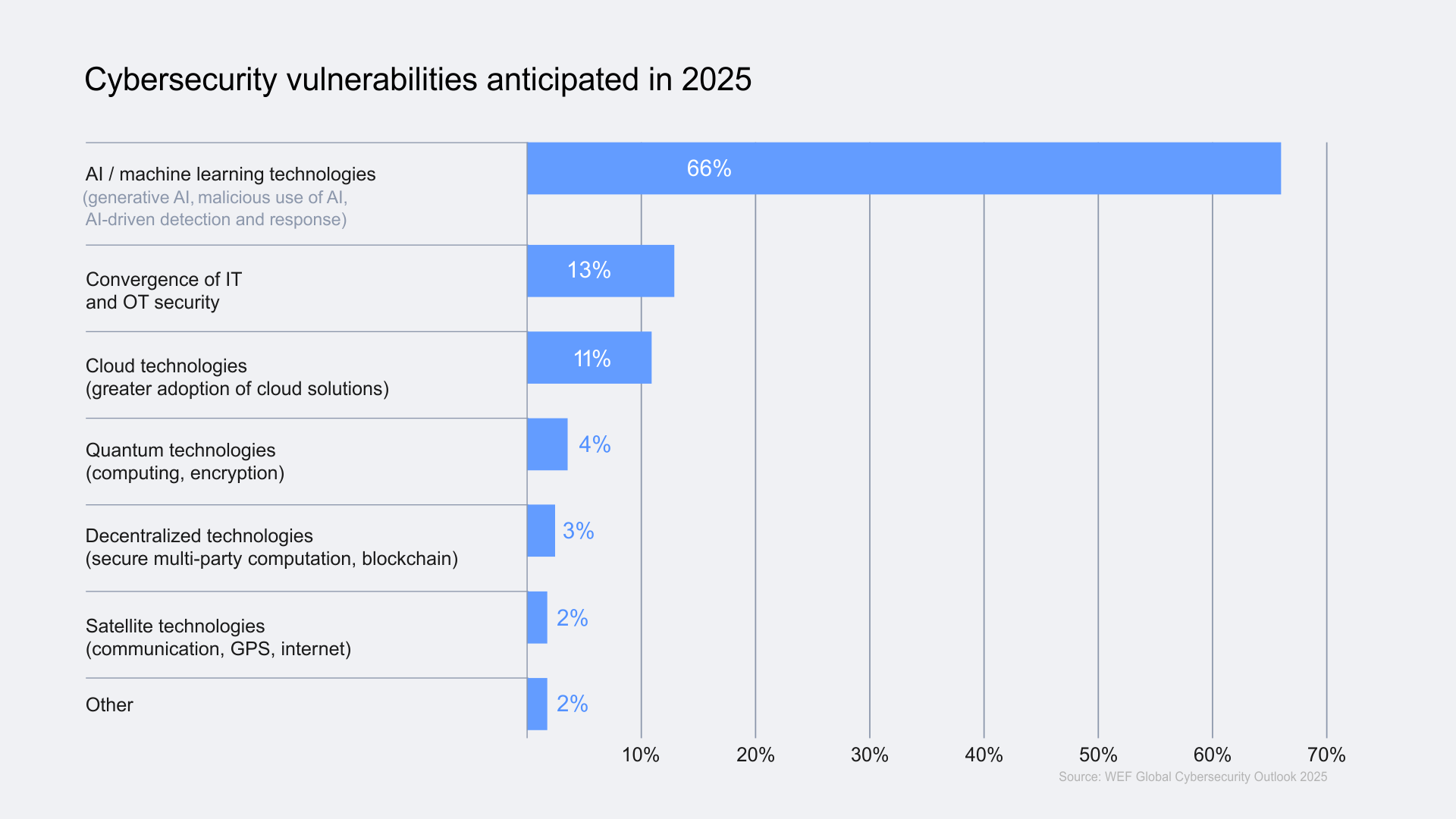
Cyber Security Vulnerabilities 2025: Management, Cloud Risks & AI Tools

IT Security-related and Cybersecurity Curriculum Taxonomy | Download ...
Advertisement Space (336x280)

Cybersecurity Digital Technologies Unit Aus Curriculum v9 by HEFFORDMedia

Cyber Security Vulnerabilities 2025: Management, Cloud Risks & AI Tools

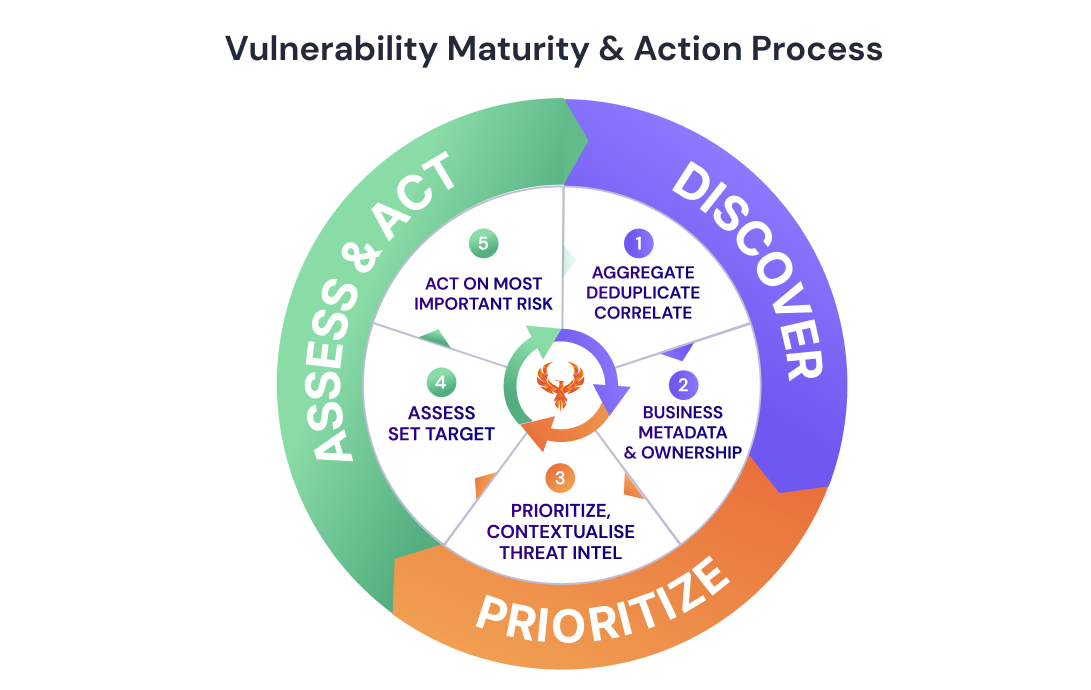
Embracing Advanced Frameworks for Effective Vulnerability Management ...
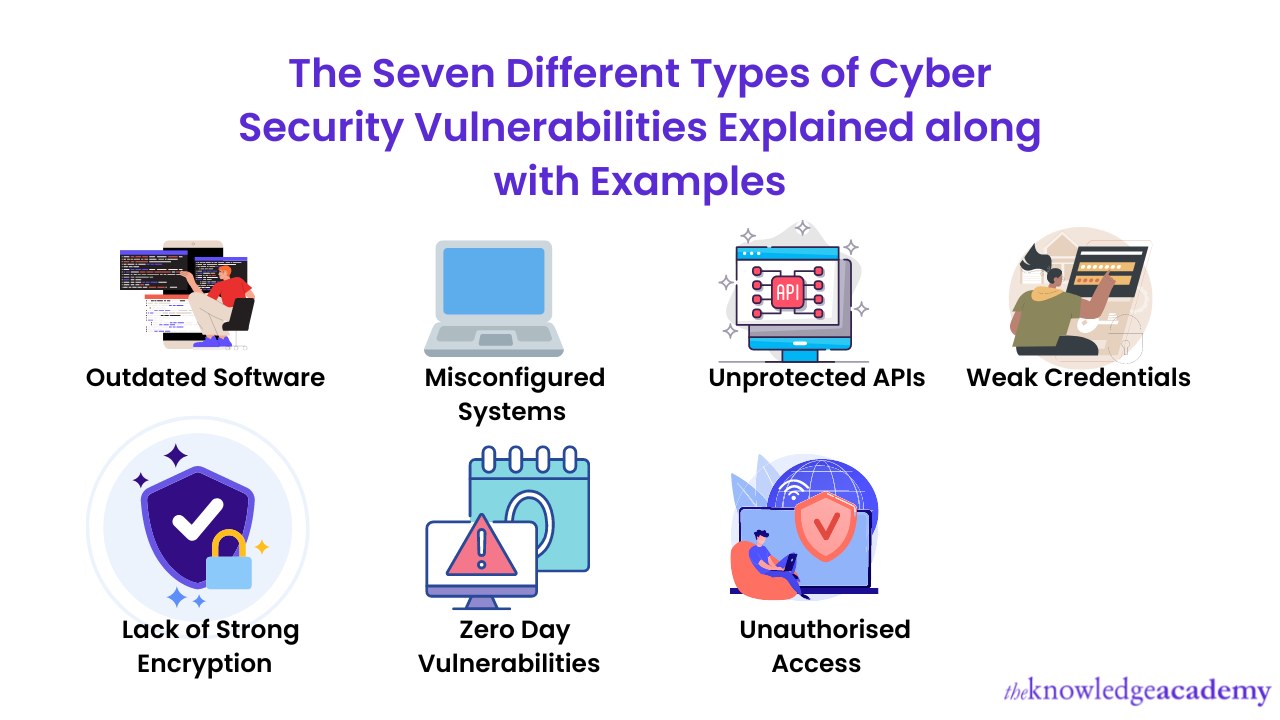
What is Vulnerability in Cyber Security With Example?
Embracing Advanced Frameworks for Effective Vulnerability Management ...
Cybersecurity Audit - FORTIC TECHNOLOGIES

