Sub Plan No Prep Puzzles Computer Science Cybersecurity MitM Attack

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | MitM ...

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | MitM ...

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | Hackers

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | Malware

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | Malware

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | Malware

Sub Plan | No Prep | Puzzles | Computer Science | Cybersecurity | Hackers

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

Sub Plan | No Prep | Computer Science | Cybersecurity | Cyberbullying

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months
Advertisement Space (300x250)

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

Sub Plan | No Prep | Computer Science | Cybersecurity | Hackers | TPT

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

Sub Plan | No Prep | Computer Science | Cybersecurity | Password Security

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

Sub Plan | No Prep | Computer Science | Cybersecurity | Hackers | TPT

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

No Prep | Sub Plan | Computer Science | Cybersecurity Bundle | 2 Months

Sub Plan | No Prep | Computer Science | Cybersecurity | Phishing
Advertisement Space (336x280)

Sub Plans | No Prep | Computer Science | Cybersecurity | A | TPT

Sub Plans | No Prep | Computer Science | Cybersecurity | C | TPT

Sub Plan | No Prep | Computer Science Semester Bundle | 700+ Pages | 61 ...

Sub Plans | No Prep | Computer Science | Cybersecurity | A | TPT

Sub Plan | No Prep | Computer Science | Artificial Intelligence Bundle ...

Sub Plan | No Prep | Computer Science Semester Bundle | 700+ Pages | 61 ...

Sub Plan | No Prep | Computer Science | Artificial Intelligence Bundle ...

Sub Plan | No Prep | Computer Science | Email Viruses by All 4 Computer ...

Sub Plans | No Prep | Computer Science | Cybersecurity | Network Security

Sub Plans | No Prep | Computer Science | Cybersecurity | Network Security
Advertisement Space (336x280)

Sub Plans | No Prep | Computer Science | Cybersecurity | Network Security

Sub Plan | No Prep | STEM | Computer Science | Robots | 1 Week | TPT

Science Article: Cybersecurity | No Prep | Sub Plan | Social Media ...

Sub Plan | No Prep | Computer Science | Programming | Arrays | TPT

Sub Plans | No Prep | STEM | Computer Science | Engineering ...

No Prep Technology & Computer Science Sub Plans by Computer Creations

Computer Science Semester Bundle of No Prep & Sub Plans | 300 Pages ...

No Prep Technology & Computer Science Sub Plans by Computer Creations
![No Prep | Cybersecurity [phishing] by All 4 Computer Science | TPT](https://ecdn.teacherspayteachers.com/thumbitem/Cyber-Security-phishing--11275671-1725263516/original-11275671-4.jpg)
No Prep | Cybersecurity [phishing] by All 4 Computer Science | TPT

Sub Plan | No Prep |Computer Science|Artificial Intelligence|AI in ...
Advertisement Space (336x280)

Emergency Sub Technology & Computer Science Lesson Activities (No Prep ...

No Prep | PowerPoint | Computer Science | Cyber Spies | Quiz | Cyberattacks

NO PREP Emergency Science Sub Plans (Monthly) - Flying Colors Science

No Prep | Computer Science | Cyber Security Bundle | 4 Quizzes | TPT

No Prep Case Study | Computer Science | Cybersecurity| Android Security ...
No Prep Emergency Sub Plans: Keep Students Engaged
Emergency Computer Science Sub Plans with Choice Boards for Middle School

Computer Science and Cybersecurity Puzzle | STEM | Cryptography ...
Complete Computer Science & Cybersecurity Educator Bundle by CTE Warehouse

