ICT Methods to Secure Data Online

ICT - Methods to Secure Data Online by Catra Learning Resources | TPT

Top 7 Ways to Secure Your Online Data & Have More Privacy | Office1

Keeping data secure - Data protection methods - GCSE ICT Revision ...

Efficient Methods to Keep your Data Safe and Secure

How to Secure and Backup Data Online

How to secure your data from others device // by ICT care - YouTube

How to Secure and Backup Data Online

Essential Tips To Secure Your Data Online - Scam Reviewer

Dihardja Software - How to Secure Your Business Data Online

Online Data Protection To Secure Data Storage Used By Global Business ...
Advertisement Space (300x250)
![[Video] How to secure sensitive data and systems | Supreme ICT Academy ...](https://media.licdn.com/dms/image/D4D05AQGe5-xWF_kkAg/videocover-high/0/1716196212209?e=2147483647&v=beta&t=f4hOB2Q-Qoqs14KgZhJIuemrLUWJZACbrK3vHdkvX0A)
[Video] How to secure sensitive data and systems | Supreme ICT Academy ...

How To Secure Data Transmission? - Newsoftwares.net Blog

Best Ways to Secure ICT Systems
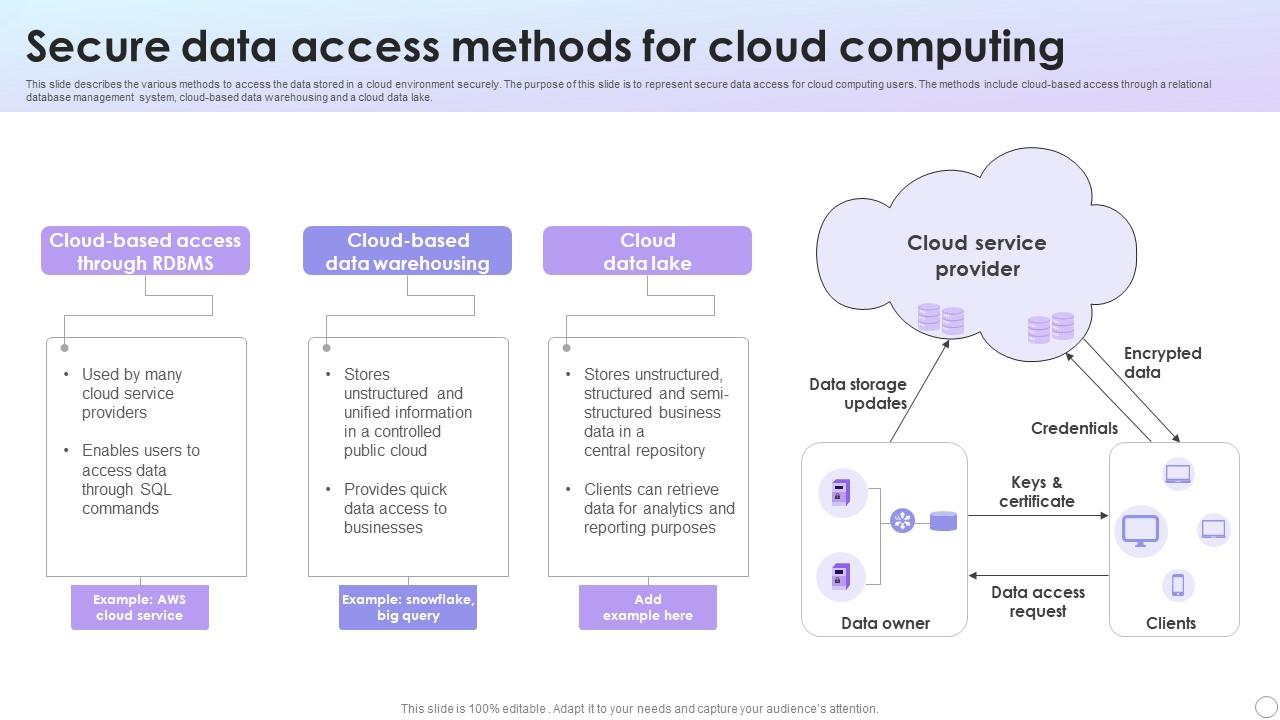
Secure Data Access Methods For Cloud Computing PPT Template