20+ Cybersecurity Vulnerability Statistics & Trends (2026)

Risk analysis, essential for your cybersecurity - MS Solutions

Top 10 Cybersecurity Dashboard Templates With Samples and Examples
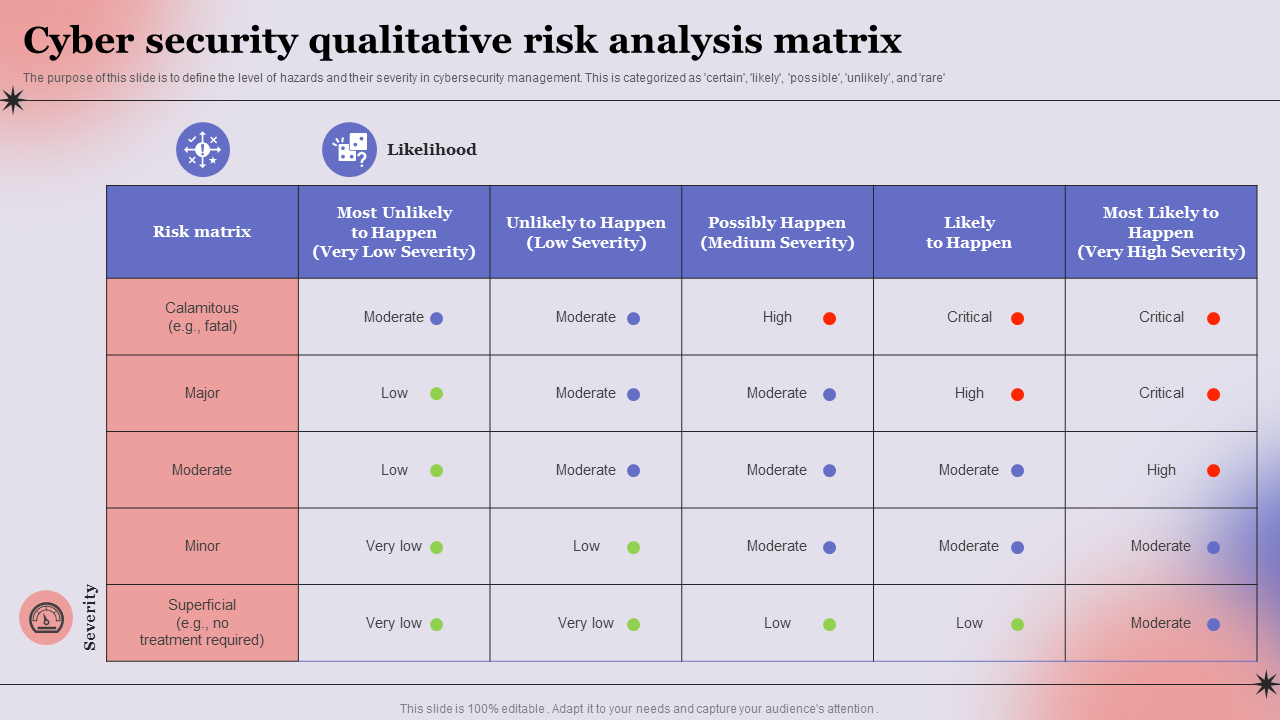
Top 7 Cyber Risk Analysis Templates with Samples and Examples
Advertisement Space (336x280)

PPT - How to assess your Cybersecurity Vulnerability_ PowerPoint ...

Common types of cyber vulnerabilities

Weekly Cybersecurity Roundup: Key Vulnerabilities, Threats, and Data ...