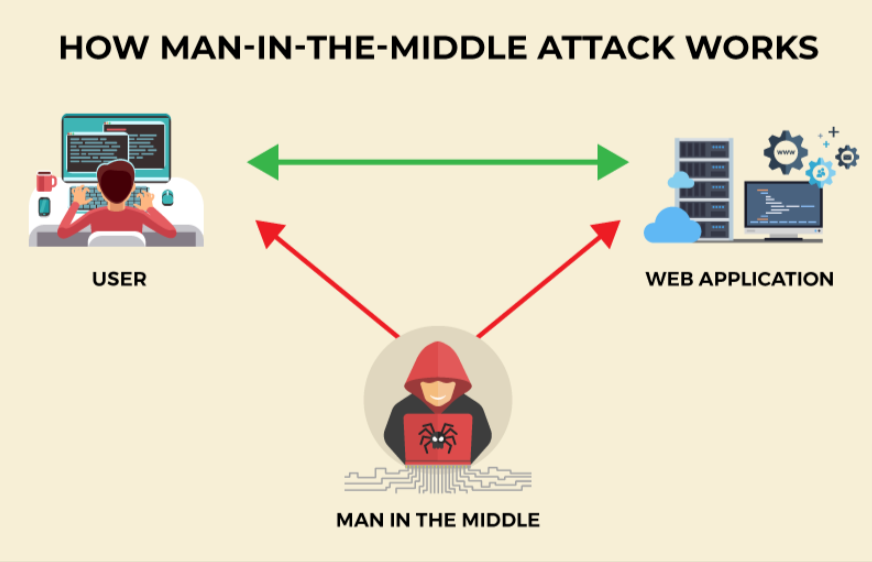
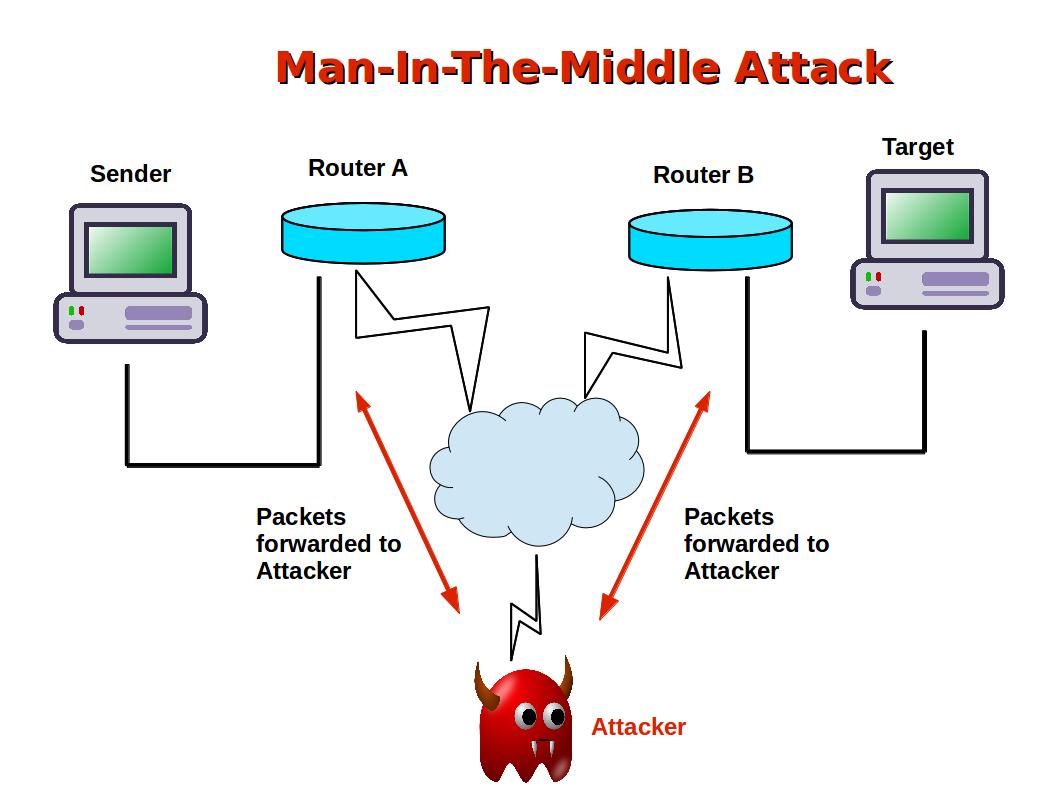
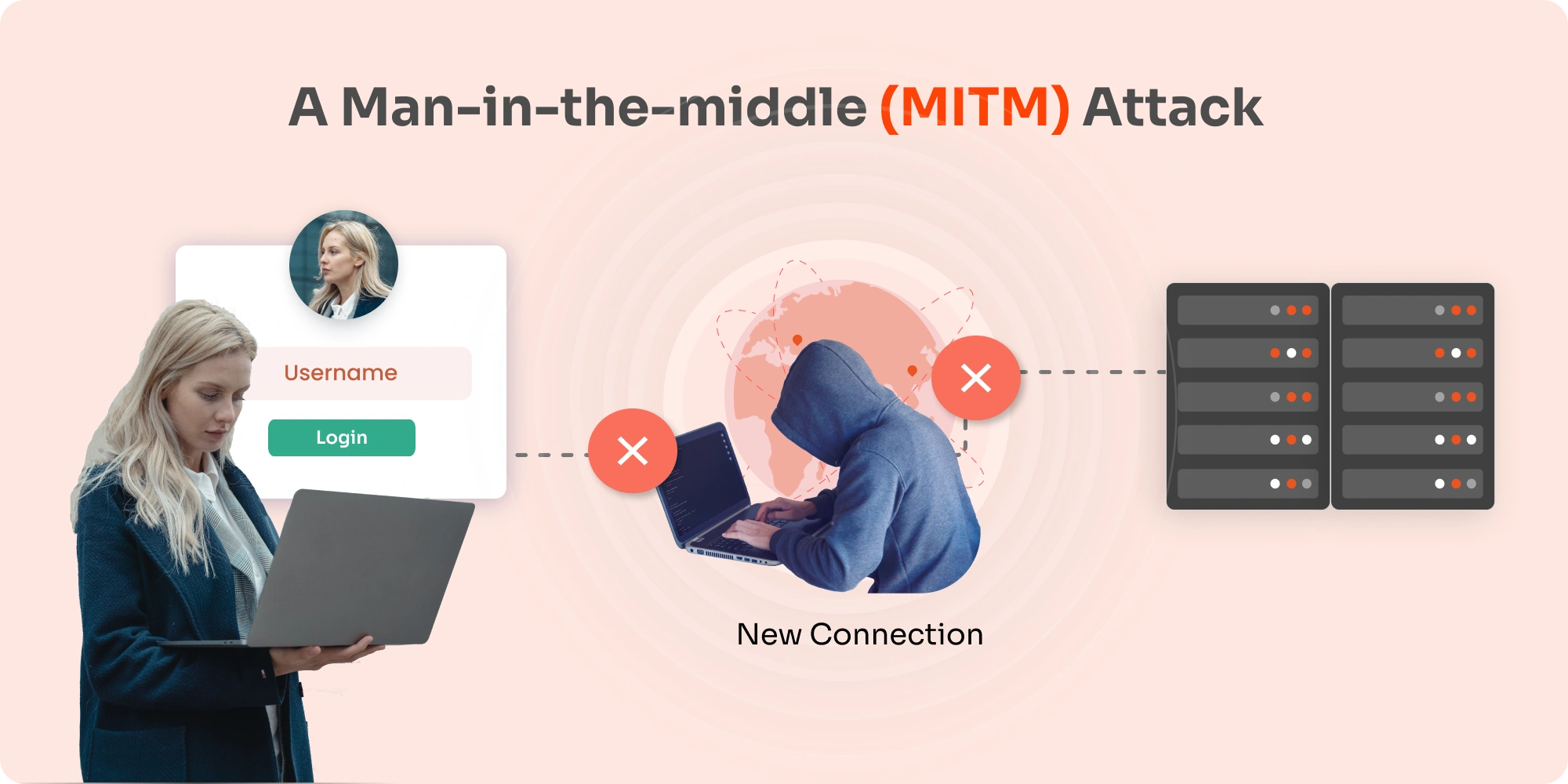
What is MITM Attack? in 2025 | Learn computer science, Networking ...
Advertisement Space (336x280)
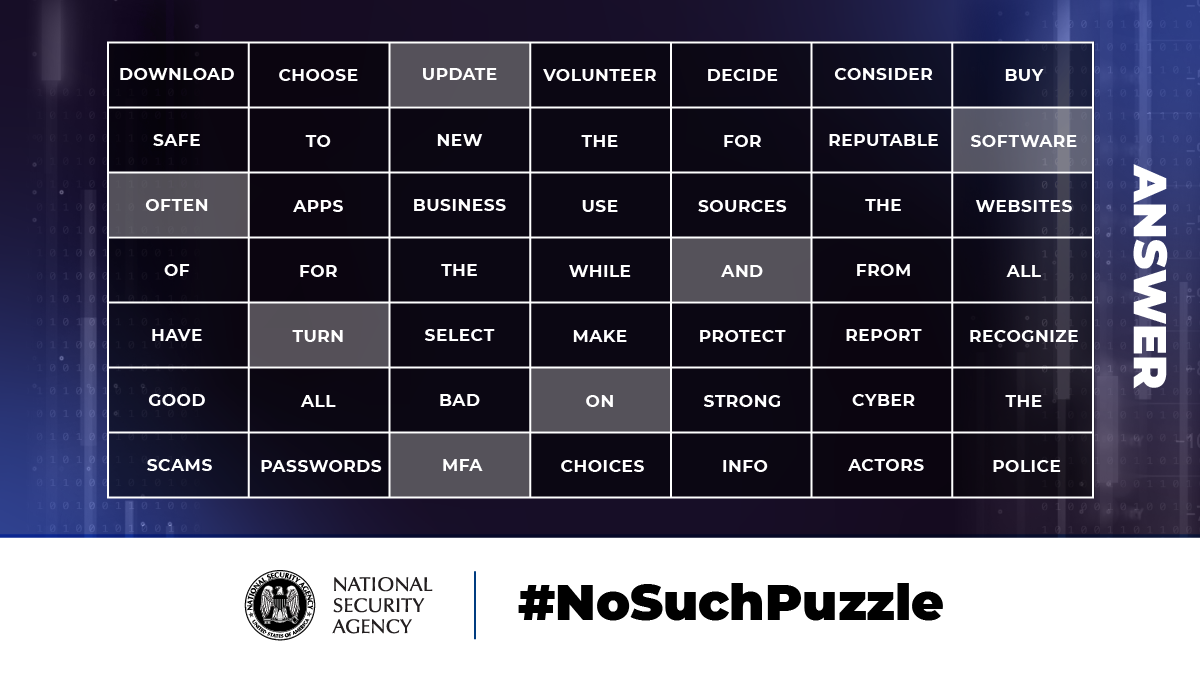
No Such Puzzle: Cybersecurity Awareness Month > National Security ...
Cyber Security Word Search Puzzle with Coloring | Computer Science ...
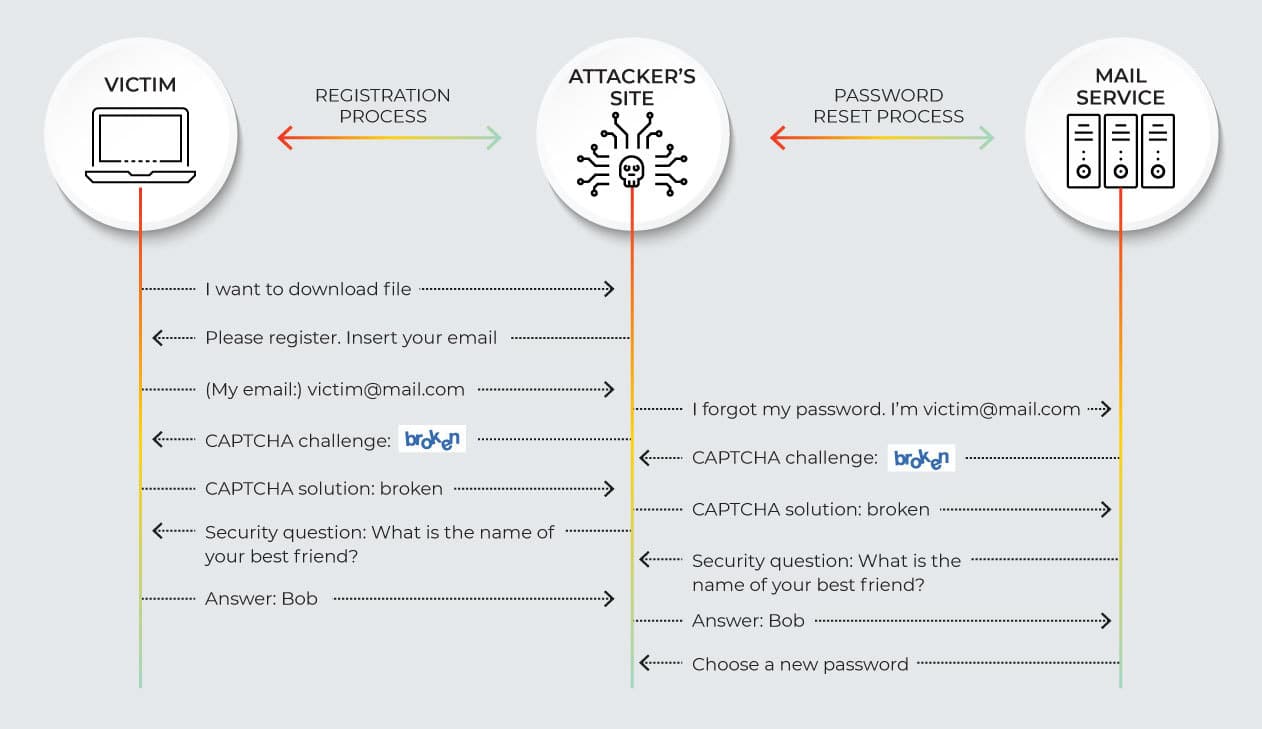
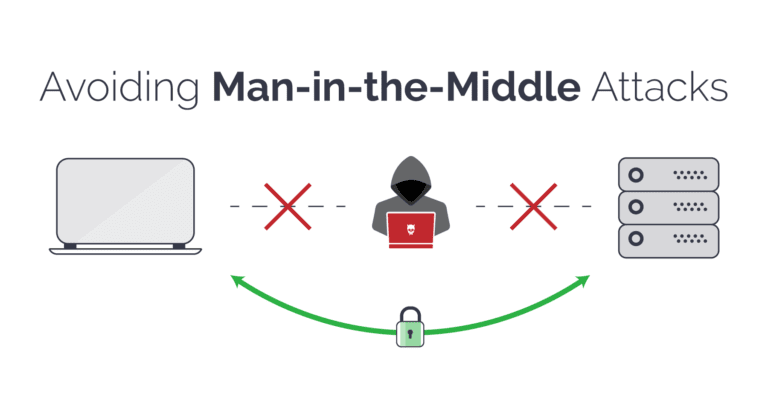
11 MitM Attack Prevention Practices for Brands | Memcyco