How To Stay Safe Online | ICT Solutions

Top Five Ways To Keep Data Secure In 2024!
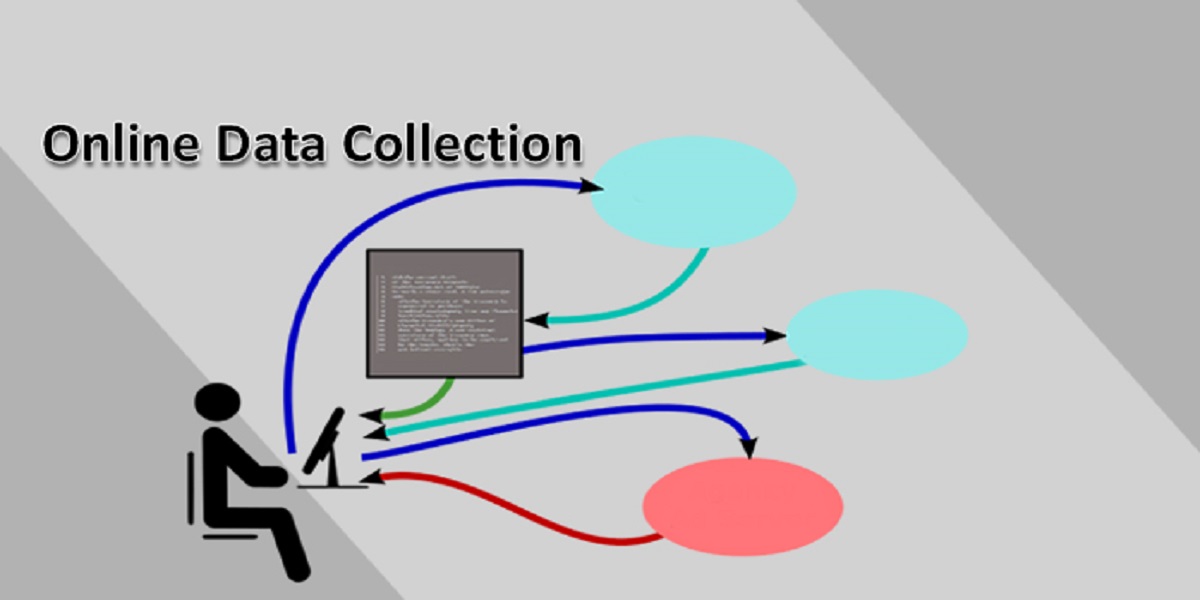
Processes & Methods Involved in Online Data Collection

How to Secure Digital Data: Best Practices for Online Safety • Teachers ...