Cyber Security Risk Management Plan Threat Identification And Vulnerability
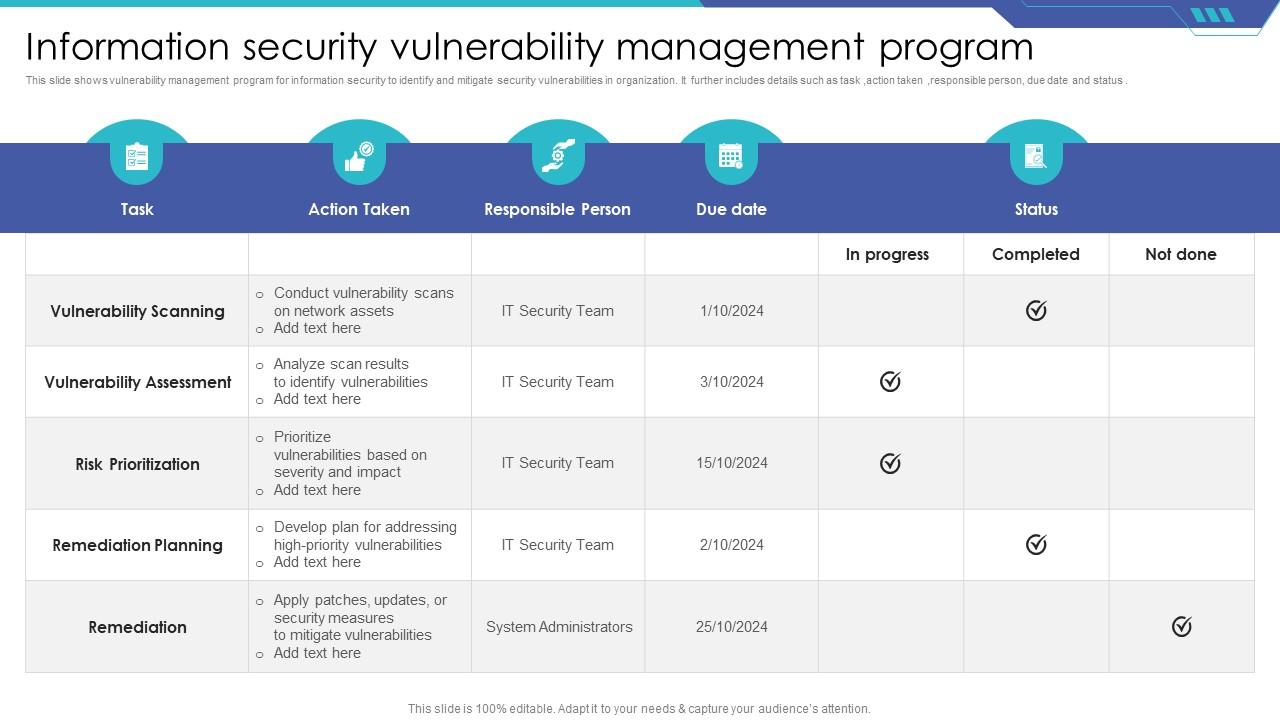
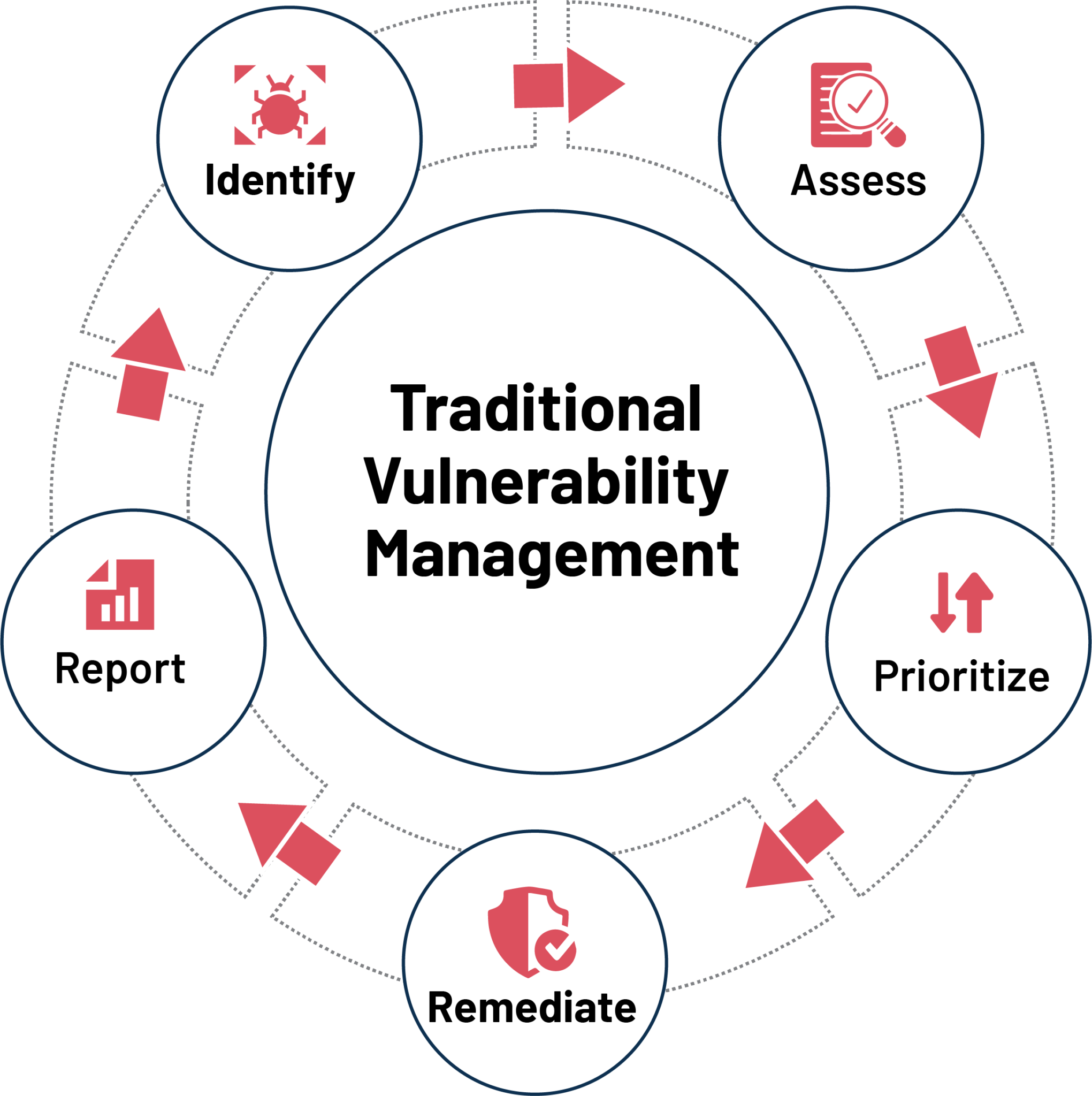
Information Security Vulnerability Management Program PPT Sample

Cyber Security Vulnerability Assessment – ICT BYTE

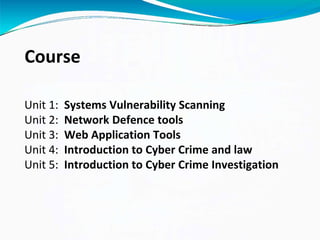
Cyber Security Analytics Topics Course Content | PDF
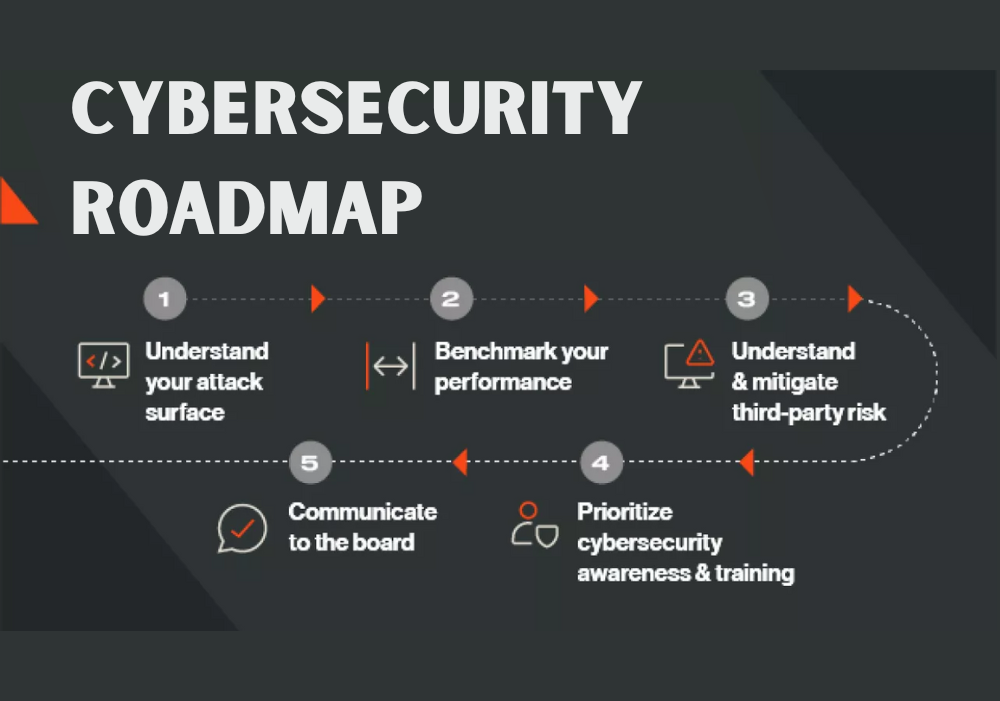
Cyber Security Roadmap Template - SlideKit

Cybersecurity Vulnerabilities: All you need to know | by Machint ...