Cybersecurity: Crash Course Computer Science #31 - YouTube
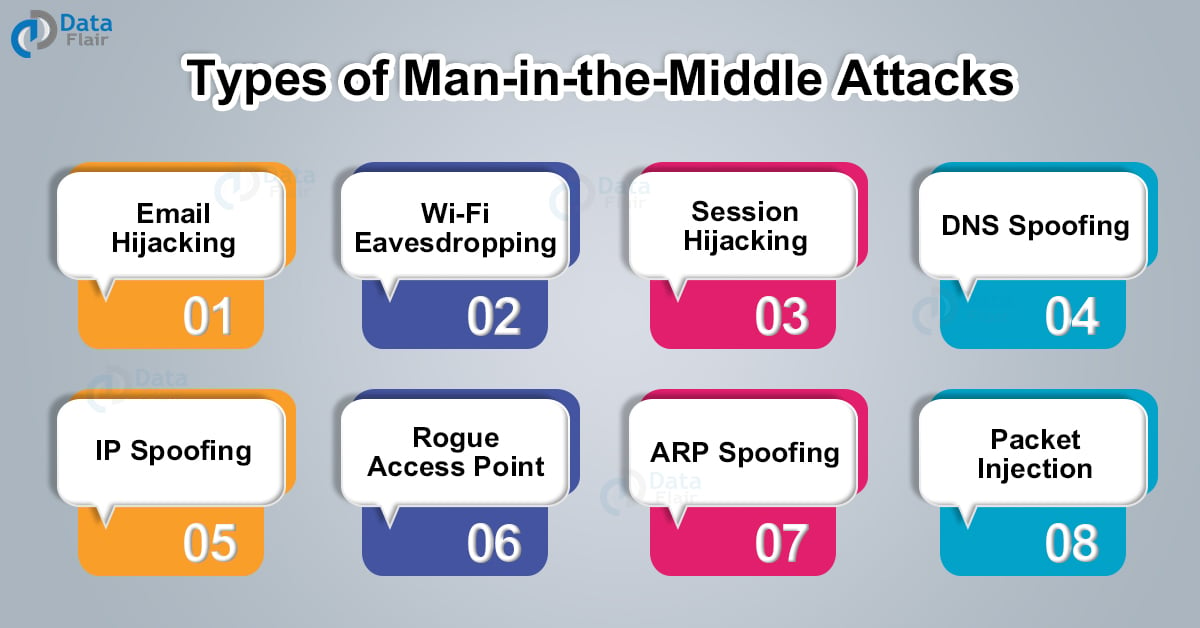
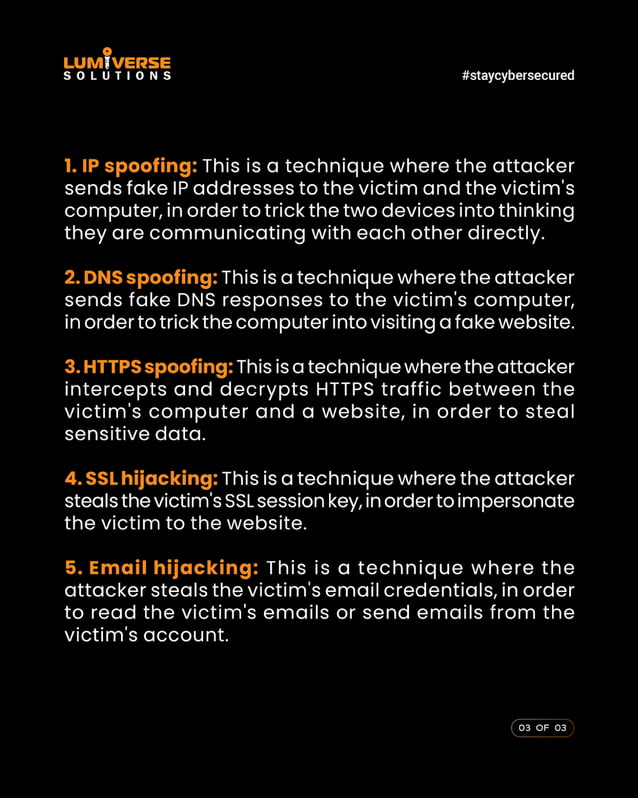
MITM (Man in the Middle) Attack | Types and Prevention - DataFlair

Man in the Middle Attack | How Can You Prevent MITM Attack? | Cyber ...