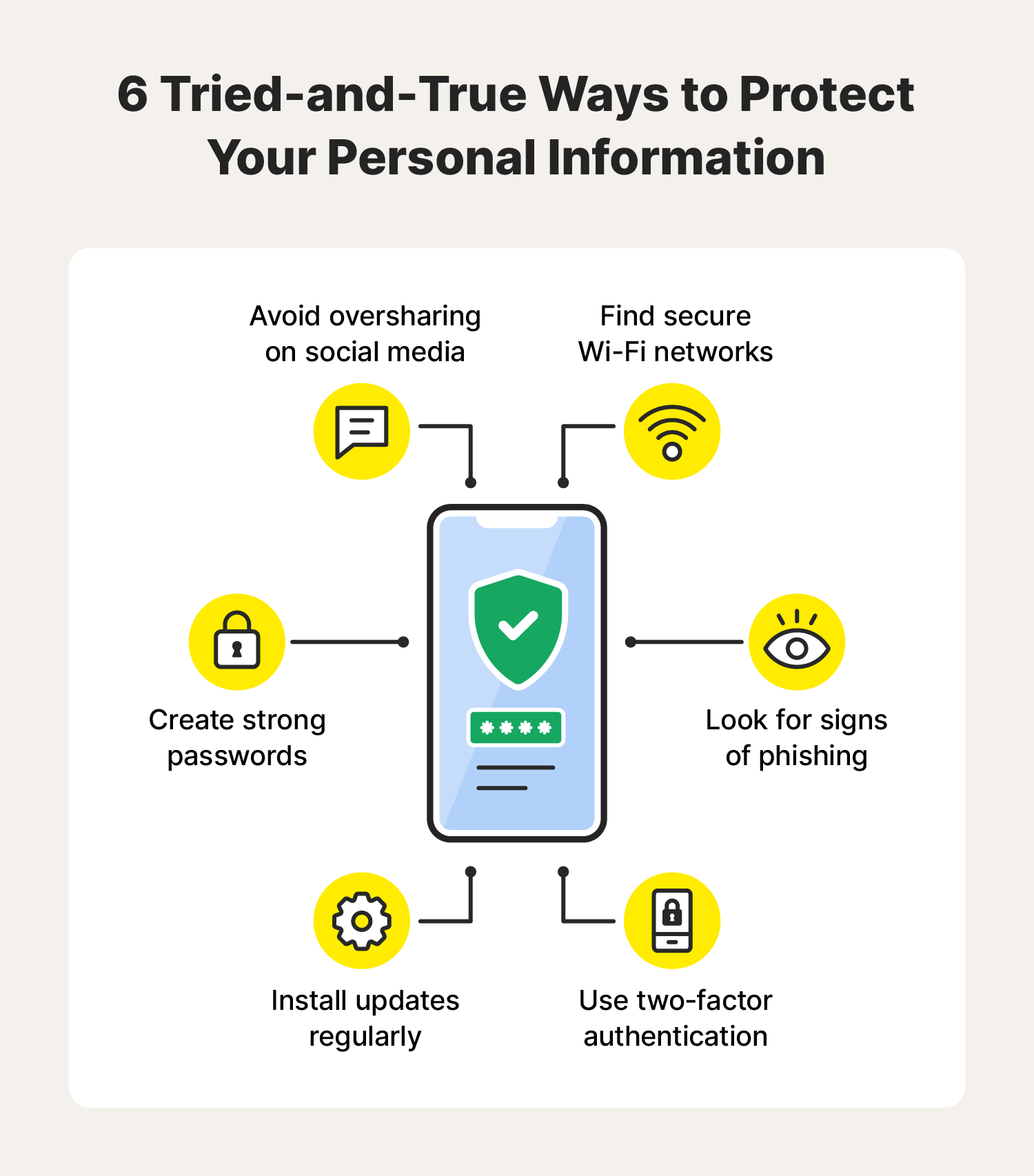
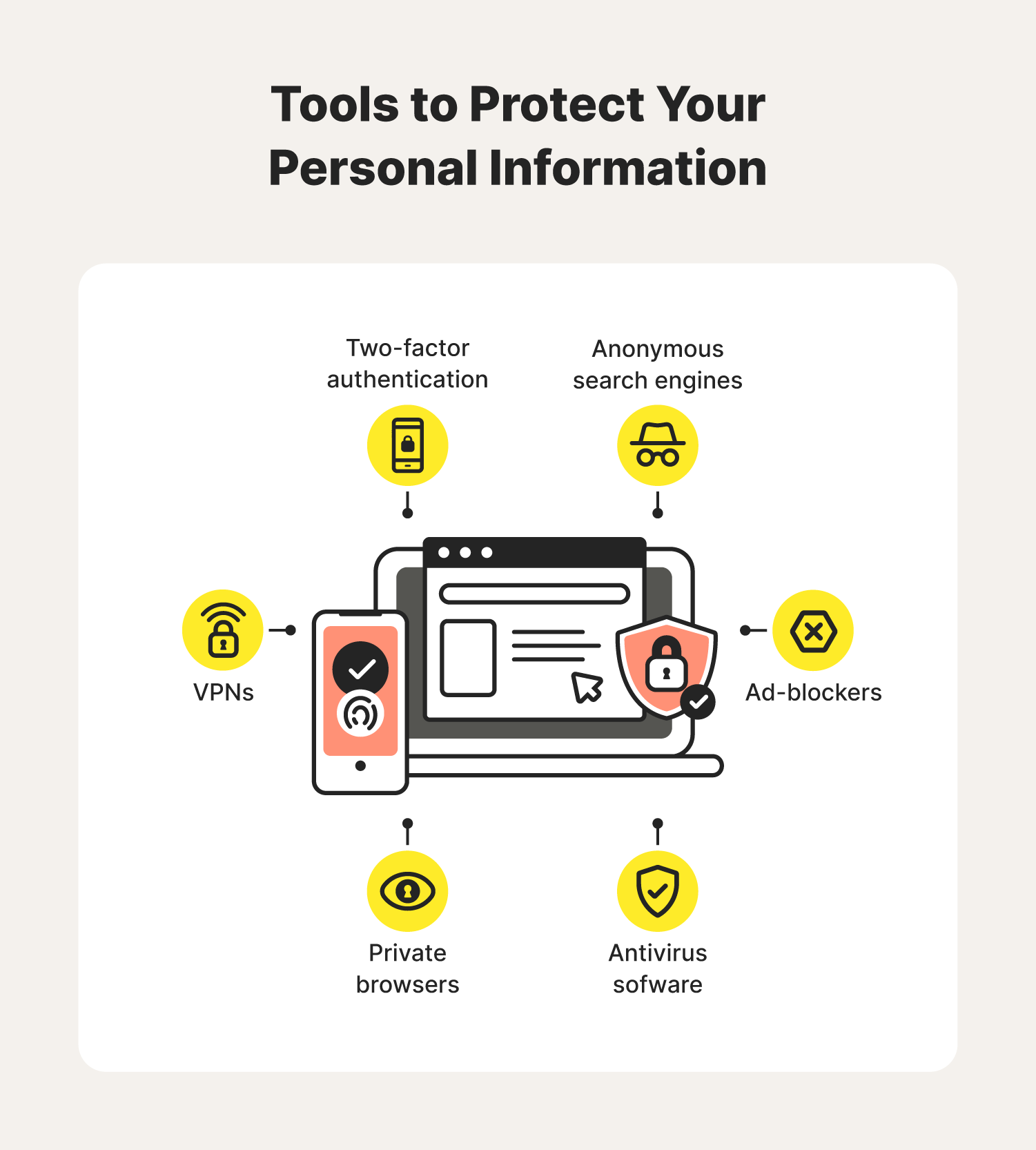
How to Protect Your Personal Data Online
5 Ways To Keep Your Data Secure In An Evolving Digital World. - Iconis
Advertisement Space (336x280)