Cyber Security Vulnerability Assessment Template
Advertisement Space (336x280)

Cybersecurity Vulnerabilities: Most Common Types of Cyber Attack ...

Course overview Cybersecurity and its applications | PDF

Common types of cyber vulnerabilities
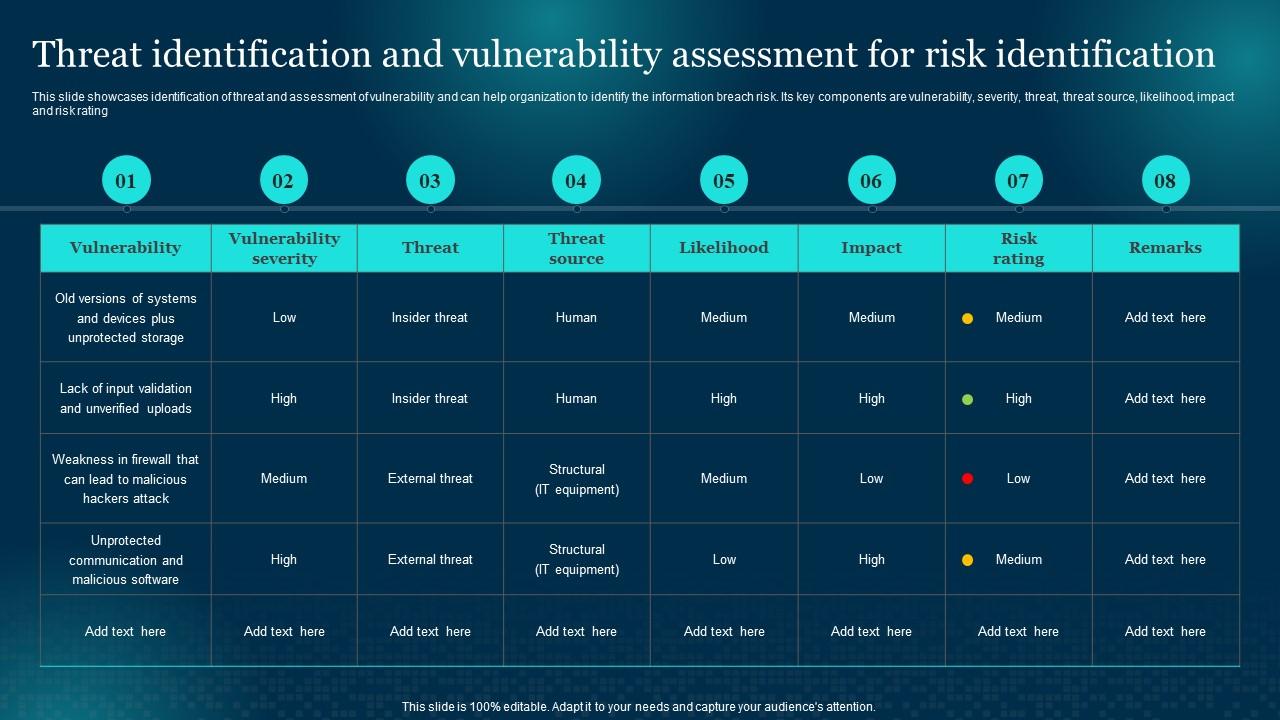
Threat Identification And Vulnerability Assessment For Cybersecurity ...

An Overview of Using AI for Next-Generation Data Security

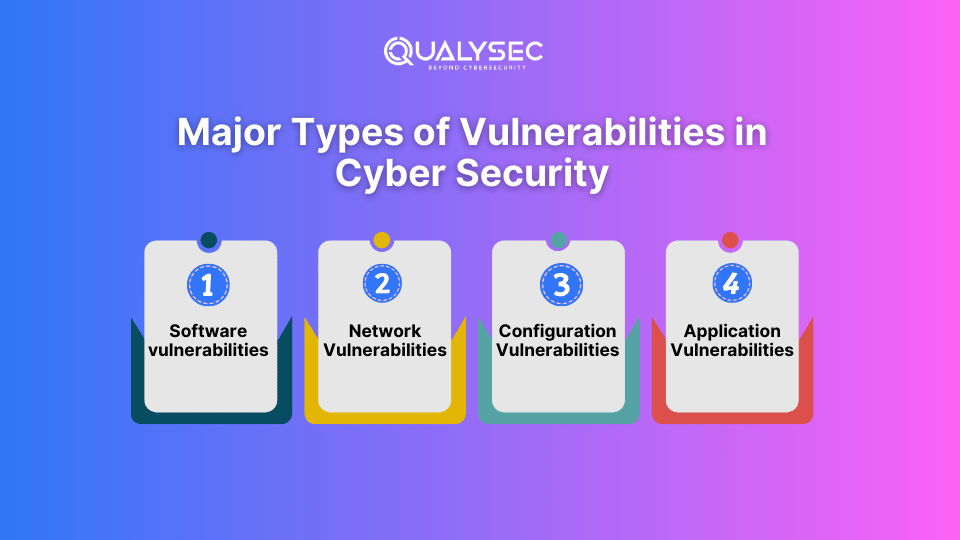
What are the Types of Cyber Security Vulnerabilities? - Global Tech Council

Threat Vulnerability Dashboard Information Security Risk Management ...
A Comprehensive Review of Cyber Security Vulnerabilities, Threats ...
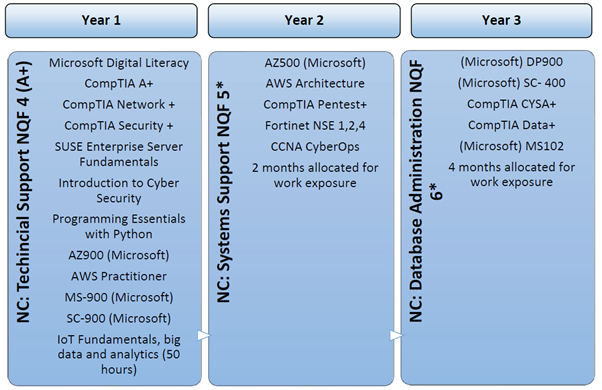
Curriculum - Absa Group | Welcome to Absa Group Limited

Cybersecurity Monitoring Dashboard Slide - NIST Cybersecurity Framework ...
Advertisement Space (336x280)

Top 10 Cybersecurity Awareness Program PowerPoint Presentation ...

Top 10 Cybersecurity Risk Assessment PowerPoint Presentation Templates ...