MSc Computer Science with Cyber Security - Sheffield Hallam University

What is MITM Attack and How to Prevent from MITM Attack? | 'Monomousumi'
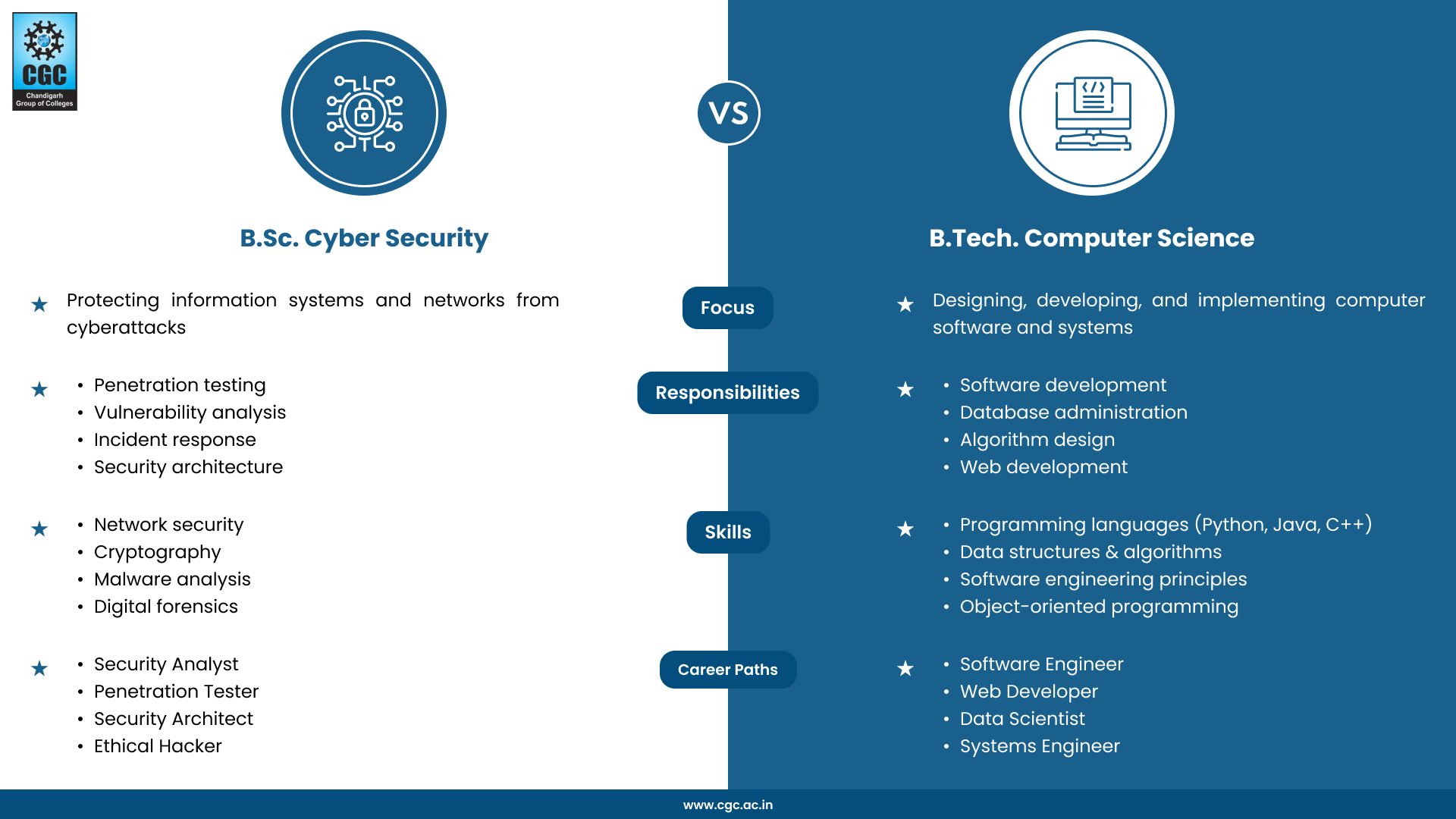
BSc Cyber Security vs BTech Computer Science What's the Difference?
Man in the Middle (MITM) Attacks Explained | Baeldung on Computer Science
Advertisement Space (336x280)

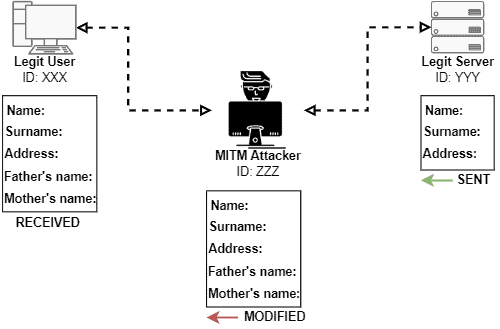
MITM Attack by hacker on user login credentials | Download Scientific ...
Computer Security and PGP: What is a Man-In-The-Middle Attack

1 MiTM attack scenario. | Download Scientific Diagram
What Is Computer Science Cyber Security? A Vital Guide - ED Tech RCE

Premium Vector | Mitm attack man in the middle cyberattack active ...

Cybersecurity Unit 3 PBL Bundle: Threats and Attack Surfaces | TPT

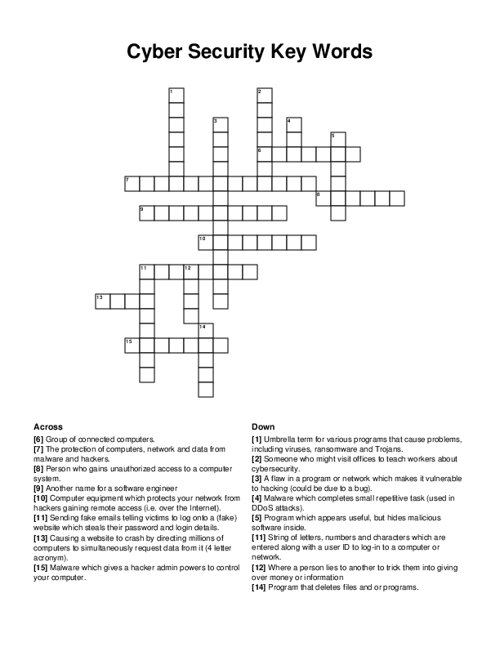
CYBERSECURITY word scramble puzzles worksheets activities by PUZZLES BY ADO
Cryptography: Encryption Code-Breaking Cybersecurity (NO PREP Sub) 6x ...