5 Ways to Protect Your Data Online

6 Essential Steps To Secure Your Data – INNOVD – ST Engineering
How to Secure Data at Rest, In Use and In Motion

12 Simple Things You Can Do to Be More Secure Online | PCMag

Web data security in internet and online secure access technology ...

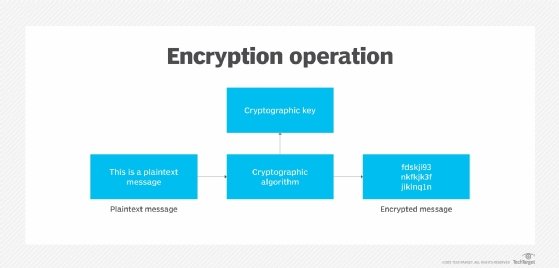
Secure Your Data in the Digital Age - Top Encryption Methods

10 Tips to Protect Your Online Data Privacy in 2025 - GeeksforGeeks

Secure access and online data protection. Data privacy and cyber ...

7 Guidelines to Best Protect Your Online Data - CenterGrid

Premium Photo | Protecting Online Data Through Encryption Encoding to ...
Advertisement Space (336x280)
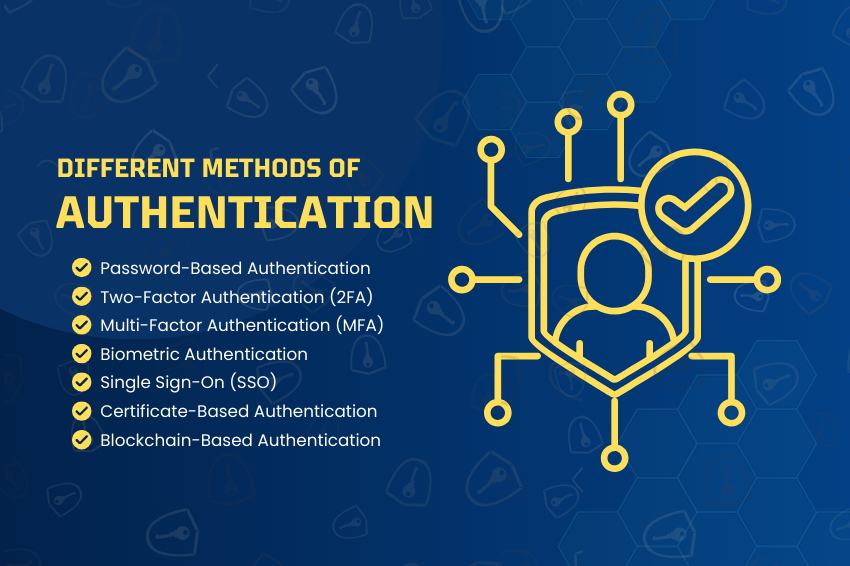
7 Authentication Methods to Secure Digital Access - The Run Time

How To Keep Your Data Safe Online - 8 Essential Tips

Top 5 Ways to Secure Your Data When Working From Home | Buffalo Americas

How to Safeguard Your Online Data Security (Best Practices)

Top 5 Methods of Protecting Data - TitanFile

Cloud Data Security & Protection: Everything You Need to Know - Palo ...

Data protection concept and secure internet security access ,cyber ...

Data protection concept and secure internet security access ,cyber ...
Data protection concept and secure internet security access ,cyber ...
![10 Tips to Protect Your Data [Infographic] | SecurityHQ](https://www.securityhq.com/wp-content/uploads/2021/07/SecurityHQ-Infographic-Tips-to-Protect-your-Data-538x1024.jpg)
10 Tips to Protect Your Data [Infographic] | SecurityHQ
Advertisement Space (336x280)
Online Safety: Essential Tips to Protect Yourself in the Digital World ...

Data protection concept and secure internet security access ,cyber ...

Overview Of Business ICT Security Data Protection Implementation ICT ...

Data protection concept and secure internet security access ,cyber ...

11 Ways How to Protect your Personal Information Online - PassCamp

What Are Best Practices to Secure Big Data? - Food Stamps

How To Protect Your ICT Infrastructure from Security Threat?

Cyber safety tips infographic: how to connect online and use social ...
Protect Using Passwords To Protect Your Data NCSC.GOV.UK

What Is Data Protection? Best Practices for Secure Data
Advertisement Space (336x280)

2 - Safety and Security of Data in ICT Systems | PDF | Computer Virus ...

What Are The Top Secure Data Transmission Methods? | Penta Security Inc.

What Is The Most Secure Data Transfer Today? - Newsoftwares.net Blog

5 Tips For Storing Online Data Securely For Your Business - nancyrubin

Data protection concept and secure internet security access ,cyber ...

Overview Of Business Ict Security For Data Comprehensive Guide For ...

Data Security: Smart Ways to Protect Privacy

Data protection concept and secure internet security access ,cyber ...
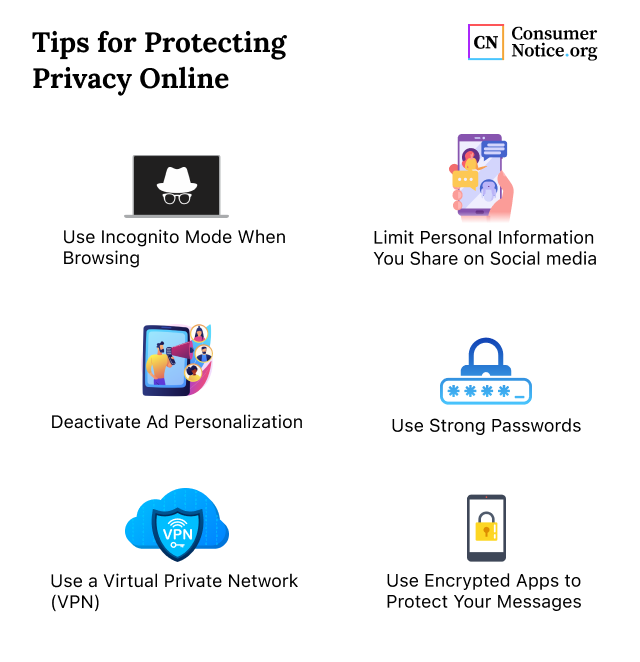
Internet Privacy Tips: How to Protect Personal Information Online

