Cybersecurity Tools and Technologies Business Studies Data Privacy

Cybersecurity Tools and Technologies (Business Studies, Data Privacy)

Cybersecurity Tools and Technologies (Business Studies, Data Privacy)

Cybersecurity and Data Privacy (Business Studies 10-LESSON BUNDLE)

Top 3 Cybersecurity Tools to Protect Business Data

Premium Photo | Cybersecurity and data protection in business ...

Cybersecurity and Data Privacy in E-Commerce (Business Studies) | TPT

Technologies and Cybersecurity Tools for Law Firms.

Cybersecurity and Data Privacy in E-Commerce (Business Studies) | TPT

Data Privacy & Cybersecurity PowerPoint and Google Slides Template ...
Cybersecurity And Data Protection In International Business ...
Advertisement Space (300x250)

Business technology privacy concept cyber security data ...

Premium Photo | Concept of business technology privacy data protection ...

Premium Photo | Cyber security and data protection business technology ...
Cybersecurity & Data Privacy | 211 Ontario

Emerging cybersecurity technologies you should know for business – Artofit

Cyber security data protection business technology privacy concept ...

Premium Photo | Cyber security and data protection business technology ...

Cyber security data protection business technology privacy concept ...

Best Cybersecurity Tools for 2025: Essential Solutions for Business ...
PPT - Privacy, Cybersecurity and Data Analytics PowerPoint Presentation ...
Advertisement Space (336x280)

6 Crucial Cybersecurity Technologies Every Business Needs
5 Best Cybersecurity Tools to Safeguard Your Data Now | ShoukhinTech

What Is Privacy Enhancing Technology? And How It Protects Your Data ...
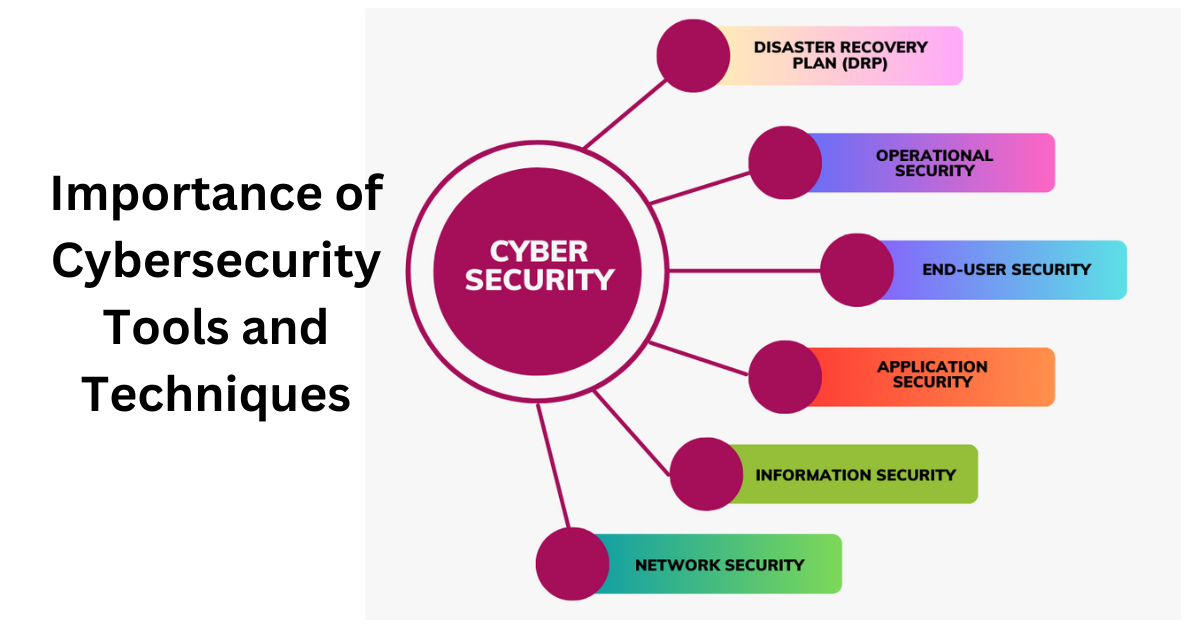
Importance of Cybersecurity Tools and Techniques - Blog.ICSS

Cyber Security Data Protection Business Technology Privacy concept ...

Premium Photo | Business technology privacy with cyber security data ...

Why Cybersecurity Must Start with Business Goals, Not Just Tech Tools ...

Premium Photo | Business technology privacy with cyber security data ...

Premium Photo | Cybersecurity Data Protection Business Technology ...

Corporate data protection cyber security privacy business internet ...
Advertisement Space (336x280)

Cyber security data protection business technology privacy concept ...

Cyber security data protection business technology privacy concept ...

Top Cybersecurity Tools Every Business Should Know About - aiotechnical ...

Cybersecurity And Data Protection: Essential Strategies 2024

Fortifying business technology safeguarding data privacy with cyber ...

Cyber security data protection business technology privacy concept ...

Cyber Security Data Protection Business Technology Privacy concept ...

Cyber Security Data Protection Business Technology Privacy concept ...

Internet business Technology and network concept Cyber security data ...

Top Cybersecurity Tools Every Business Should Use
Advertisement Space (336x280)

Cyber Security Data Protection Business Technology Privacy concept ...
Cyber Security. Data protection business concept on virtual screen ...

Premium Photo | Cyber Security Data Protection Business Technology ...