Cybersecurity Unit 3 Bundle: Threats and Attack Surfaces | TPT
Man In The Middle Attack | MITM Attack | MITM | PDF

Description diagram of an MITM attack | Download Scientific Diagram

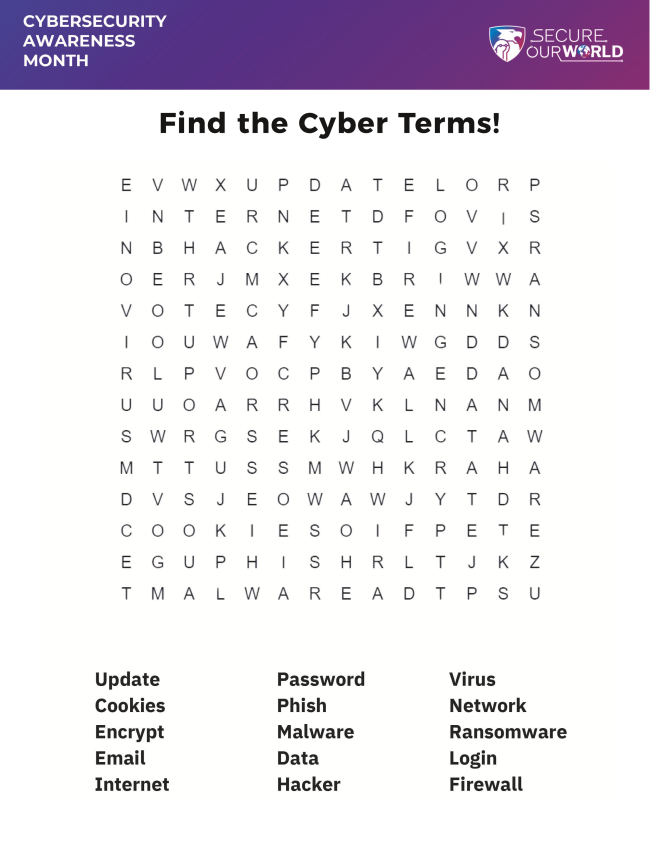
Secure-Our-World-Cybersecurity-Awareness-Month-Puzzles | PDF | Computer ...

Cybersecurity Word Search Puzzle Worksheet Activity | Teaching Resources
How to Solve the Cybersecurity Puzzle » Resources | GovLoop

9 Sub Plans ideas | sub plans, emergency sub plans, choice boards
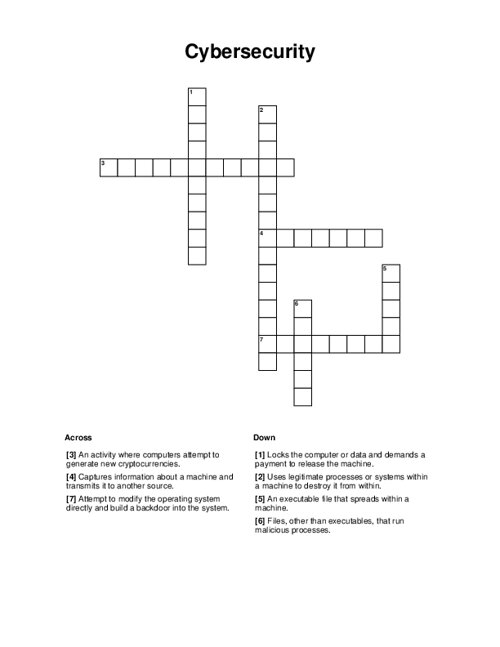
Cybersecurity Crossword Puzzle
Cybersecurity Friday
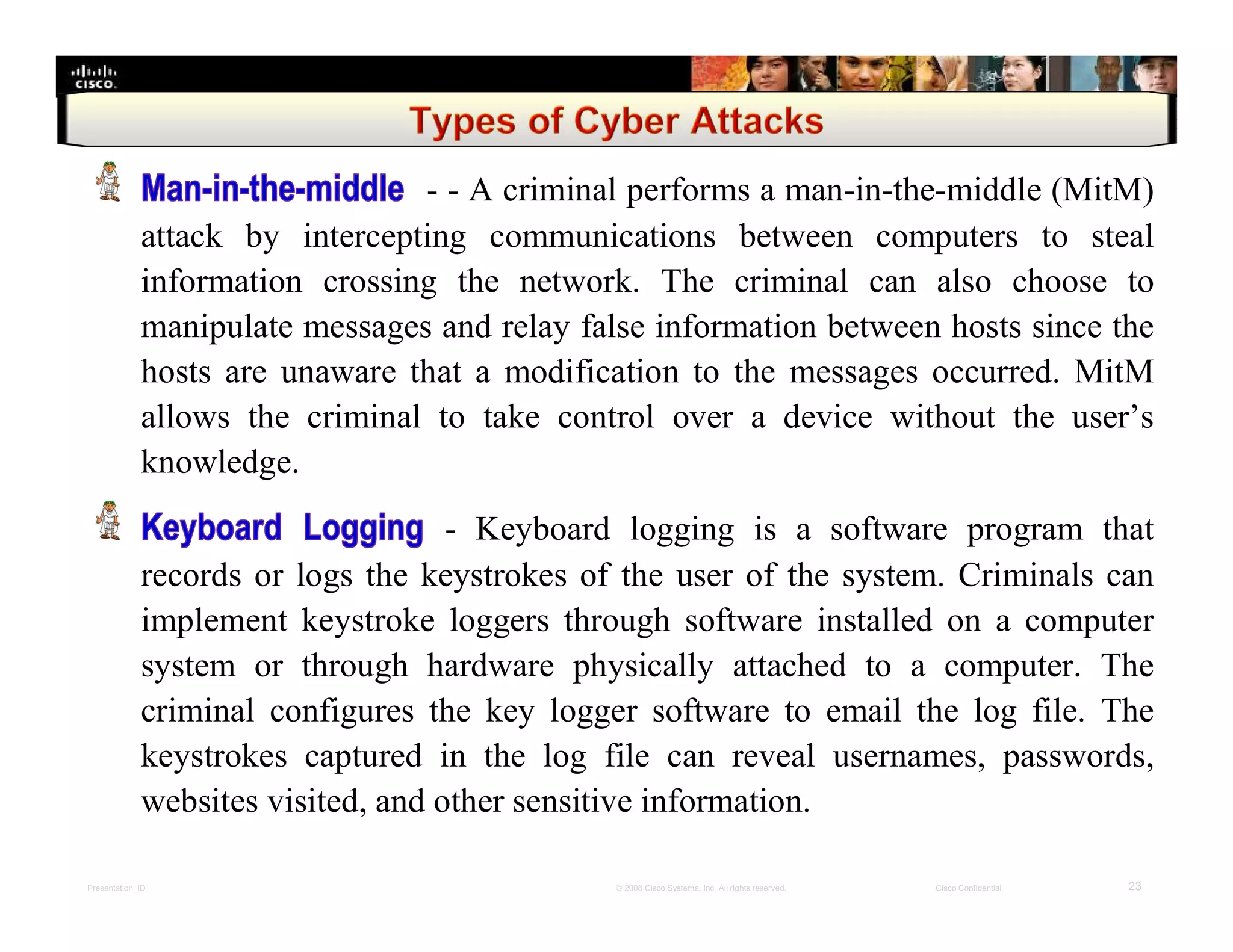
Cisco cybersecurity essentials chapter 3 | PDF
Bridge the Cybersecurity Skill Gap with Managed Services
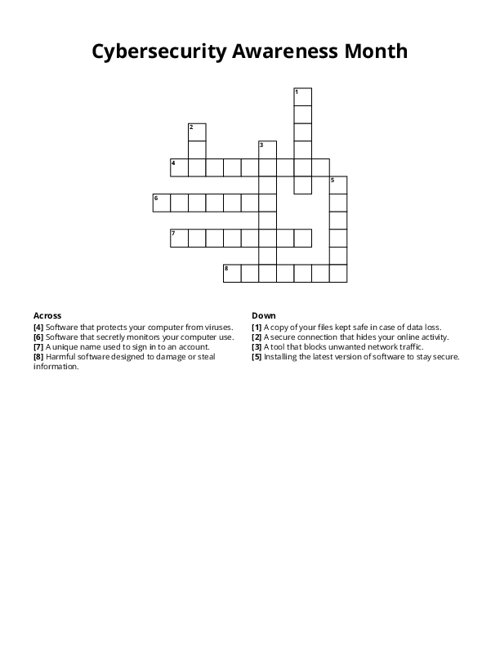
Cybersecurity Awareness Month Crossword Puzzle
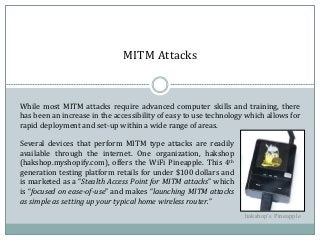
OPSEC - MITM Attacks.pptx

Man in the middle attacks | Learn computer science, Computer security ...