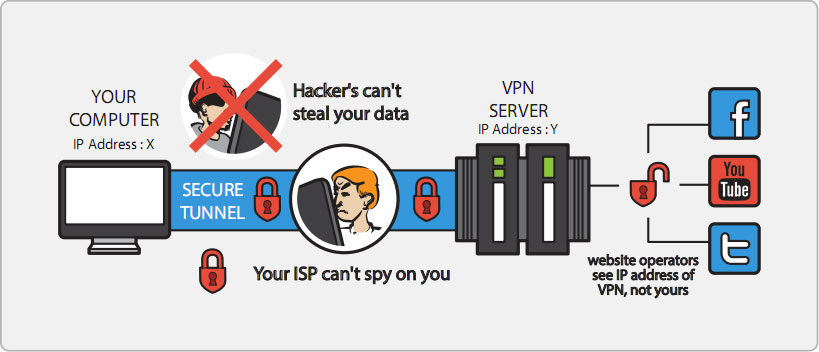
The Ultimate Guide To Securely Transfer Data Over The Internet
Advertisement Space (336x280)
Ways To Protect Data From Hackers - Newsoftwares.net Blog

Secure Cyber Data. Online Privacy Safety. Computer Information Stock ...

Internet data security and online global network protection with ...

Securing Your Data and Online Identity - Technology Article ...

Data protection concept and secure internet security access ,cyber ...

Premium Photo | Cyber security and online data protection with tacit ...

Data protection concept and secure internet security access ,cyber ...

Data protection concept and secure internet security access ,cyber ...
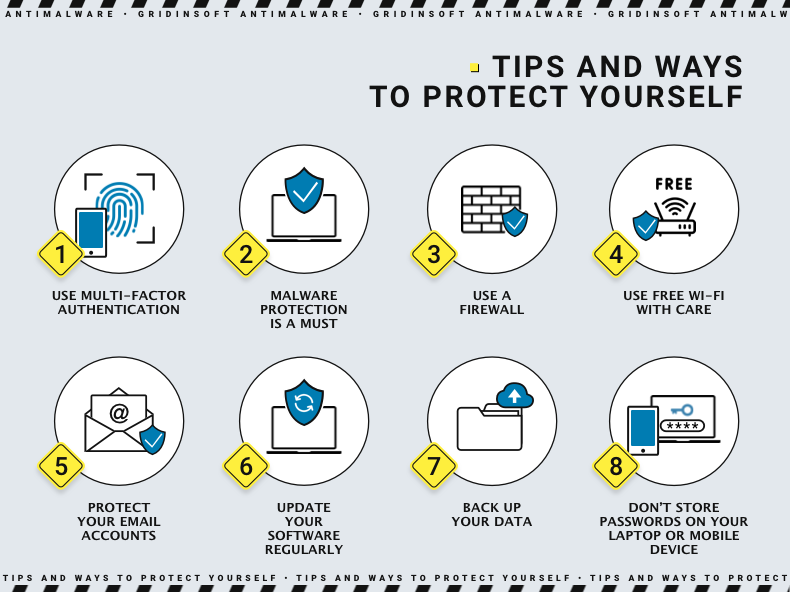
10 Ways to Protect Your Personal Data – Gridinsoft Blog
How to protect your data online? - Global Village Space

Innovative view of online data protection and cyber security ...

Securing Your Online Presence: Tips for Protecting Personal Data from ...

Premium Photo | Online data protection and information security concept

Cybersecurity Tips for Protecting Your Online Data - StoryMag

Keep Your Personal Data Secure: Top 5 Methods

Web Traffic Encryption Concept - Secure Online Communications - Process ...