Top 10 Cybersecurity Risk Assessment Templates with Examples and Samples

Offensive cyber security engineer | PDF

The Importance of Vulnerability Assessments in Cybersecurity - C ...
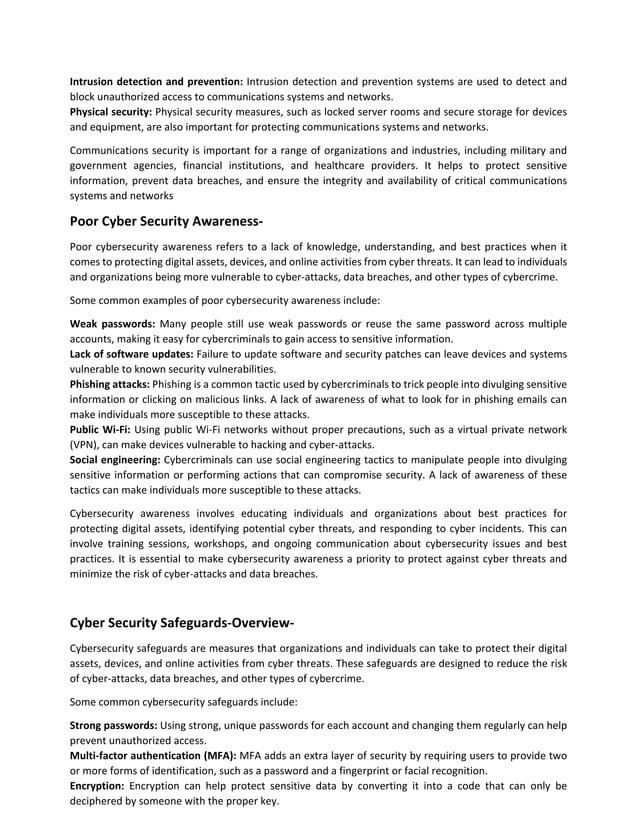
Module 4 Cyber Security Vulnerabilities& Safe Guards | PDF

Understanding Vulnerabilities in Cybersecurity: A Comprehensive ...
Cybersecurity | PPTX
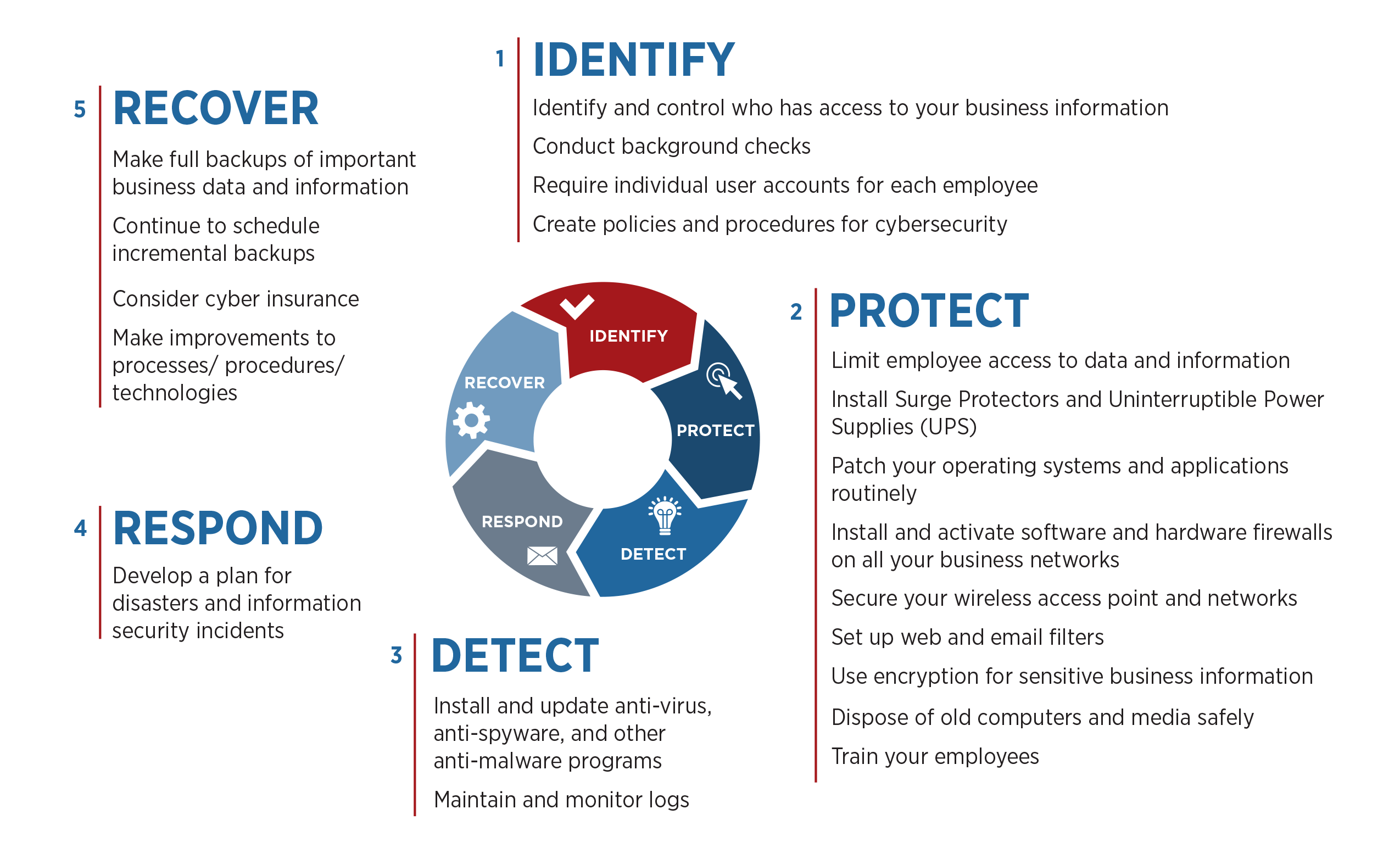
MEP Centers Aid Manufacturers on Cybersecurity | NIST

Advanced Persistent Threat Lifecycle Diagram Malware Access Control ...
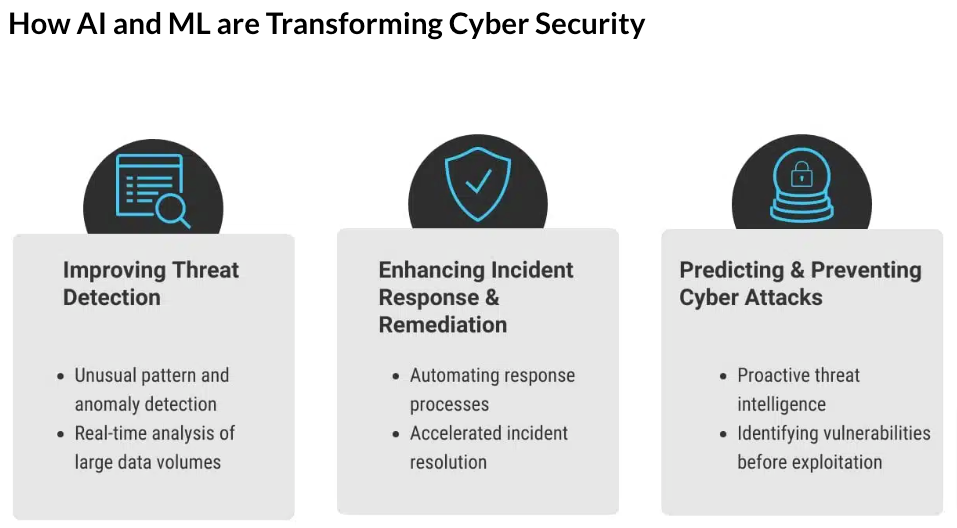
The benefits of AI in cyber security and Its Role
Tackling Cyber Threats with Automation: Salesforce’s Security Strategy

Cybersecurity: security vulnerabilities. | Download Scientific Diagram

Get the most recent ICSS Blog | ICSS Cybersecurity Blog
Cybersecurity 101: A Beginner’s Guide to Networking Fundamentals ...

Home - Level 6 Cybersecurity

20+ Cybersecurity Vulnerability Statistics & Trends (2026)

Cybersecurity Business Value Benchmark - Measure Protection Levels

Threat, Vulnerability and Risk in Cyber Security - Bangalore

Lab 6 cybersecurity.docx - Lab 6: Managing Technical Vulnerabilities ...