(PDF) Simplified Modeling of MITM Attacks for Block Ciphers: New ...

Cybersecurity Crossword Puzzle - WordMint

Performing Mitm Attacks Within A Wlan | PDF | Transport Layer Security ...
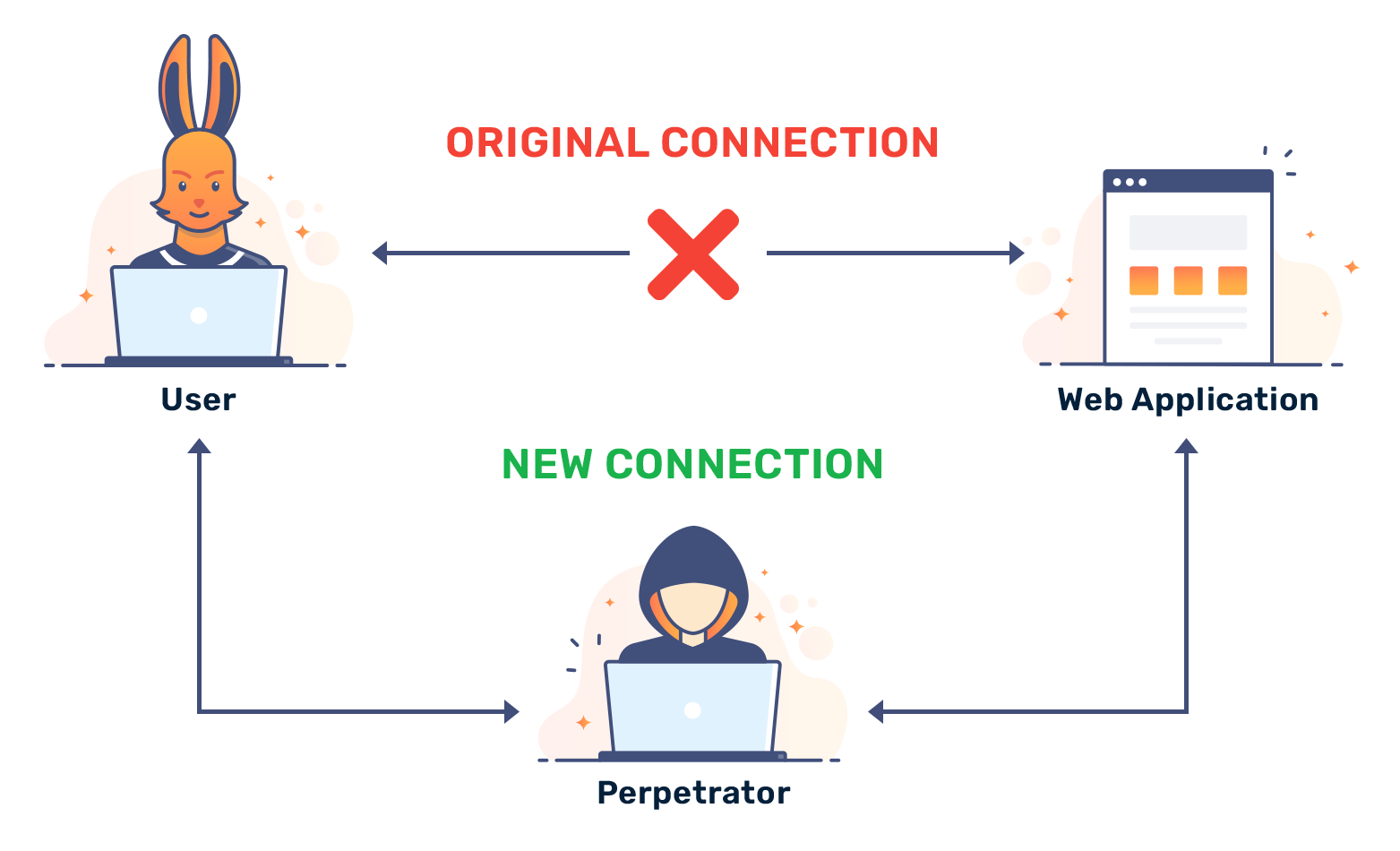
What are Man In The Middle (MITM) Attack and how do they work?
Cybersecurity _ Man in the Middle (MITM) Attack.pdf
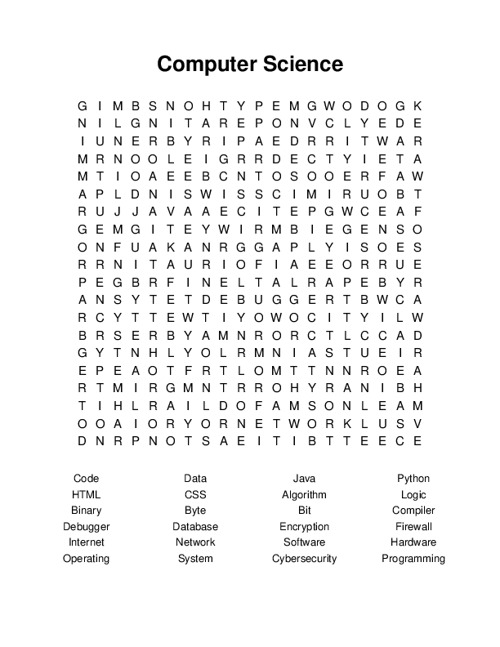
Cybersecurity Word Search

Cybersecurity Basics Crossword - WordMint

Amazon.com: 101 Cyber-Security Themed Learning Word Puzzles ...