Data Privacy in the Digital Age: How to Protect Your Information

The Ultimate Guide To Securely Transfer Data Over The Internet

5 Tools for Secure Communications and Data Storage - ICTworks

How To Check Security Of My Online Data? - Newsoftwares.net Blog

Data protection concept and secure internet security access ,cyber ...

Cybersecurity 101: Protect Your Devices and Online Data

Securing Online Data Images - Free Download on Freepik

Premium Vector | Internet security global online data protection

Data protection concept and secure internet security access ,cyber ...

Premium Photo | Data privacy and online safety exploring blockchain s ...

Premium Photo | Cyber security and online data protection with tacit ...

Online security technology personal data protection an | Premium AI ...
How Secure Is Our Online Information? - Technology Article ...

Concept of cyber security, information security and encryption, secure ...

Safeguarding Your Online Data: A Comprehensive Step-by-Step Tutorial ...

ICT Security Solutions - Techvana

Computer Security : Security Measure ~ ICT SPM - Blog Cikgu Hisham

Features Of Data Security at Byron Wells blog
.jpg)
Is your school’s ICT network safe and secure? | The Educator K/12
Implementation Of Information Overview Of Business Ict Security For ...

ICT security in the digital transformation era | Arthur D. Little
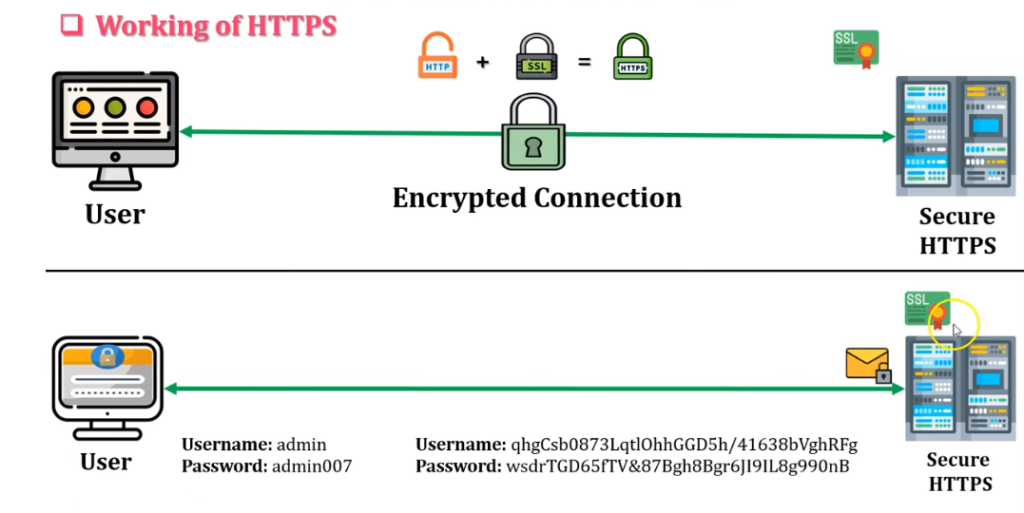
Decoding The Standard For Transferring Encrypted Data On The Web

What is the Difference Between ICT and IT? | CCI Training Center

Protecting Personal Data India's Digital Personal Data Protection Act

Do Your Online Security Practices Stack Up? | News and Updates | About ...
IGCSE ICT - Safety and Security - Ajiro Tech | PDF

internet security online, data protection concept, cybersecurity ...

Is your ICT environment secure? - HEAnet
IGCSE ICT - Safety and Security - Ajiro Tech | PDF

Protecting online information systems via the internet with encryption ...

Cybersecurity Tip #28: Secure your Internet of Things (IoT) devices ...

Our role in keeping your data safe | IG Wealth Management

Data Protection
Safety Issues on the Use of ICT including e-Safety Rules.pptx
Security of data and the internet Data protection using cybersecurity ...

What is Digital Security: Overview, Types, and Applications in Digital ...