Cyber Security Module 2 Assignment 1 - Vulnerability Scanner | PDF ...
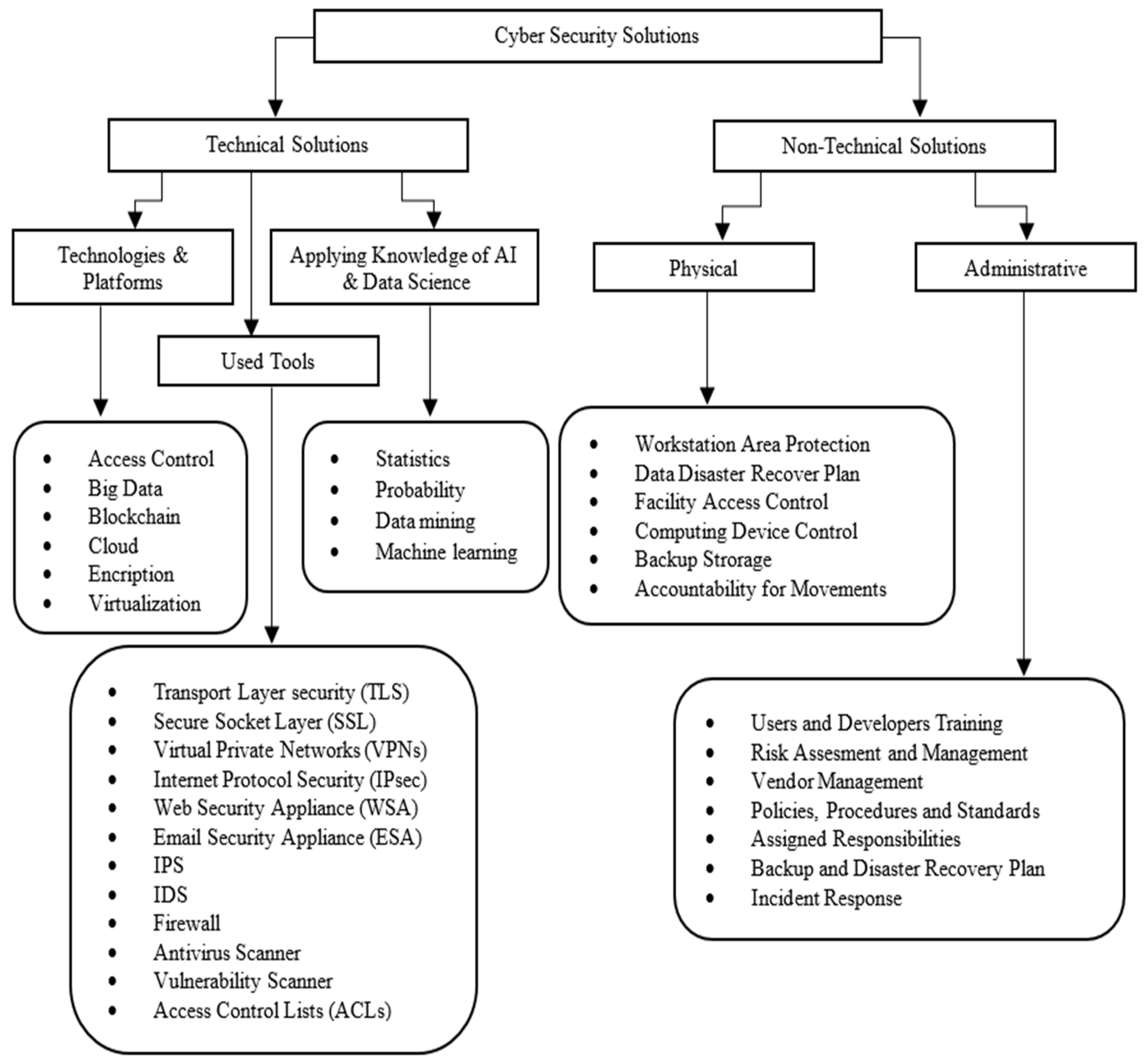
A Comprehensive Review of Cyber Security Vulnerabilities, Threats ...

Advanced Cyber Security: Week 3 Lab and Tutorial - Get to Know | Course ...

cyber security vulnerabilities.html - CompTIA Security Cyber Security ...
Vulnerability Managment Framework - Application Security - Code to Cloud

Advance Cyber Security
The Cyber Security Vulnerability Database.

Cyber Security Vulnerability Assessment Model for County Governments by ...