Cybersecurity _ Man in the Middle (MITM) Attack.pptx
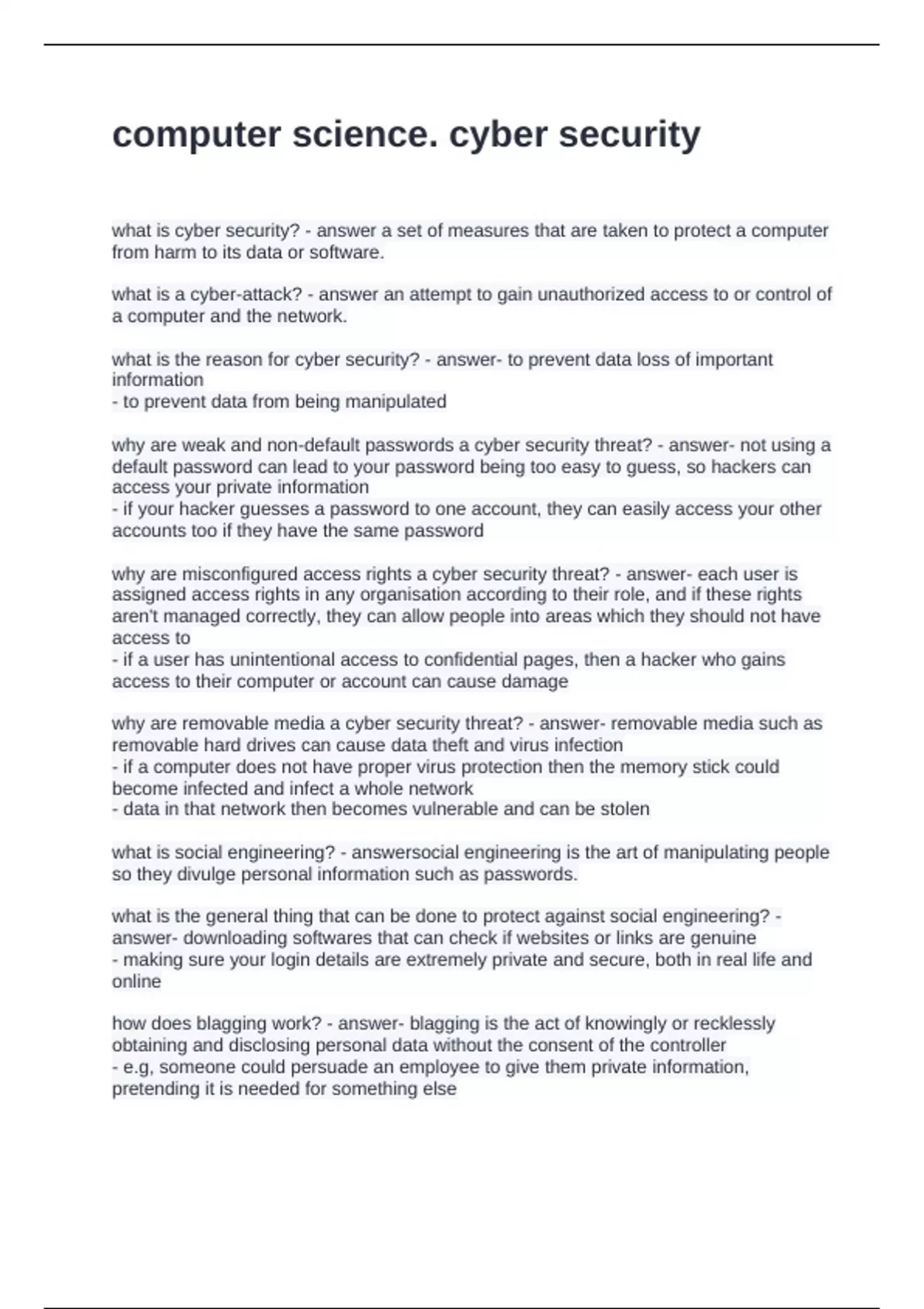
computer science. cyber security questions and answers 2024 - Cyber ...
Preventing MITM Attacks: Proven 2022 Methods - CyberProof
What is a Man in the Middle Attack? MitM Types & Prevention

MITM Attacks - Cyber Security Complete Course - Class 13 | Azad ...
Cybersecurity _ Man in the Middle (MITM) Attack.pptx

Cybersecurity _ Man in the Middle (MITM) Attack.pptx
Cybersecurity _ Man in the Middle (MITM) Attack.pptx

What Is a Man in the Middle Attack? MITM Explained

What is a Man in the Middle Attack? MitM Types & Prevention

One Step Ahead of Hackers: Mitigating MitM Attacks | Blog
Avoiding man-in-the-middle (MITM) attacks | Invicti

Applying Puzzle-Based Learning to Cyber-Security Education
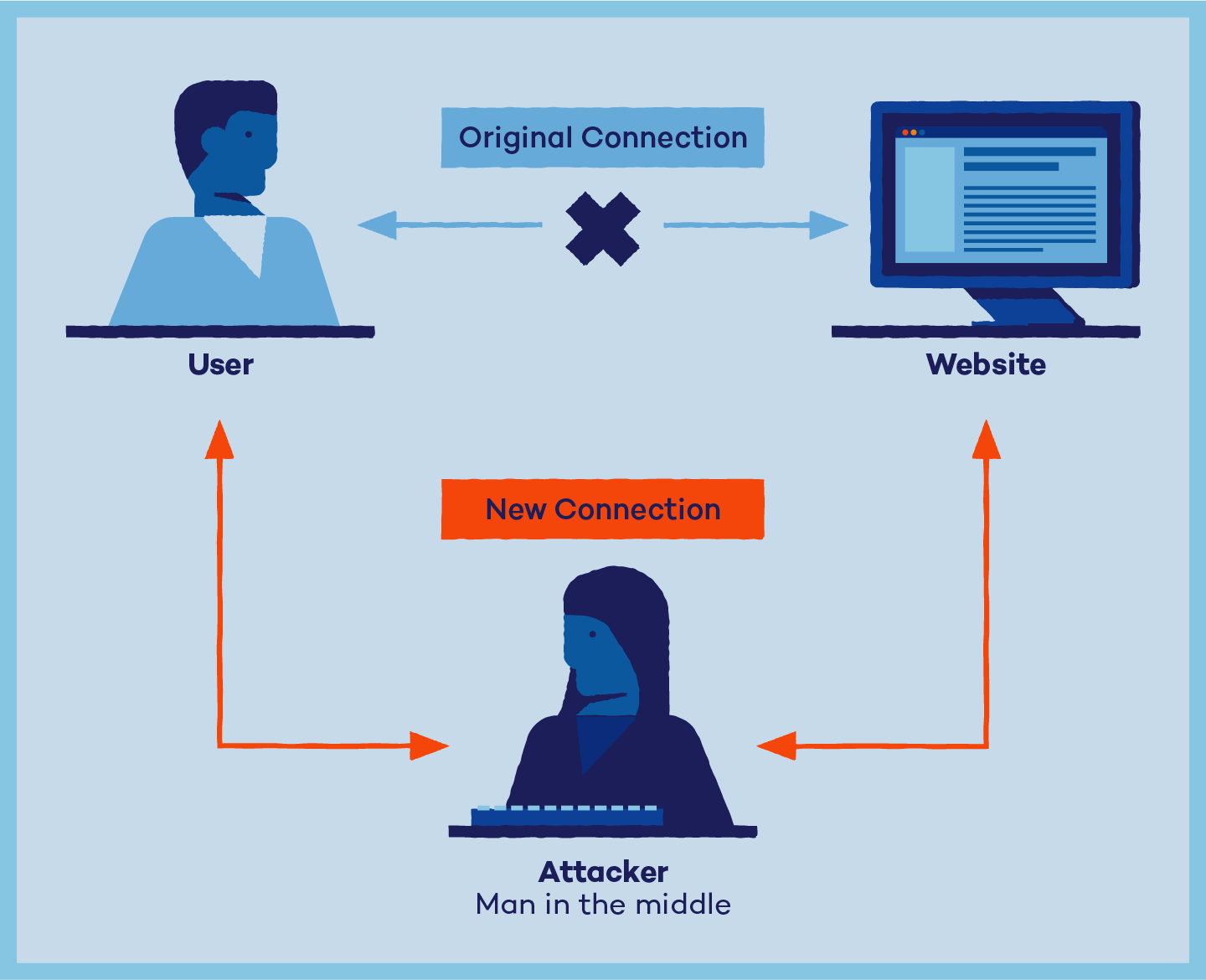
What Is a Man-in-the-Middle (MITM) Attack? Definition and Prevention ...