Safeguarding digital assets and personal information with cybersecurity ...
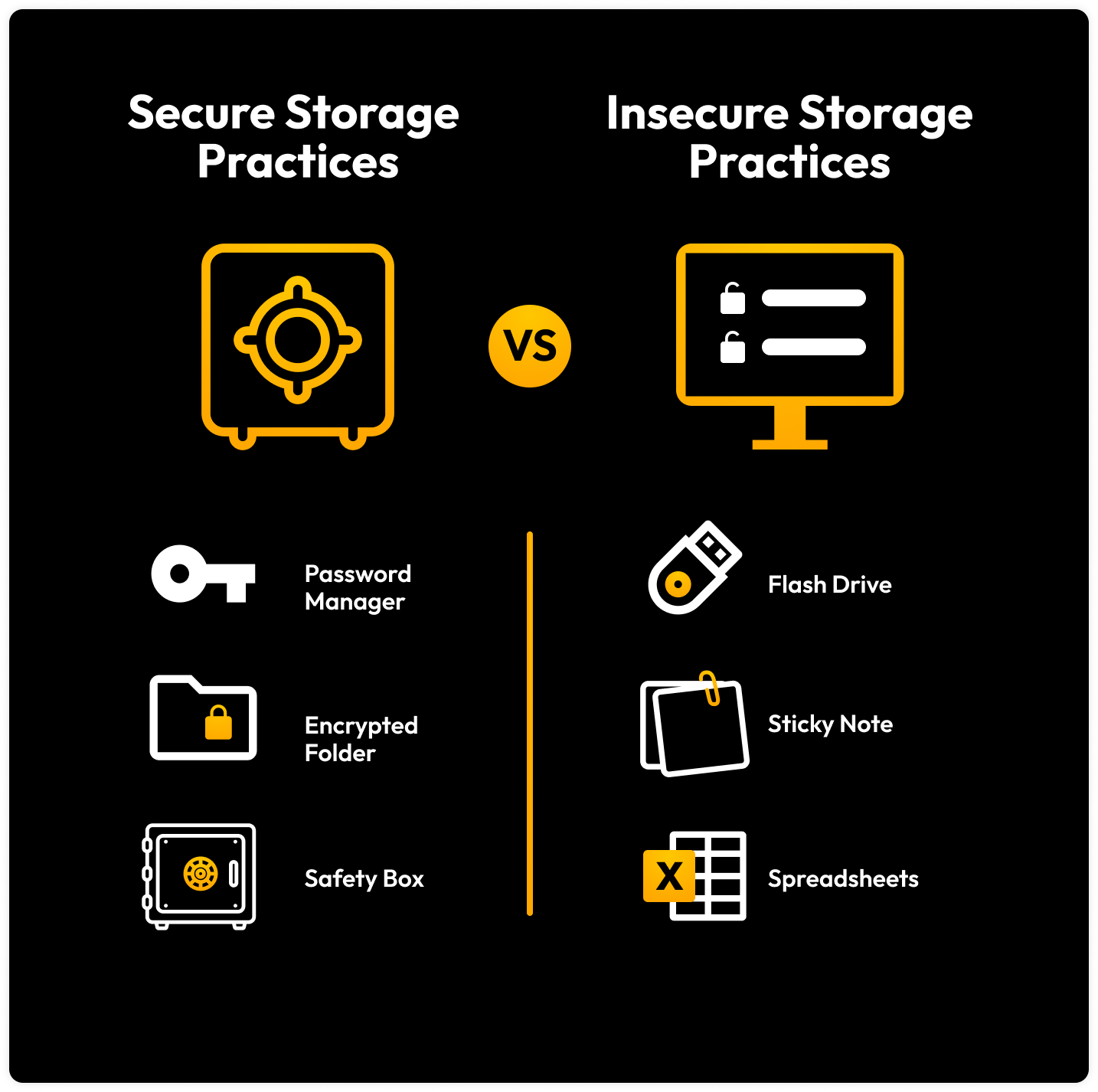
How Should Sensitive Information Be Stored?

Choosing the Right AI Development Company for Your Business

Network Security Checklist - 2026
Cyber Security Practices For Small Businesses

Why taking a layered approach delivers the best IT security protection ...