Fundamentals of Cyberattacks - Pathway Communication Cyber Security
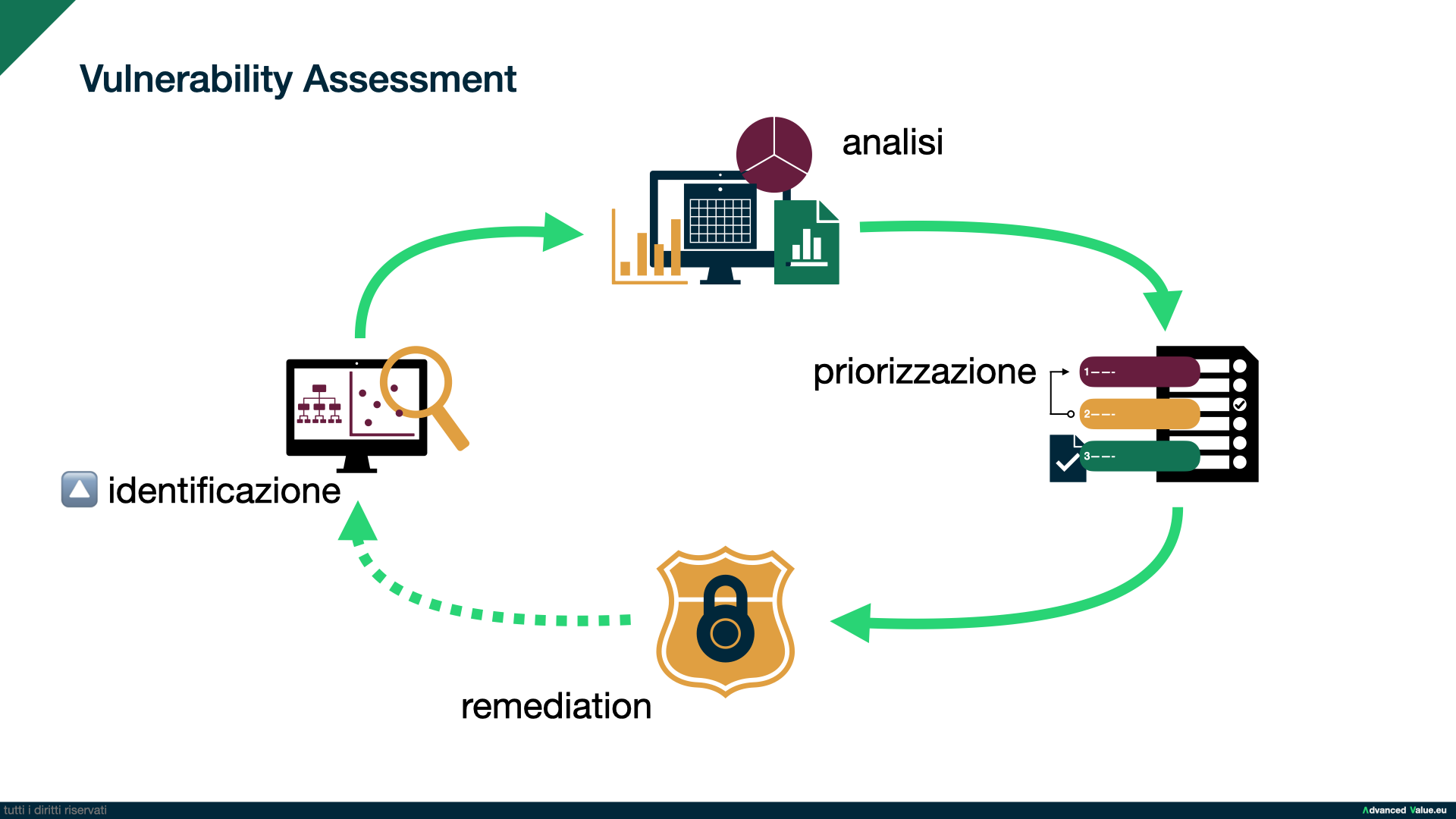
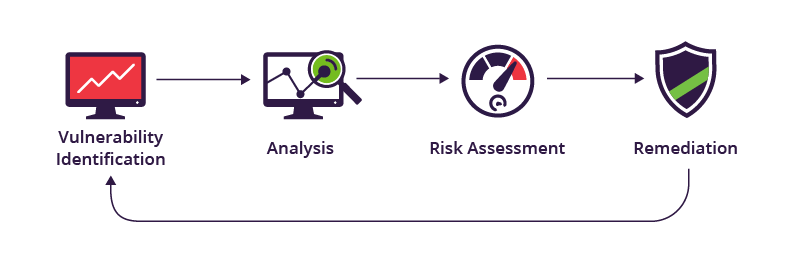
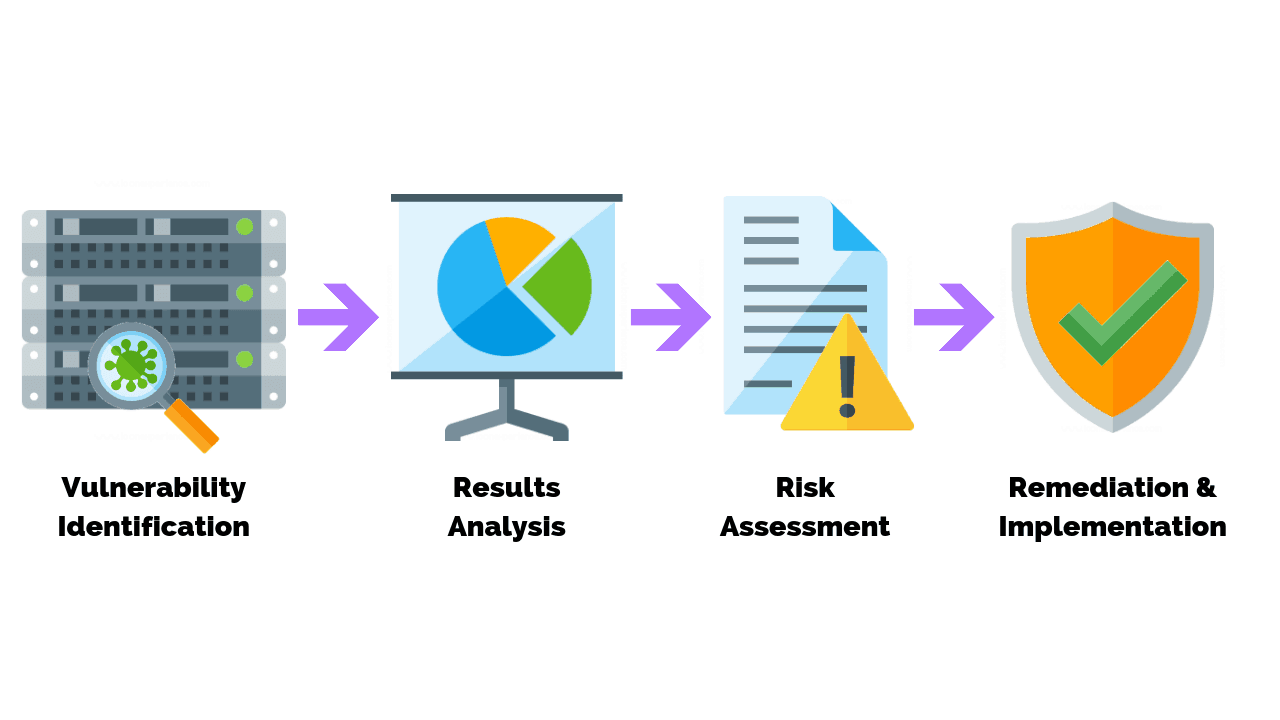
Vulnerability Assessment
What is vulnerability in cyber security: Definition & Impact

Vulnerability in Cybersecurity: Definition, Types and Prevention

Digital Learning | IT Development | Consulting | Translation Services ...
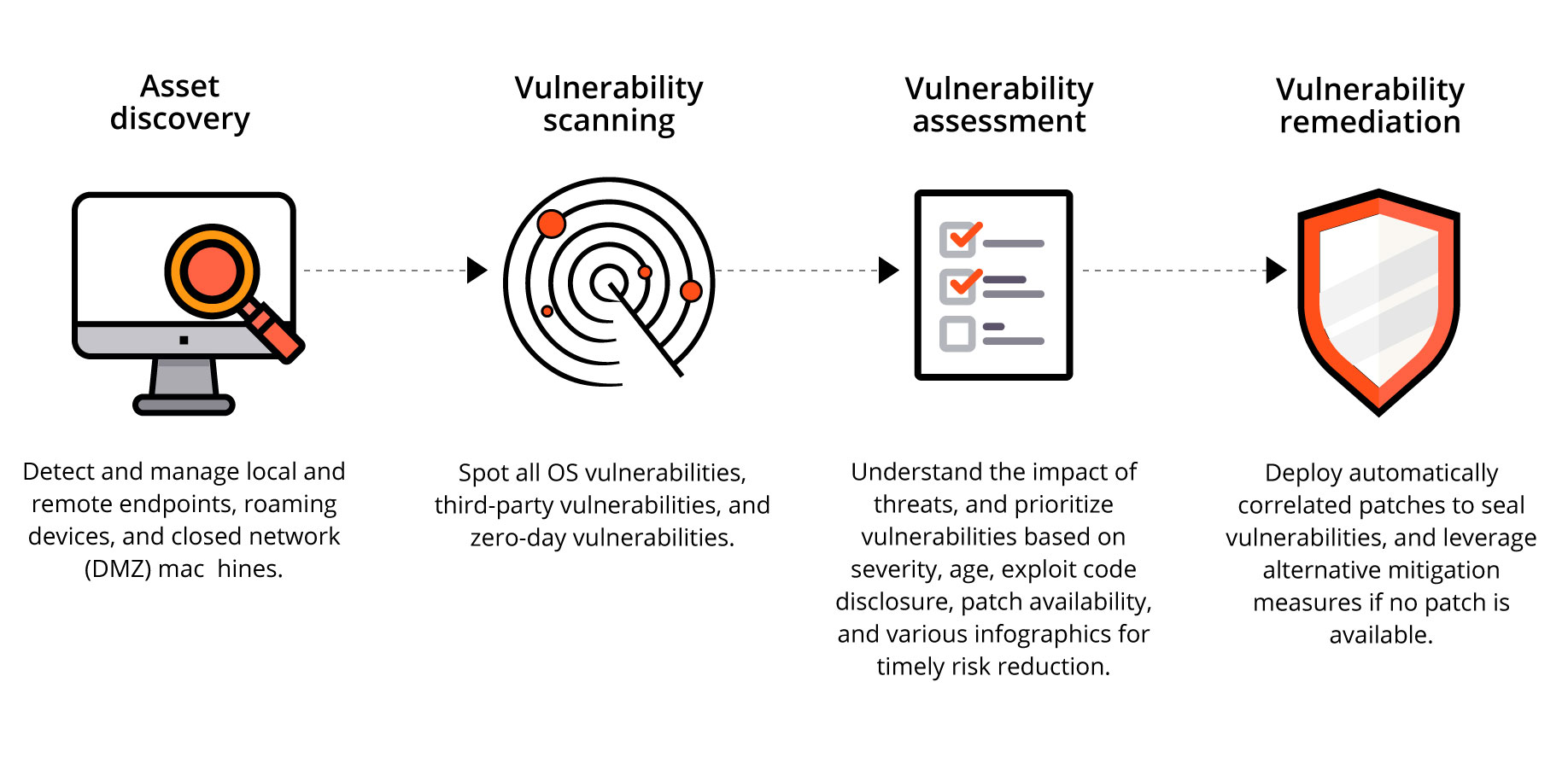
Vulnerability Assessment - WebSec Services