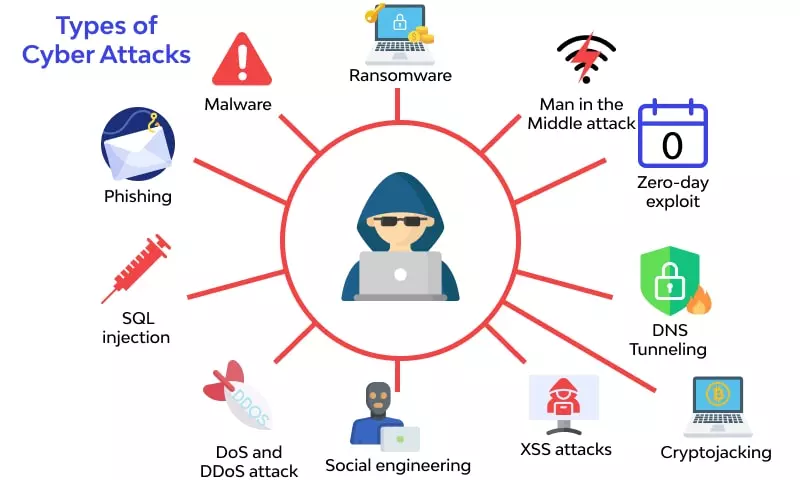
What is a Cyber Attack? Types, Effects & Prevention

What Is SIEM? | Definition, Tools, and Security Benefits
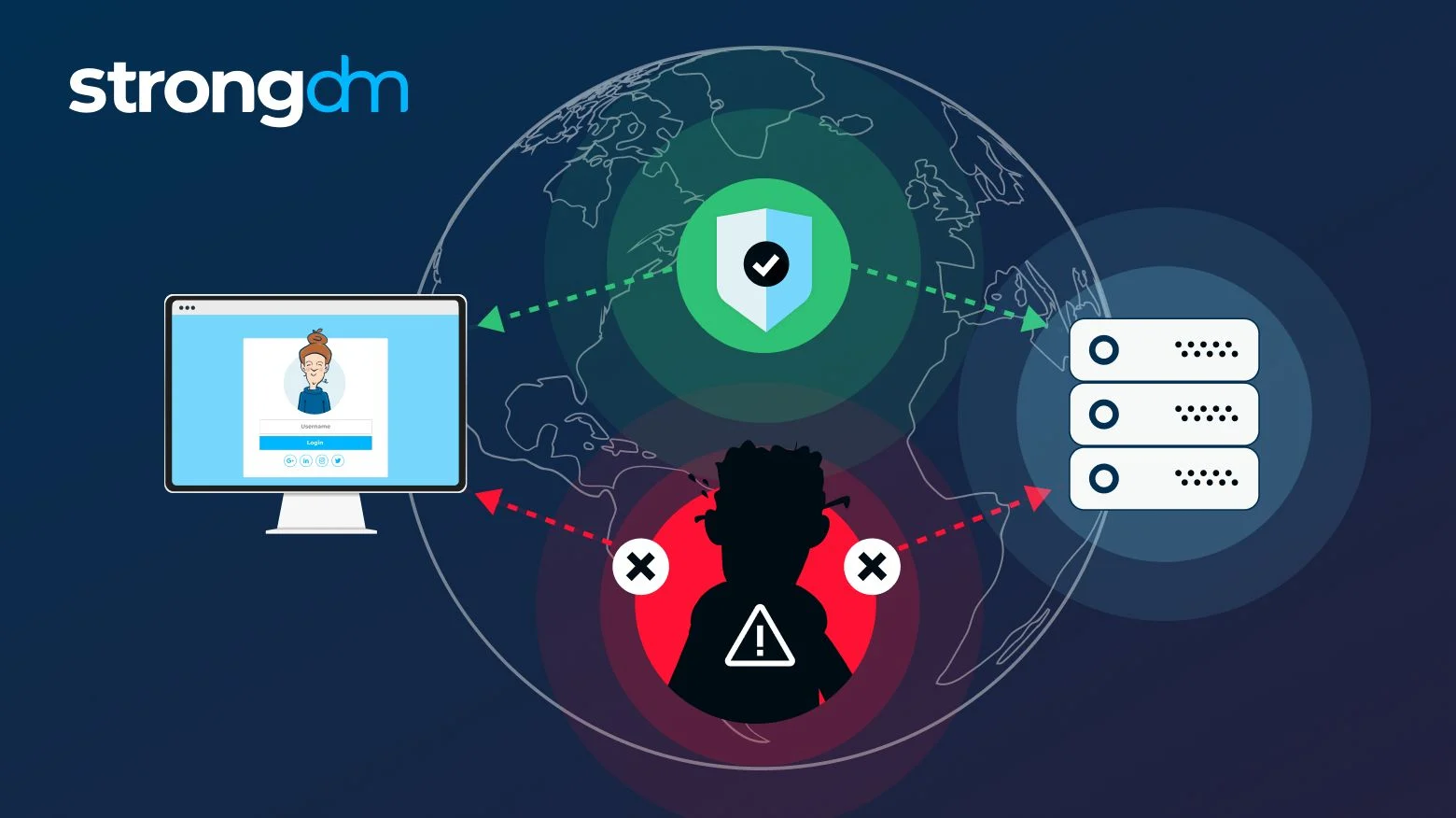
Man-in-the-Middle (MITM) Attack: Definition, Examples & More | StrongDM

Cyber Security puzzle & printable jigsaw

What Is a Man-in-the-Middle Attack? | Examples & Prevention Tips

Cyber-security Basics Crossword - WordMint

Man-in-the-Middle Attacks: Risks, Detection, and Defense Strategy ...

(PDF) Guide for designing cyber security exercises

Cyber Kill Chain vs MITRE ATT&CK: Best Comparison (2025)
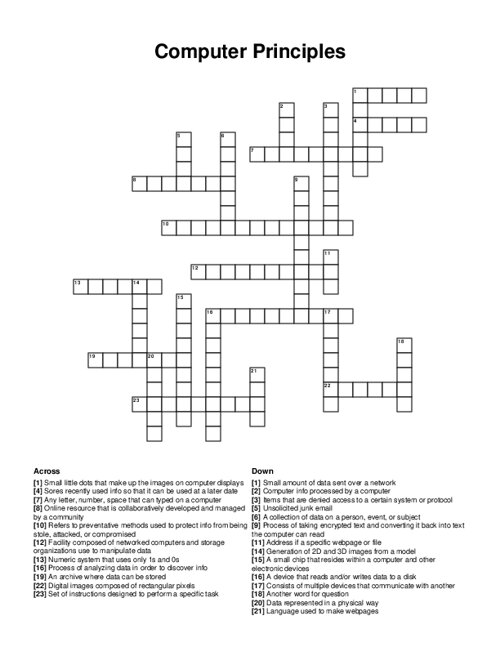
Cyber Security Crossword Puzzle
Technology Crossword Puzzle
What is Access Provisioning in Identity Management?
![Cyber Security Activity Worksheets [3 Different Puzzle Types with Answers]](https://ecdn.teacherspayteachers.com/thumbitem/Cyber-Security-Activity-Worksheets-3-Different-Puzzle-Types-with-Answers--10707181-1702846323/original-10707181-1.jpg)
Cyber Security Activity Worksheets [3 Different Puzzle Types with Answers]

Spear‑Phishing, Whale Phishing, MITM: A Beginner’s Guide to Cyber ...

Spear‑Phishing, Whale Phishing, MITM: A Beginner’s Guide to Cyber ...
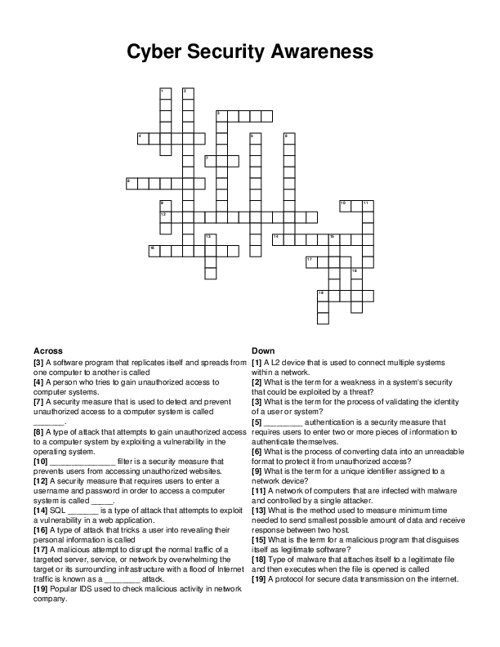
Cyber Security Awareness Crossword Puzzle