Top 12 Essential Cybersecurity Tools you must know in 2026
.jpeg)
Cybersecurity for Small Businesses - Sangfor Technologies

Cybersecurity Tools Archives - Global Tech Council

Best Cybersecurity Tools For Small Businesses - Shartega IT

Types of Cybersecurity Threats (Business Studies, Data Privacy) | TPT

Introduction to Cybersecurity (Business Studies, Data Privacy) | TPT

How to Choose the Right Cybersecurity Tools for Your Business: A
Advertisement Space (336x280)

Introduction to Cybersecurity (Business Studies, Data Privacy) | TPT

Data Privacy Vs Data Security: Data Protection Guide 2024

The Best Cybersecurity Tools for Cloud & On-Prem Environments

Cyber Security Data Protection Business Technology Stock Photo (Edit ...

Cyber Security Data Protection Business Technology Stock Photo ...

Premium Photo | Concept of cyber security, data protection, business ...

Premium Photo | Cyber Security Data Protection Business Technology ...

internet security and data protection concept, blockchain and ...

Cybersecurity for Small Business: 3 Proven Tools (AI, SIEM, EDR)

Premium Photo | Cyber Security Data Protection Business Technology ...
Advertisement Space (336x280)

Introduction to Cybersecurity (Business Studies, Data Privacy) | TPT

Cyber Security Data Protection Business Technology Stock Photo ...

Premium Photo | Concept of cyber security, data protection, and ...

Understanding Data Privacy (Business Studies, Cybersecurity) | TPT

Premium Photo | Cyber Security Data Protection Business Technology ...

Types of Cybersecurity Threats (Business Studies, Data Privacy) | TPT

Top Cybersecurity Trends and Strategies for Securing the Future | Gartner

Premium Photo | Cyber security data protection business technology ...
Top Books in Guide to Selecting the Right Cybersecurity Tools | S-Logix

Premium Photo | Cyber security data protection business technology ...

Premium Photo | Cyber Security Data Protection Business Technology ...

Premium Photo | Cyber Security Data Protection Business Technology ...

Cybersecurity Services - Generative AI Services & Data Analytics for ...

The Role of Cybersecurity in E-Commerce (Business Studies, Data Privacy)

Top 29 Cyber Security Tools - DataFlair
Top 16 Cyber Security tools You Must Know in 2025 - Sprinto

Top 10 Cyber Security Tools - Shiksha Online
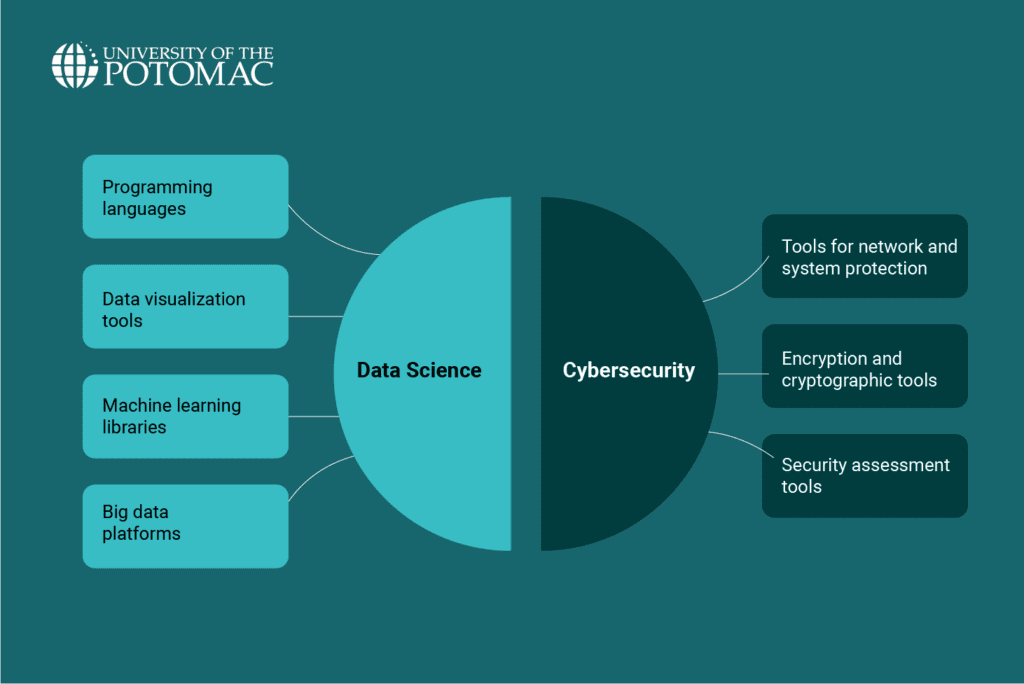
Data Science vs. Cybersecurity: Which Path to Take in 2025?

Top 8 Powerful Cyber Security Tools In 2025 - leed
The Role of Privacy-Enhancing Technologies in Cybersecurity.pdf

The Best Cybersecurity Assessment Tools: Top 5 Picks

Why Technology Convergence is the Future of Cybersecurity

TECH TALK: 3 Steps to Developing an Effective Cybersecurity Strategy ...

Helping to shape the RMIT Centre for Cyber Security Research and ...

The Role of Privacy-Enhancing Technologies in Cybersecurity.pdf

The Evolution of Cyber security Threats and Protection - MaPuPa

Exploring the Impact of AI-Based Cyber Security Financial Sector Management

Cybersecurity-&-Data-Privacy-for-Indian-Businesses_-Strategies ...