Vulnerability Assessment - Lanworks

Top 10 Vulnerability Assessment Templates With Examples and Samples
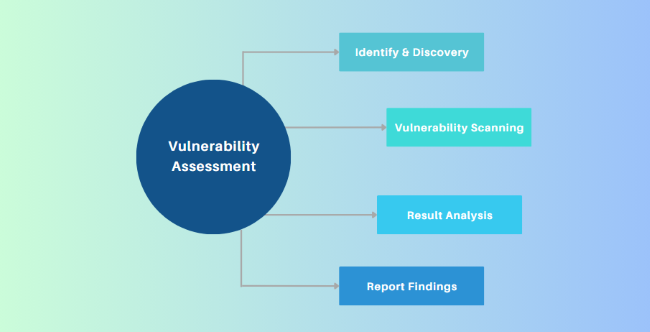
What is Vulnerability Assessment in Cyber Security– AirDroid
Vulnerability Assessment In Cybersecurity: A Complete Guide (2025 ...
Bot Verification

Vulnerability in Cyber Security: Types and Causes

Vulnerability Management Program Maturity Model at Cassandra Wild blog

Sample Vulnerability Management Program at Charles Mattingly blog
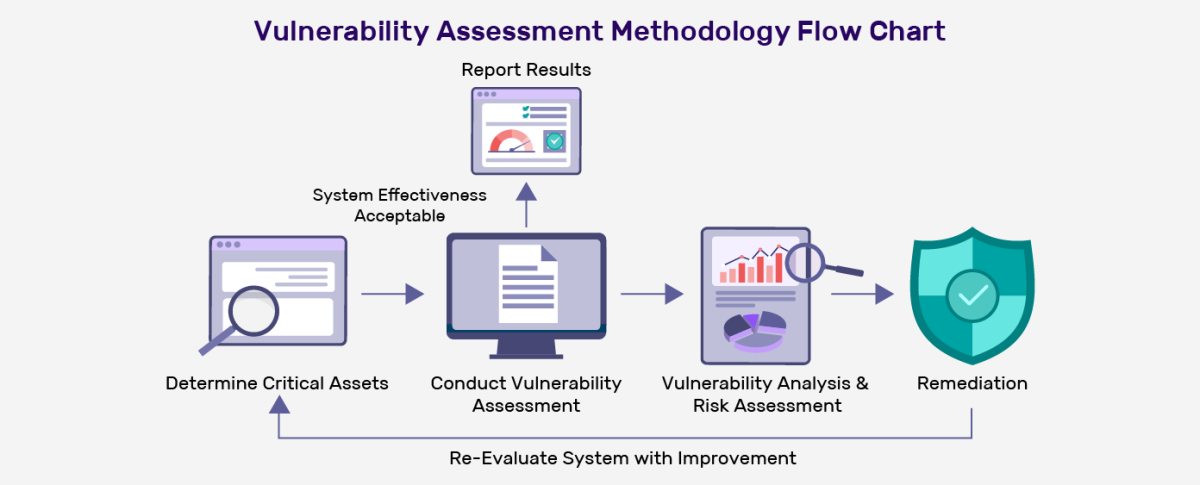
The Importance of Vulnerability Assessment: Types and Methodology ...

Top 10 Vulnerability analyzing dashboard for cyber threat intelligence ...

The Importance Of Vulnerability Assessment - Protect Your Business ...

Vulnerability Assessment: Key Steps and Benefits Explained

Vulnerability in Cyber Security: A Complete Overview
What is Data Loss Prevention - Understanding DLP Tools and Trends

Key Components Of Vulnerability Remediation Plan System Vulnerability ...
How To Perform A Vulnerability Assessment In 8 Steps
Cyber handbook-enterprise-v1.6 | PDF
Network Vulnerability Assessment and Penetration Testing | Blog
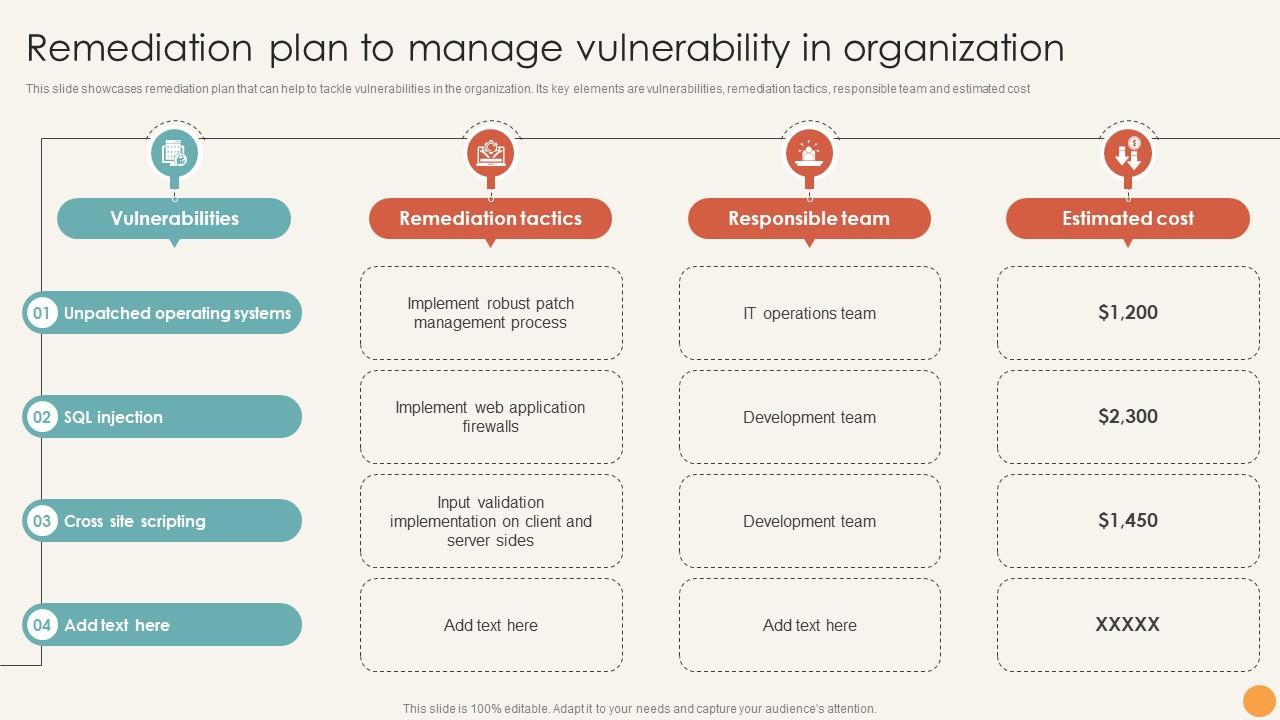
Remediation Plan To Manage Vulnerability In Organization System ...
Top 15 Paid and Free Vulnerability Scanner Tools - DNSstuff

What Is Adaptive Security? Benefits, Use Cases & Examples

Give aid in cyber security, vulnerability analysis, and penetration ...

Curriculum: Introduction to Cyber-security

Vulnerability Management Program Risks at Catherine Reeves blog

Qilin Ransomware: Analysis, Impact and Defense (2025) | BlackFog
8 Threat Detection Techniques to Outsmart Attackers
